Recently Microsoft enhanced the Intune Managed Browser experience with Mobile Application Management (MAM) and app-based Conditional Access (CA) a lot. It is integrated into the Conditional Access story as an approved app and supports the Azure AD Application Proxy very well now.
What does this allow us to do now?
We are now able to design a solution to publish our internal websites externally with minimal effort and then allow access to it from our mobile devices only by the Intune Managed Browser protected by Intune app protection policy. This ensures the information is safeguarded in our containerized Intune MAM solution. This gives most companies enough trust to actually do the publishing of internal resources for usage on mobile devices and support the bring your own device (BYOD) solution.
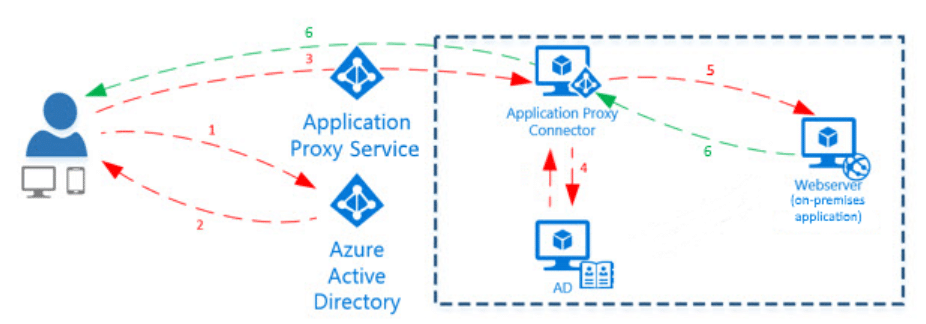
