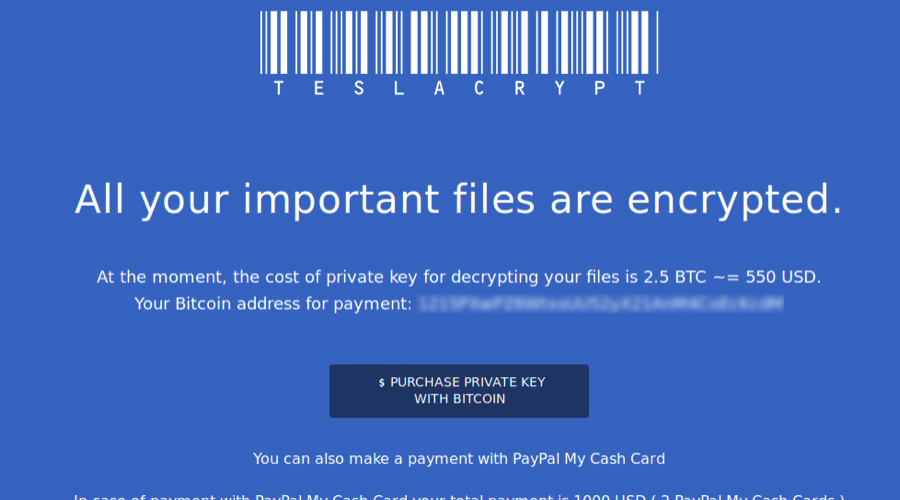
Ransomware is big business at present and like the viruses of the mid and late 90’s, it will probably be with us for quite a while. The fact of the matter is that ransomware is a multi million dollar industry and without adequate protection and more importantly backups, it can leave your business at a sizable risk from which you might not have the financial or technical abilities to recover from.
Over the past number of years we have seen continued reports in the media about companies, universities and individuals falling fowl of this menace. In January of this year news broke that a college had paid over $28,000 to restore files (https://www.zdnet.com/article/la-school-caves-in-pays-28000-ransom-to-restore-infected-systems/) and the list will continue to grow unless we put into place processes to help us protect our files.
Given this I was reminded recently after reading Nicolai Henriksen’s book on Microsoft System Center Endpoint Protection that from a server perspective we can make use of the File Server Resource Manager role to create file screen lists based on known ransomware file type extensions.
So lets first of all run through how this is done and then lets automate the entire creation process across multiple servers in your environment in the form of a Configuration Baseline in SCCM.
Installing the File Server Resource Manager
FSRM has been around with us for quite a few years now and the majority of administrators would have used it at some stage to either report on file type usage on their servers or to use it to block files based on file extensions (such as MP3, M4a etc).
To install the FSRM role you can use either the Server Manager GUI – Add Roles and Features or my preference (as should yours be by this stage) is to use PowerShell.
 Adding FRSM Role – Add Roles and Features
Adding FRSM Role – Add Roles and Features
 Adding FSRM Role – PowerShell
Adding FSRM Role – PowerShell
The FSRM Console
Once the service is installed you can open the console by running FSRM.msc or selecting it from Administrative Tools. The File Screening Management section is the section we will focus on for the purpose of this post.
 FSRM Console
FSRM Console
Within the File Screening Management section you will see various File Screen Templates and Groups which are available out of the box. So lets run through how to create a File Screen Template based on known ransomware file types;
Setting Up A File Screen
- Create a new file group by right-clicking on File Groups and selecting “Create File Group“. For the purpose of this post we will call it “CryptoExtensions” and we will add file extensions contained within the text file here : FileExtensions
- Now create a new File Screen Template which will hold the settings for monitoring / blocking and alert/event actions to be carried out if a match is detected. Right click on File Screen Templates and go to “Create File Screen Template”
- Under the Settings tab select “Active Screening” and select the “CryptoExtensions” file group from the list of available groups

- Under the E-Mail Messages tab enter an email address, subject and message body similar to the one in the below example

- Under the Settings tab select “Active Screening” and select the “CryptoExtensions” file group from the list of available groups
- Create a new File Screen by right clicking on “File Screens” and selecting “Create File Screen“. Enter the path you would like to protect and select the “CryptoExtensions” template.

