For the past few weeks I’ve really been looking into Intune and how to use it in a hybrid scenario with ConfigMgr. In my home lab, I’ve got AADSync installed on my Domain Controller (DC01) that is synchronizing my on-premise Active Directory with my Azure Active Directory tenant (configmgrse.onmicrosoft.com).
Problem
Although, today I ran into my first error when using AADSync (Azure Active Directory Synchronization Services). I noticed this because I made a change to an on-premise user account and it wasn’t synchronized to my Azure AD.
Troubleshooting steps
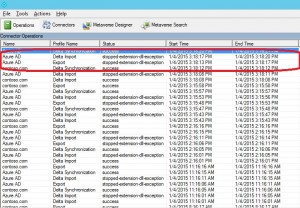
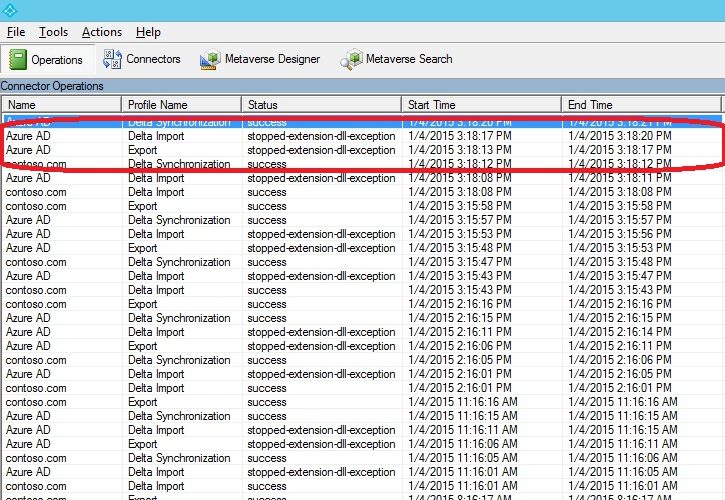
First of I went to check if there were any errors in the Synchronization Service Manager tool, and there I was able to confirm my suspicions. I indeed had an error when synchronizing to my Azure AD. The Operations view of the tool presented me with this information for the Connectors:
My next step was to naturally open up the Event Viewer to see if there were any errors in the Application log, and I found this:
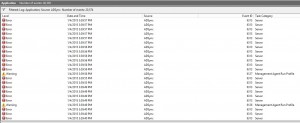
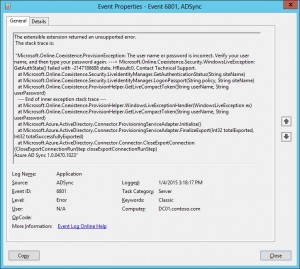
Most of these errors turned out to be problems caused by an error when creating performance counters for a management agent. Not really the information I was looking for (I’d need to dig into those errors though). I was almost about to give up when I hit one of the error events with event ID 6801. This event was indeed from the AD Sync source and could be what I was looking for. The error message presented an obvious problem:
Microsoft.Online.Coexistence.ProvisionException: The user name or password is incorrect. Verify your user name, and then type your password again
This is what the whole event looked like:
It then occurred to me what the problem could be. When I initially configured my Azure AD tenant, I had not verified any public domain. And before I started configuring the hybrid configuration between Intune and ConfigMgr, I’d already installed AADSync and set it up to use a Global Administrator called [email protected]. This account was later changed to [email protected] after I had verified my public domain.
Resolution
So in order to resolve this error (if you may call it that), it’s pretty simple.
1. Open Synchronization Service Manager located in C:\Program Files\Microsoft Azure AD Sync\UIShell (the executable file is called miisclient.exe).
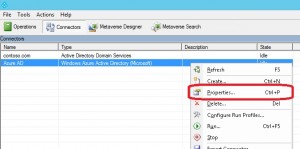
2. Click on the Connectors button, right-click on your Windows Azure Active Directory connector, in my lab environment its called Azure AD, and choose Properties.
3. Click on Connectivity in the left pane and configure the correct Global Administrator account for this connector. In my case I had to change from [email protected] to [email protected]:
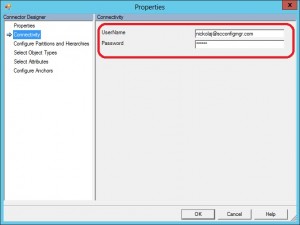
4. Click OK to save your modification to the connector.
5. Either run the Azure AD Sync Scheduler task located in the root of Task Scheduler or run the executable manually (C:\Program Files\Microsoft Azure AD Sync\Bin\DirectorySyncClientCmd.exe).
Once the Import, Synchronization and finally Export steps have completed, we can see that the synchronization to Azure AD once again is working as expected:









Great article! Thanks!
Thanks. In my case I had to reset the password in O365, and enter the new one in the Properties dialog. Then it worked again!