If you haven’t already upgraded to ConfigMgr build 1706 then you are missing out on one of the new and best features, the ability to near instantly run a script on a collection. The feature is still in its infancy and yes improvements needed and being worked upon, but the ability to run scripts without packaging them up is truly awesome and something I am going to explore in the below use case scenario.
DNS SUFFIX REPORTING
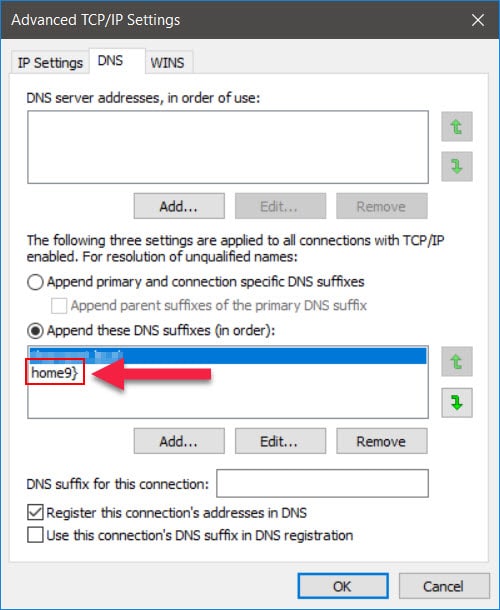
Over the past number of years I have seen instances where some of our laptops have had their DNS suffix entries updated, not by the user but by what appears to be malicious code on some websites. This can cause issues accessing internal resources and external websites and also has a greater potential security issue, so this is something I had been watching out for.
I had another case this morning (pictured below) and thought I would make use of the new script feature and write up a quick script to get a near instant report on all machines with the number and list of DNS suffixes listed.
So here is the script I came up with;
$DNSSuffix = (Get-DNSClientGlobalSetting | Select-Object -ExpandProperty SuffixSearchList)
$DNSSuffixCount = $DNSSuffix.Count
$DNSSuffixReport = @()
foreach ($DNSEntry in $DNSSuffix)
{
$DNSEntries += ($DNSEntry + ";")
}
$DNSEntries = $DNSEntries.Trimend(";")
$DNSSuffixReport += New-Object psobject -Property @{ ComputerName = $env:ComputerName; DNSSuffixNames = $DNSEntries; DNSSuffixCount = $DNSSuffixCount }
$DNSSuffixReport[1 .. ($DNSSuffixReport.Count - 1)] | Select-Object ComputerName, DNS* | Export-CSV -Path "\\SERVER\SHARE\DNSSuffixReport.csv" -NoTypeInformation -Append
The script in this case generates a CSV report with the following details;
- Computer Name
- DNS Suffix Count
- DNS Suffix Names
Implementing
So now we have a script that will report the required details we simply need to set up a network share for the report, taking into consideration that the share permissions will need allow for systems and not users to update the file. Once that share is set up we can put the script to work.
A prerequisite for deploying your own unsigned scripts is to perform the following actions;
Allow users to approve their own scripts
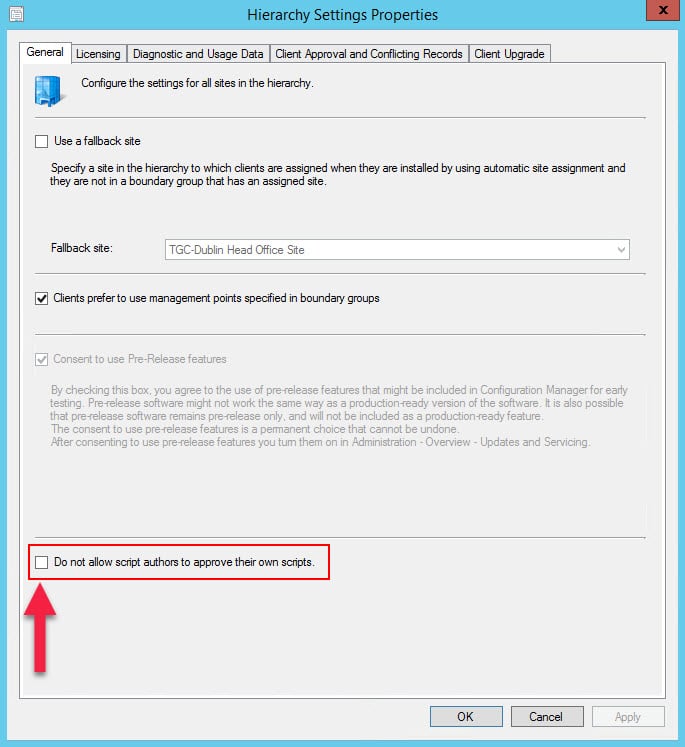
- In the Configuration Manager console, click Administration.
- In the Administration workspace, expand Site Configuration, and then click Sites.
- In the list of sites, choose your site and then, on the Home tab, in the Sites group, click Hierarchy Settings.
- On the General tab of the Hierarchy Settings Properties dialog box, clear the checkbox Do not allow script authors to approve their own scripts.