Please read the How does Application Proxy work? documentation from Microsoft to get a better understanding what we are going to do in the next section with the Azure AD Application Proxy. The Azure AD Application Proxy architecture is shown in the figure below:
One of the nice things is it will not require us to open up any inbound firewall ports. As long as we are allowed to make outbound connections we can publish internal websites easily to external. The solution even supports various authentication scenarios inclusive Single Sign-On (SSO).
Here is a walkthrough of a demo setup to show it in action
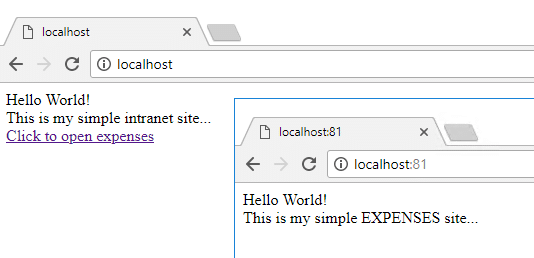
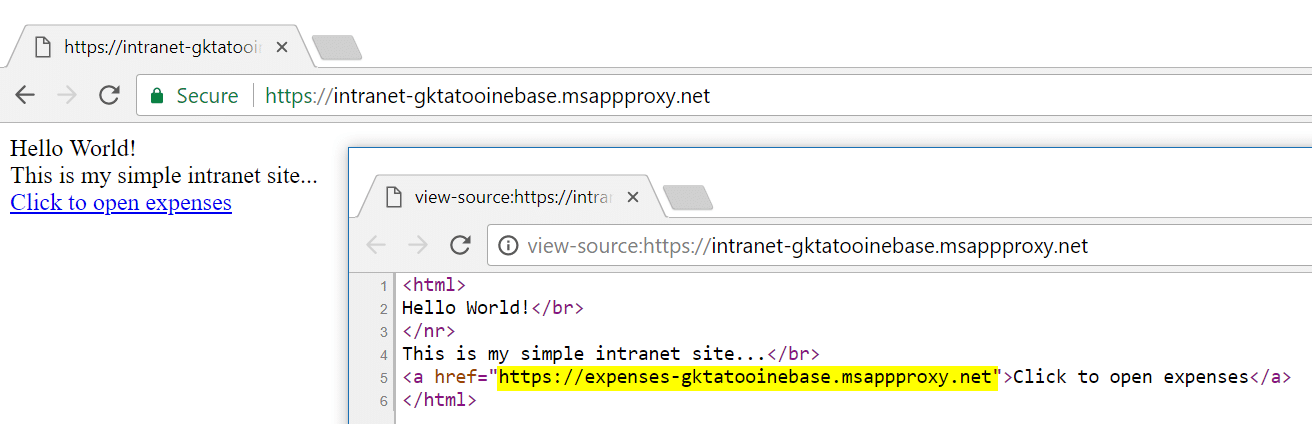
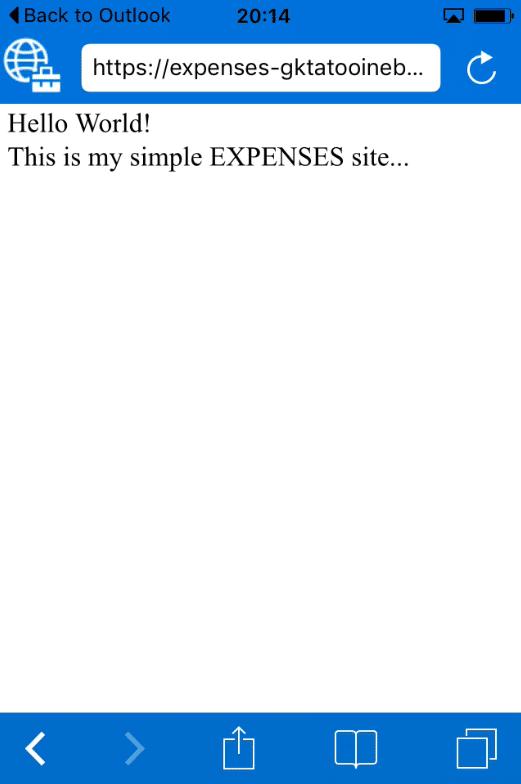
The walkthrough of the demo scenario should get you a deeper understanding of the new possibility. I used an iOS mobile device for the tests. I assume some internal websites intranet and