- Specify SMTP Server Details by right clicking on “File Server Resource Manager” and selecting “Configure Options“

At this stage you now have an additional means of protecting your network from ransomware. So just repeat that on all of the file servers in your environment and you have peace of mind.. Wait? I have to do this for all my servers?? This is going to take ages!..
Automate The Process With SCCM CB
Obviously creating file screens across your organisation could take quite a while, so unless you are really free to do so lets look at automating the process with a Configuration Baseline in SCCM. In fact lets automate the entire process of adding the role, creating the file screens, adding the SMTP server details and furthermore lets report on whether or not the action has been successful on our File Servers.
Update – 23/3/2017
Following feedback, I have modified the script to get a list of file extensions from a text file on a network share. The script will now update the extension list on your file servers following any additions to this text file on the next Configuration Baseline scheduled check.
Configuration Item
- Open the SCCM console and expand the Compliance Settings section
- Right click on Configuration Items and select Create Configuration Item
- Give the CI a name of your choice
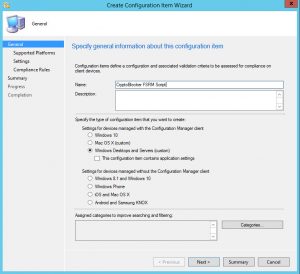
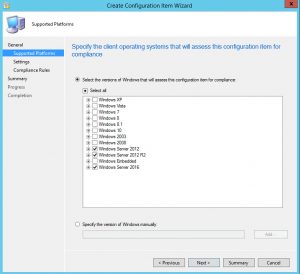
- Select Windows Server 2012 – 2016
- Click on “New“, enter a name and select Script as the Setting Type and Boolean as the Data Type
- Click on “Edit Script” under the “Discovery Script” section and paste in the following;
function CryptoBlocker { # Email Sever Settings $SMTPServer = "YOURSMTPSERVER" $SMTPFrom = "$env:COMPUTERNAME@YOURDOMAINNAME" $SMTPTo = "Admin@YOURDOMAINNAME" $AdminEmail = "Admin@YOURDOMAINNAME" # Get Ransomware Known File Types $CryptoExtensions = Get-Content "\\UNCFILESERVERPATH\FileExtensions.txt" # Import Server Manager PS Module Import-Module ServerManager # Install FSRM Role if required if ((Get-WindowsFeature -Name FS-Resource-Manager).InstallState -ne "Installed") { Install-WindowsFeature -Name FS-Resource-Manager -IncludeManagementTools | Out-Null } # Install Cyrpto Extension Monitoring / Blocking if ((Get-FSRMFileScreen).Description -notcontains "Crypto Extension Monitoring") { # Set FSRM Email Settings Set-FSRMSetting -AdminEmailAddress $AdminEmail -SMTPServer $SMTPServer -FromEmailAddress $SMTPFrom # Create FSRM File Group New-FSRMFileGroup -name "CryptoExtensions" -IncludePattern $CryptoExtensions -Description "Crypto Extension Detection" | Out-Null # Set FRSM Notification Message & Scan Interval $Notification = New-FSRMAction -Type Email -Subject "Crypto File Activity Detected - $env:COMPUTERNAME" -Body "User [Source IO Owner] attempted to save [Source File Path] to [File Screen Path] on the [Server] server. This file is in violation of the [Violated File Group] file group. This file could be a marker for malware infection, and should be investigated immediately." -RunLimitInterval 30 -MailTo $SMTPTo # Create FSRM Template New-FsrmFileScreenTemplate -Name CryptoExtensions -Description "Known CryptoLocker File Extesions" -IncludeGroup CryptoExtensions -Active: $true -Notification $Notification | Out-Null # Build Drive Lists $Drives = Get-WmiObject -Class Win32_LogicalDisk -Filter DriveType=3 | Select -ExpandProperty