More information can be found here – https://docs.microsoft.com/en-us/sccm/apps/deploy-use/create-deploy-scripts
Add PowerShell Script
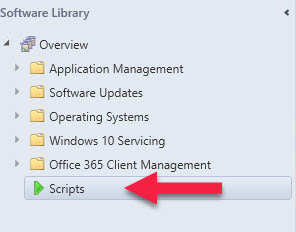
- Launch the Configuration Manager Console
- Click on the Software Library Tab and go to Scripts
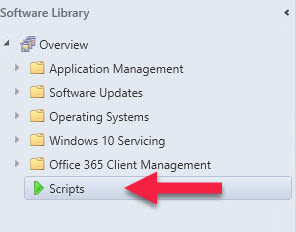
- Click on the Create Script button
- Give your script a meaningful name, in this example I am using “DNS Suffix Reporting“
- Paste in the contents of your script or Browse to find a PS1 script file (obviously after having modified the server and share name)

- Click on Next, Next and Close to finish creating the Script for deployment
- Right click on the newly created script and click on Approve / Deny
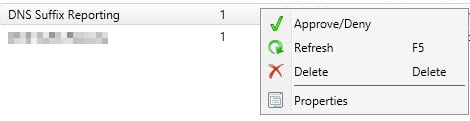
- Click Next through the Approval screens
At this point you should now have an approved script.
Deployment
Deploying the script is done in the in the Assets and Compliance section of the console. Simply select the device collection you wish to run the script against, right click on the collection and go to “Run Script“
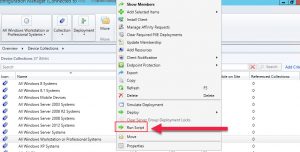
Select the script you have just created and it will start running on the collection.
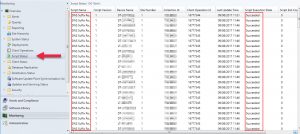
Monitoring
To ensure your script is executing on your clients you can go to the Monitoring tab and click on Scripts. From here you will see the script names and their current status on each of the devices you have targeted;
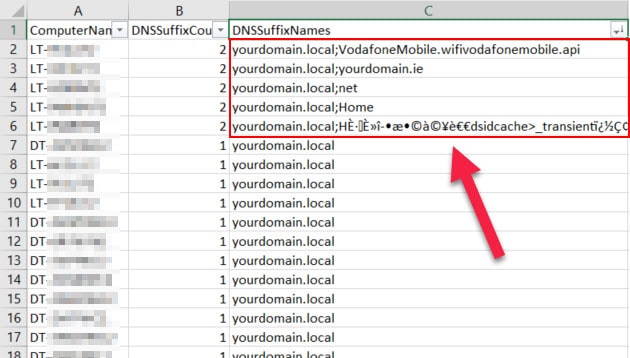
Report
After a few seconds you should see the CSV being created on the specified share and the data size increasing as each of your clients reports their values into it. At the end of which you should have something similar to the below:
Here you will be able to see a list of computers which fall outside of the expected normal DNS suffix entries.
Remediation
The next step for automatically remediation of this potential security issue is to create a Configuration Baseline.
For the Configuration Item Discovery Script use the following lines of code if you are looking for a set number of DNS suffixes (with the Setting Type set to Script and the Data Type set to Integer):
function DNSSuffixCheck
{
$DNSSuffix = (Get-DNSClientGlobalSetting | Select-Object -ExpandProperty SuffixSearchList)
$DNSSuffixCount = $DNSSuffix.Count
Return $DNSSuffixCount
}
DNSSuffixCheck
Monitor the Discovery for the set value of DNS entries expected on your network and for remediation you can either create an array containing your DNS entries to be applied, or alternatively just clear the DNS entries by using the following single line:
Set-DnsClientGlobalSetting -SuffixSearchList @("")
Conclusion
The new script feature in 1706 is without a doubt going to feature a lot in upcoming solutions from the community, so try it out and use it carefully too. In the mean time take time to thank the product team in Microsoft who listen to you the customer and the wider ConfigMgr community.









Hi Maurice,
Thanks for responding and point taken.
I like the new Script feature, but I’m just still scratching my head to come up with examples when I’d use it over CI/CB’s – probably in situations where speed is important and monitoring/reporting is less so.
The point about the new scripting feature is speed and flexibility. Configuration baselines and applications can both be used for deploying tasks via PS scripts, however they will need a machine to process it’s computer policy, become aware of the item, schedule it etc. When you run a script via the new console method it runs near instantly on all active machines in the collection.
So let’s take the recent SMB 1 issues with ransomware. In that scenario you could have removed the feature near instantaneously from your entire environment and as a follow up put a CB into place for continued compliance.
Great article.
But if you have to go through the trouble of writing an baseline with remediation, why not do it all from within it?
Does the script take into account whether or not the csv file is locked/in use by other clients?
Hi Bo,
The point of the article was more to highlight the script capability and not purely designed to be about creating and deploying a CB. If you wanted you could of course just run the the CB and have your compliance monitoring in the console.
Maurice
Good work. Just remember 1706 is still Fast Ring currently and may not be suitable for everyone’s production environments ;).