expenses and they are available in the internal network only. To simulate that, I have setup an IIS server hosting the two simple websites, intranet and expenses within a private network. They are reachable on the IIS server via https://localhost for intranet and https://localhost:81 for expenses. In addition I have a link from intranet pointing to expenses website (link target is: https://localhost:81, compare screenshot with html source code). I built the two demo sites to also demonstrate link translation with Azure AD Application Proxy later on.
HOW DO WE GET THE INTERNAL WEBSITES PUBLISHED NOW?
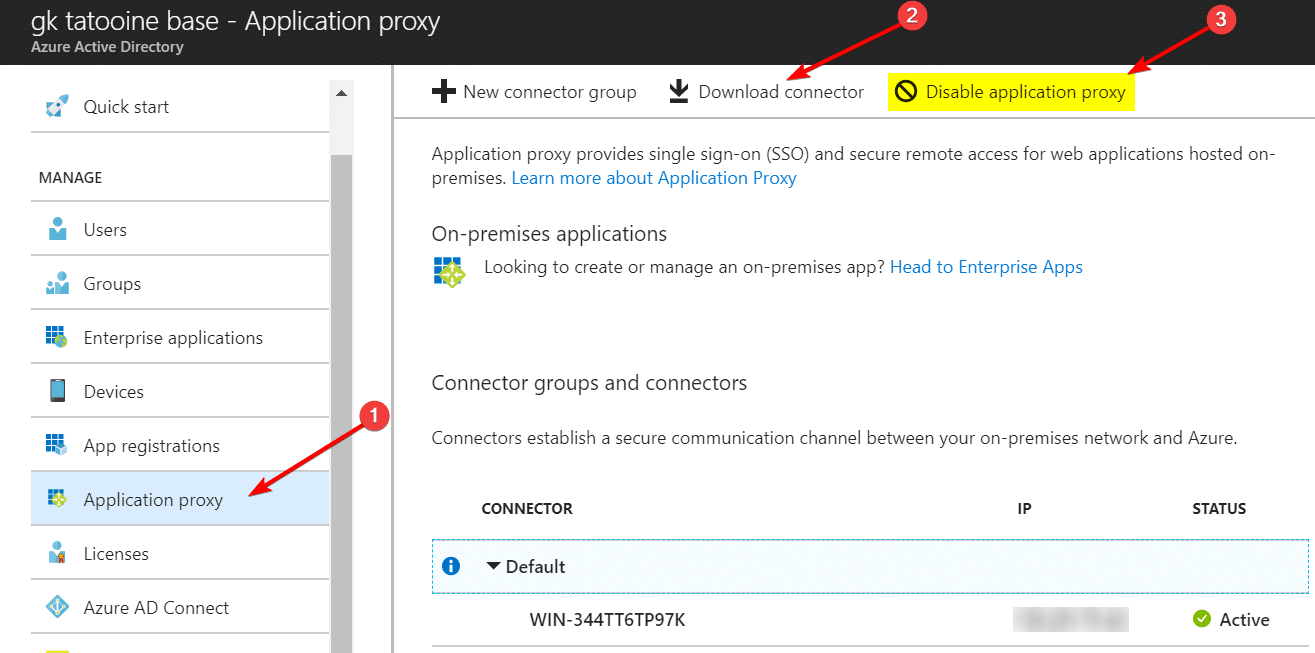
First of all we need to switch off the IE Enhanced Security Configuration on the Windows Server otherwise we are not able to complete the login prompt of the Azure AD Application Proxy during setup procedure. Then we are downloading