DeviceID # Apply FSRM Screen foreach ($Drive in $Drives) { New-FSRMFileScreen -Path $Drive -Active: $true -Description "Crypto Extension Monitoring" -Template CryptoExtensions -Notification $Notification | Out-Null } } # Update Cyrpto File Extensions if ((Get-FSRMFileScreen).Description -contains "Crypto Extension Monitoring") { # Create Array For File Extensions $CryptoExtensionsUpdate = New-Object -TypeName System.Collections.ArrayList # Get Known Extensions $KnownExtensions = Get-FSRMFileGroup -Name CryptoExtensions | select -ExpandProperty IncludePattern # Add Known Extensions To $CryptoExtensions Array foreach ($Extension in $CryptoExtensions) { If ($Extension -notin $KnownExtensions) { $CryptoExtensionsUpdate.Add($Extension) | Out-Null } } # Update File Screen Set-FSRMFileGroup -Name CryptoExtensions -IncludePattern $CryptoExtensionsUpdate | Out-Null } # Check for FSRM File Screen $CryptoScreen = Get-FSRMFileScreen | Where-Object { $_.Description -eq "Crypto Extension Monitoring" } if ($CryptoScreen -gt $null) { $CryptoCICompliant = $true } else { $CryptoCICompliant = $false } Return $CryptoCICompliant } CryptoBlockerMicrosoft Technet Script Download – https://gallery.technet.microsoft.com/scriptcenter/Ransomware-FSRM-File-889d58de
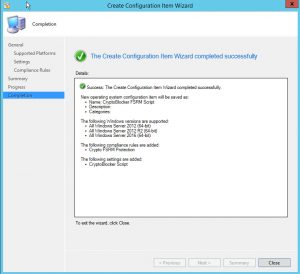
- Click on the “Compliance Rules” tab, then click on “New” and enter the following:Name: Crypto FSRM Protection
Rule type: Value
The value returned by the specified script: Equals
the following values : TrueCheck the Checkbox for “Report noncompliance if this setting is not found” - Review the Summary and click Next and Close when done.
Configuration Baseline
With the configuration item created the next step is to publish the CI via a CB to a collection containing your file servers. To do so follow the below process (I am going to assume you have already created a collection containing your file servers);
- Right click on Configuration Baseline and click Create Configuration Baseline
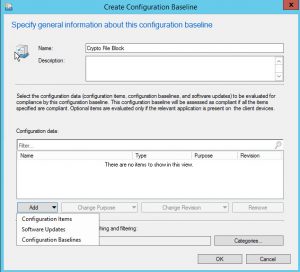
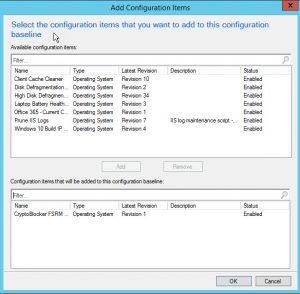
- Name the Baseline “Crypto File Block” or something of your own choice, then click on Add and add in the CryptoBlocker FSRM CI created earlier
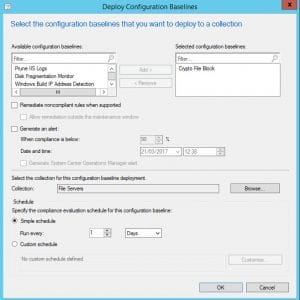
- The final step is to deploy the Configuration Baseline to your File Server Collection, so right click on the CB and go to Deploy
Verify FSRM Rules Creation
After waiting for your Configuration Baseline to apply, to verify that the settings have applied simply log onto any of the servers within your collection and open the FSRM console. Under file screens you should have something similar to the below;
Testing FSRM Rules
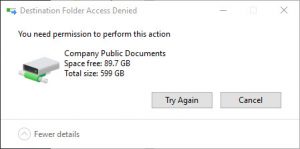
The next step is to obviously test the file screen. To do so simply create a file in Notepad and name it with a file extension listed on the list of known ransomware file extensions, for example; test.encrypted. Try dropping the file onto a protected server share and you should receive something similar to the following;
At the same time the administrative contact should receive an email similar to the one below;










The .enc file extension is unfortunately also used by Intel’s wifi driver, which stores wireless network information inside the user’s profile, under the path “%userprofile%\AppData\Roaming\Intel\Wireless\WLANProfiles\Profiles.enc”.