the Azure AD Application Proxy on our demo IIS server and run the msi installer. It’s a very lightweight installer and the only thing we need to provide is the Global Administrator credential during setup to finish the process.
The next step after installing the connector is to enable it by clicking Enable application proxy. After it is enabled the UI switches to “Disable application proxy” (shown in screenshot as step 3). Once enabled we have the Connector group default and our server listed there. It is possible to install more then one connector and build connector groups to support better reliability of the publishing (in fact this is recommended). The connector does not need to be installed on the IIS as I have done it in my demo setup, it should be on a dedicated Windows Server 2016 for example. I needed to run it on the IIS for simplicity of my setup and to use the internal address of https://localhost during publishing later on.
The official documentation for the Azure AD Application Proxy from Microsoft is found here:
https://docs.microsoft.com/en-us/azure/active-directory/active-directory-application-proxy-enable
or you follow the link on the application proxy blade “Learn more about Application Proxy“.
With an up and running connector we can publish the websites now. It is the best to follow the detailed step-by-step guide from Microsoft here:
https://docs.microsoft.com/en-us/azure/active-directory/application-proxy-publish-azure-portal
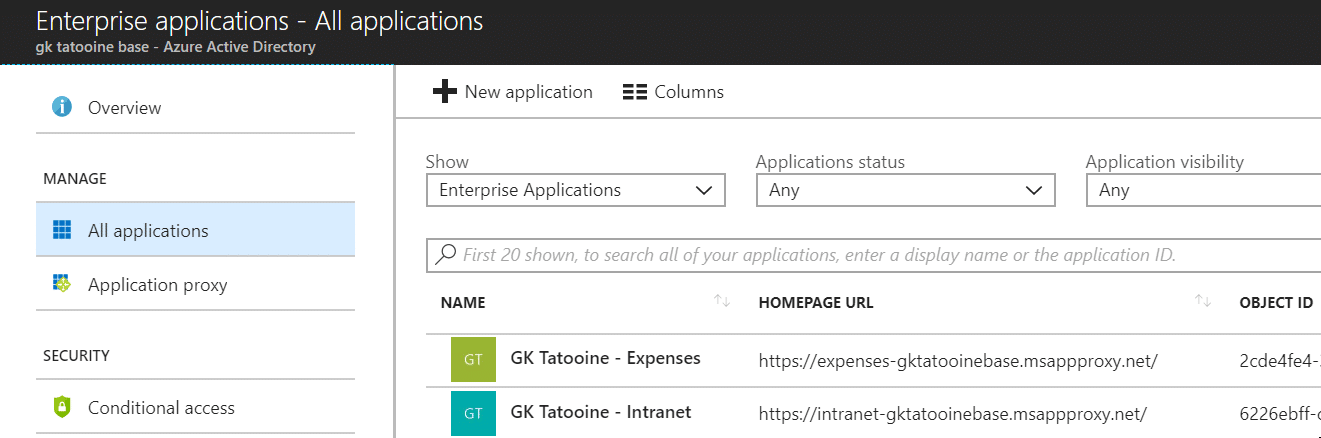
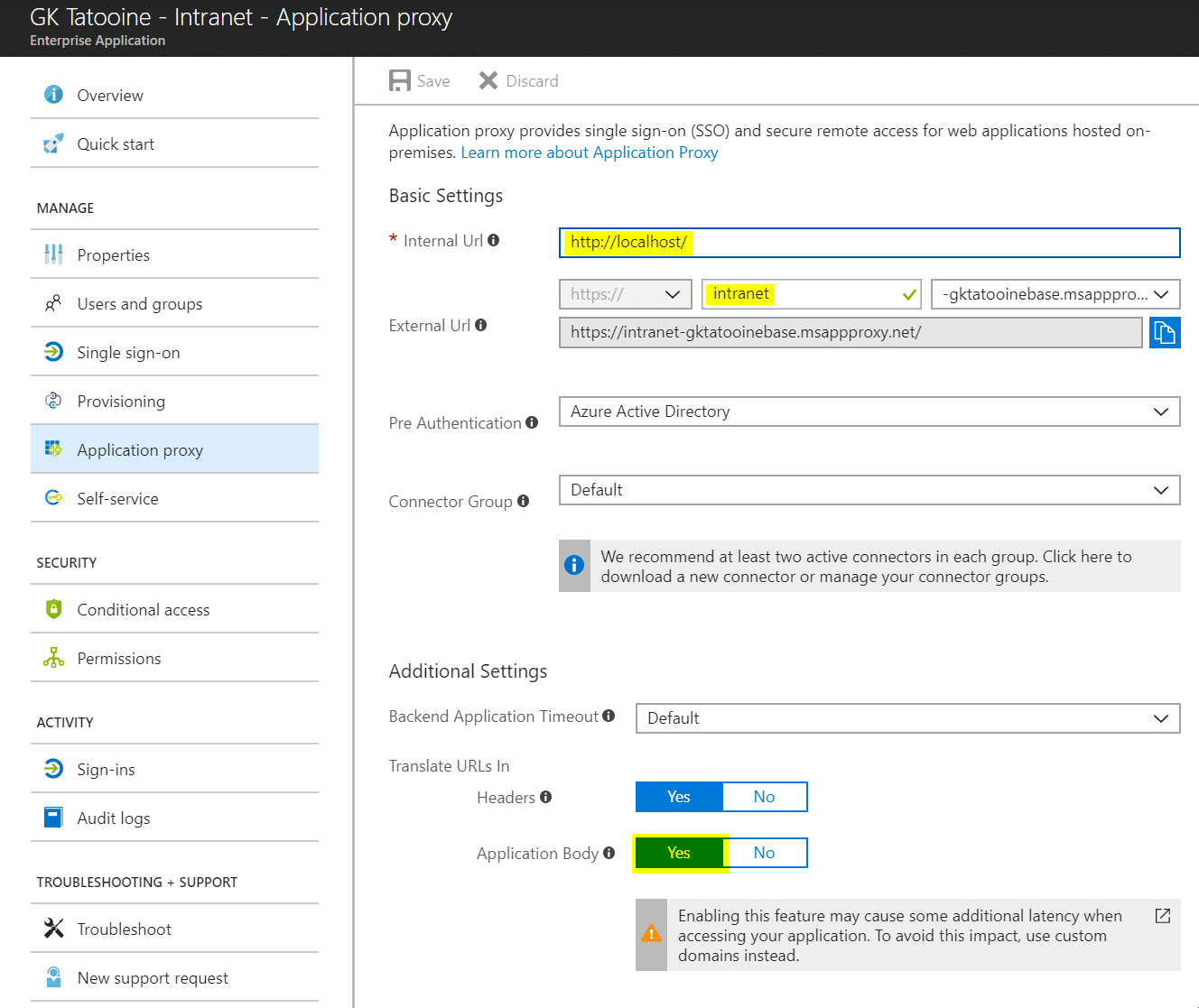
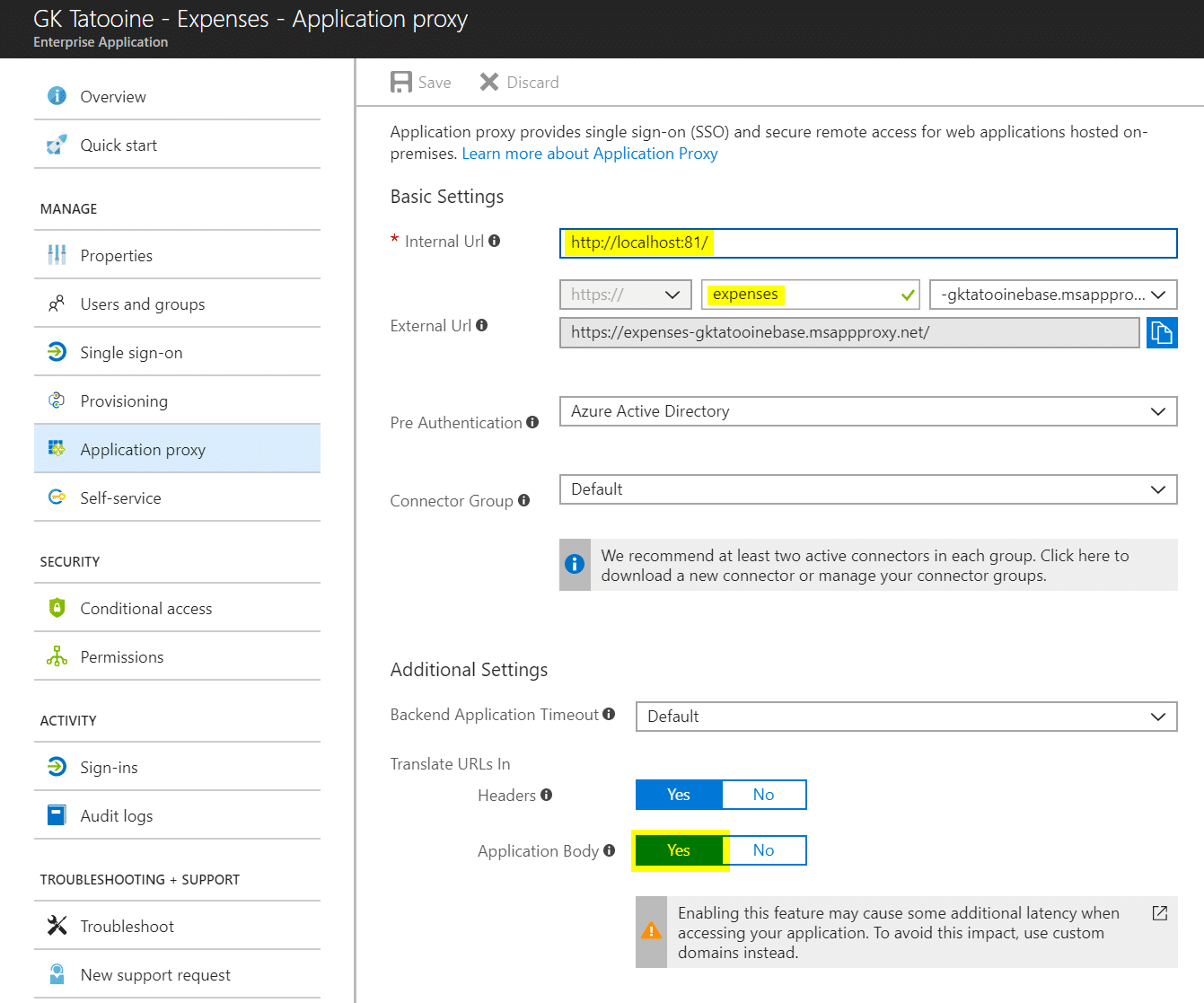
and make both available. I published my both sites as an Enterprise Application as described and used no custom domain, but enabled link translation in the application body.