For anyone using roaming profiles and the Intel wireless drivers, you may want to add an exclusion to the file group for this particular file and partial path, or else you’re going to get a lot of unwanted email alerts.
It looks like the list on the site has a space before the *.btcbtcbtc entry. Once i removed it the script started working.
Have you tested this against Server 2008 R2?
Hi Justin,
The file has been updated so it shouldn’t cause an issue now. I haven’t tested it against 2008 R2, however I’ll spin up a VM and check the PS commandlets etc.
Maurice
Did you ever get the chance to test this against 2008R2? I’d love to know if it can be used with servers running the older OS.
Hi Steve,
I didn’t, however I might give this a go tomorrow as I am going to make up update to the script with the wannacry extensions added.
Maurice
I am running this locally on my server and I am having issues with Update File Screen step. I have the text file located at the root of C for testing. Keeps coming back with the errors below:
Set-FSRMFileGroup : 0x80045321, The specified file group definition is invalid.
At C:\RandsomwareFileBlock.ps1:101 char:3
+ Set-FSRMFileGroup -Name CryptoExtensions -IncludePattern $CryptoExtensionsUpda …
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : NotSpecified: (MSFT_FSRMFileGr…ptoExtensions”):Root/Microsoft/…T_FSRMFileGroup) [Set-FsrmFileGroup], CimException
+ FullyQualifiedErrorId : HRESULT 0x80045321,Set-FsrmFileGroup
Hi Justin,
Are you using the file extension list from this site or have you modified it?.
Maurice
Hi Maurice
Great post – Have set it up manually on one server – works great – have tried to get it working with SCCM – no luck – have tried executing the script on a file server and it installs the role and sets SMTP settings but it keeps coming back with the same errors as per below;
New-FSRMFileGroup : 0x80070057, The parameter is incorrect.
At C:\Users\user1\Desktop\Crypto.ps1:29 char:5
+ New-FSRMFileGroup -name “CryptoExtensions” -IncludePattern $CryptoExtensions …
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : InvalidArgument: (MSFT_FSRMFileGroup:Root/Microsoft/…T_FSRMFileGroup) [New-FsrmFileGroup], CimException
+ FullyQualifiedErrorId : MI RESULT 4,New-FsrmFileGroup
New-FsrmFileScreenTemplate : 0x80045301, The requested object was not found.
At C:\Users\user1\Desktop\Crypto.ps1:35 char:5
+ New-FsrmFileScreenTemplate -Name CryptoExtensions -Description “Known Crypto …
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : NotSpecified: (MSFT_FsrmFileScreenTemplate:Root/Microsoft/…eScreenTemplate) [New-FsrmFileScreenTemplate], CimException
+ FullyQualifiedErrorId : HRESULT 0x80045301,New-FsrmFileScreenTemplate
New-FSRMFileScreen : 0x80045301, The requested object was not found.
At C:\Users\user1\Desktop\Crypto.ps1:43 char:7
+ New-FSRMFileScreen -Path $Drive -Active: $true -Description “Crypto Extens …
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : NotSpecified: (MSFT_FSRMFileScreen:Root/Microsoft/…_FSRMFileScreen) [New-FsrmFileScreen], CimException
+ FullyQualifiedErrorId : HRESULT 0x80045301,New-FsrmFileScreen
New-FSRMFileScreen : 0x80045301, The requested object was not found.
At C:\Users\user1\Desktop\Crypto.ps1:43 char:7
+ New-FSRMFileScreen -Path $Drive -Active: $true -Description “Crypto Extens …
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : NotSpecified: (MSFT_FSRMFileScreen:Root/Microsoft/…_FSRMFileScreen) [New-FsrmFileScreen], CimException
+ FullyQualifiedErrorId : HRESULT 0x80045301,New-FsrmFileScreen
New-FSRMFileScreen : 0x80045301, The requested object was not found.
At C:\Users\user1\Desktop\Crypto.ps1:43 char:7
+ New-FSRMFileScreen -Path $Drive -Active: $true -Description “Crypto Extens …
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : NotSpecified: (MSFT_FSRMFileScreen:Root/Microsoft/…_FSRMFileScreen) [New-FsrmFileScreen], CimException
+ FullyQualifiedErrorId : HRESULT 0x80045301,New-FsrmFileScreen
False
Any ideas on this, hopefully something simple – when I search for some of the errors some related solutions come back but nothing definitive.
Thanks in advance
Hi Dallan,
Looking at the output it appears that the FSRMTemplate is having difficulty with the FSRMFileGroup which is set earlier in the script and is in turn dependent on reading in the list of extensions from the $CryptoExtensions variable. So can you confirm that the $CryptoExtensions path specified is accessible by the computer accounts to which the baseline is deployed?.
Maurice
Hi Maurice – I did check on this and yes all servers that the BL is deployed to have full access to the location where the file extension txt file is located. I have tried running locally on a server with txt file local and still the same error appears – have set-execution policy Bypass mode also – it will install Role and set SMTP settings – unfortunately it wont do anything further.
Thanks for your response
Dallan
Hi Dallan,
Check your site extensions list file, compare it to the one on the site and you should be good.
Maurice
Hi Maurice all working now – extension list was the issue- thanks for your help
Dallan
In your latest script, you have a setting that is wrong, or?
—-
# Set FSRM Email Settings
Set-FSRMSetting -AdminEmailAddress $AdminEmail -SMTPServer $SMTPServer -FromEmailAddress $SMTPTo
—-
The FromEmailAddress should be like this:
FromEmailAddress $SMTPFrom
Hi Mats,
It was a typo. I have corrected this and thanks for letting me know.
Maurice
Please update your Powershell script so that if you change ANYTHING in the script after it was deployed, it will automatically update the settings on ALL deployed servers.
I’m not that good with scripts so I’m not really sure where to put the settings and where to set all the brackets.
Please!!
This is a great idea. Is there a way to make it work for EMC File storage? It appears it would only work if you had windows file servers, but I maybe I am missing something.
Hi Matthew,
I am not familiar with the options open to you at a hardware level with EMC File Storage, the post is intended purely for Windows File Servers.
Maurice
Nice post but I wonder
1: Why don’t you have all file extensions included that you can find on other sites on Internet?
2: I also wonder why it is possible for me ( after I’ve followed your guide) to drop a test file on my c:\ drive without warning, is that right? It’s blocked on other drives.
Hi,
Please see answers to your queries below;
1. The idea here was to provide a base level of protection and unfortunately if I was to keep the extension list up to date, it would be out of date by time the post had been written. In writing this I grabbed a sizable chunk of extensions for the script but you can easily add to these as required to keep the list up to date.
2. FSRM will only apply a passive screen type for your system drive as typically data shares are on/should be on drives other than the system drive.
Maurice
Thanks! I added more extensions to an already deployed baseline but the list doesn’t seem to update on the servers even if I set the compliance evaluation Schedule to 1 minute in the deployment properties.
I even wonder how to send those e-mails without passwords?
I have just posted an update based on your feedback. The script will now pull a list of known file extensions from a text file you store on a UNC share. If you make additions to this text file, all servers will update their list upon the next CB scheduled update.
Great job! If I change theese settings, will it also update all servers then?:
# Email Sever Settings
$SMTPServer = “YOURSMTPSERVER”
$SMTPFrom = “$env:COMPUTERNAME@YOURDOMAIN”
$SMTPTo = “Admin@YOURDOMAIN”
$AdminEmail = “Admin@YOURDOMAIN”
If you have applied the script without modifying the placeholders in the variables, you will need to update the variables and modify the script to run the following lines under the Update Crypto File Extensions If statement;
# Set FSRM Email Settings
Set-FSRMSetting -AdminEmailAddress $AdminEmail -SMTPServer $SMTPServer -FromEmailAddress $SMTPTo
# Set FRSM Notification Message & Scan Interval
$Notification = New-FSRMAction -Type Email -Subject “Crypto File Activity Detected – $env:COMPUTERNAME” -Body “User [Source IO Owner] attempted to save [Source File Path] to [File Screen Path] on the [Server] server. This file is in violation of the [Violated File Group] file group. This file could be a marker for malware infection, and should be investigated immediately.” -RunLimitInterval 30 -MailTo $SMTPTo