Published internal websites:
Details of the website intranet with internal URL https://localhost
Details of the website expenses with internal URL https://localhost:81
Now I can open up my published intranet from external and the intranet link originally pointing to https://localhost:81 was replaced by the application proxy because we enabled link translation on the application body (compare screenshot below). This works only if we publish both websites as the application proxy must find a published website for https://localhost:81 to do the translation.
In a real world implementation I would recommend to use a custom domain for publishing to maintain your links. For example if we have mydomain.com as Active Directory (AD) and I publish via Azure AD Application Proxy with the custom domain mydomain.com I can reach the website internally and externally with the same URL. To set this up follow the instructions here:
Working with custom domains in Azure AD Application Proxy
https://docs.microsoft.com/en-us/azure/active-directory/active-directory-application-proxy-custom-domains
SECURING OUR INTUNE MOBILE APPS WITH INTUNE APPLICATION PROTECTION POLICIES
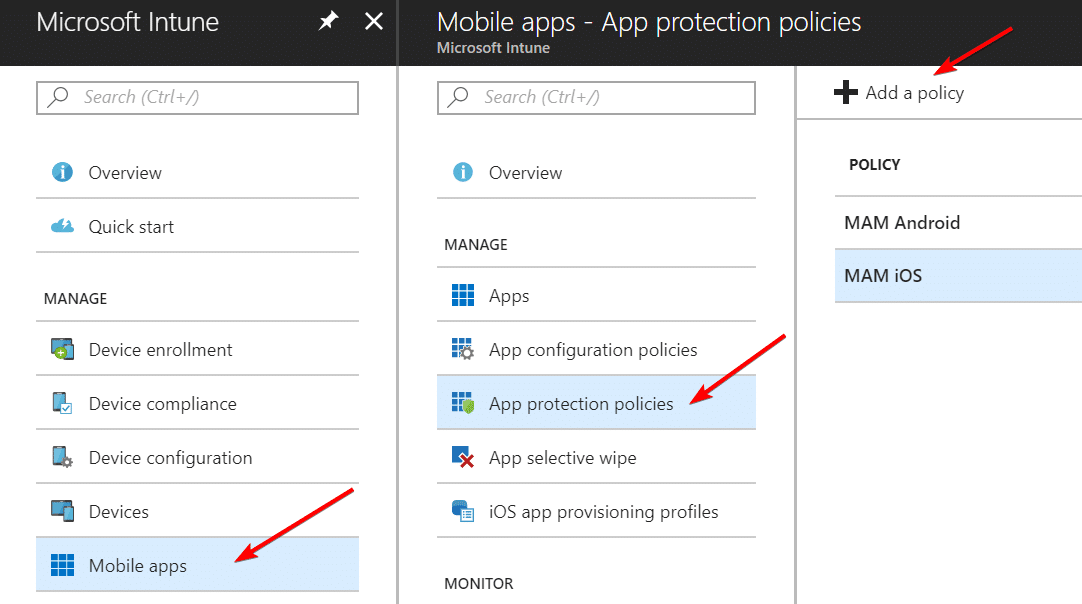
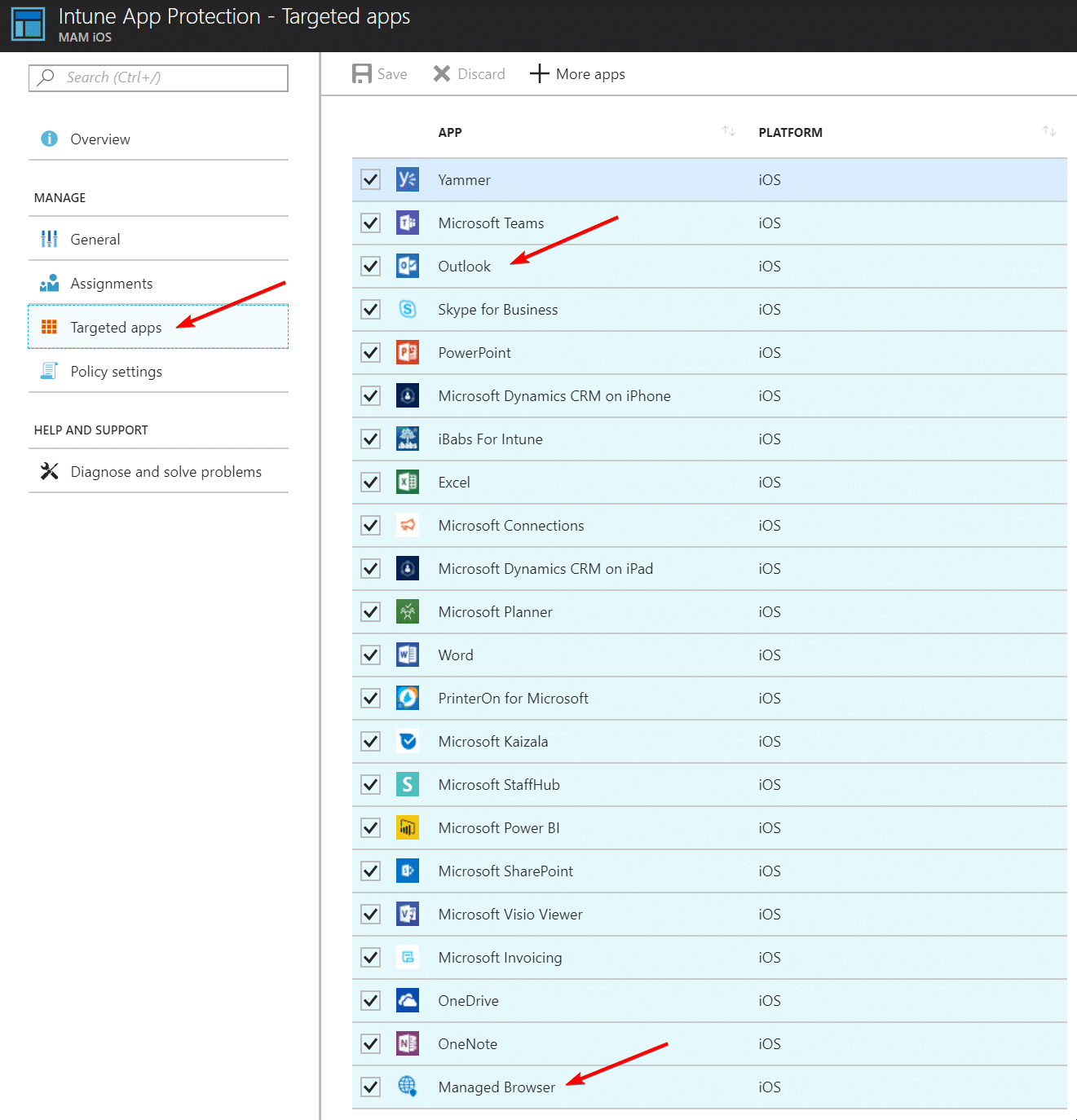
Now we need to add a MAM policy – app protection policy to secure the Intune Managed Browser and Mobile Outlook. To do that we open Intune > Mobile apps > App protection policies > Add a policy
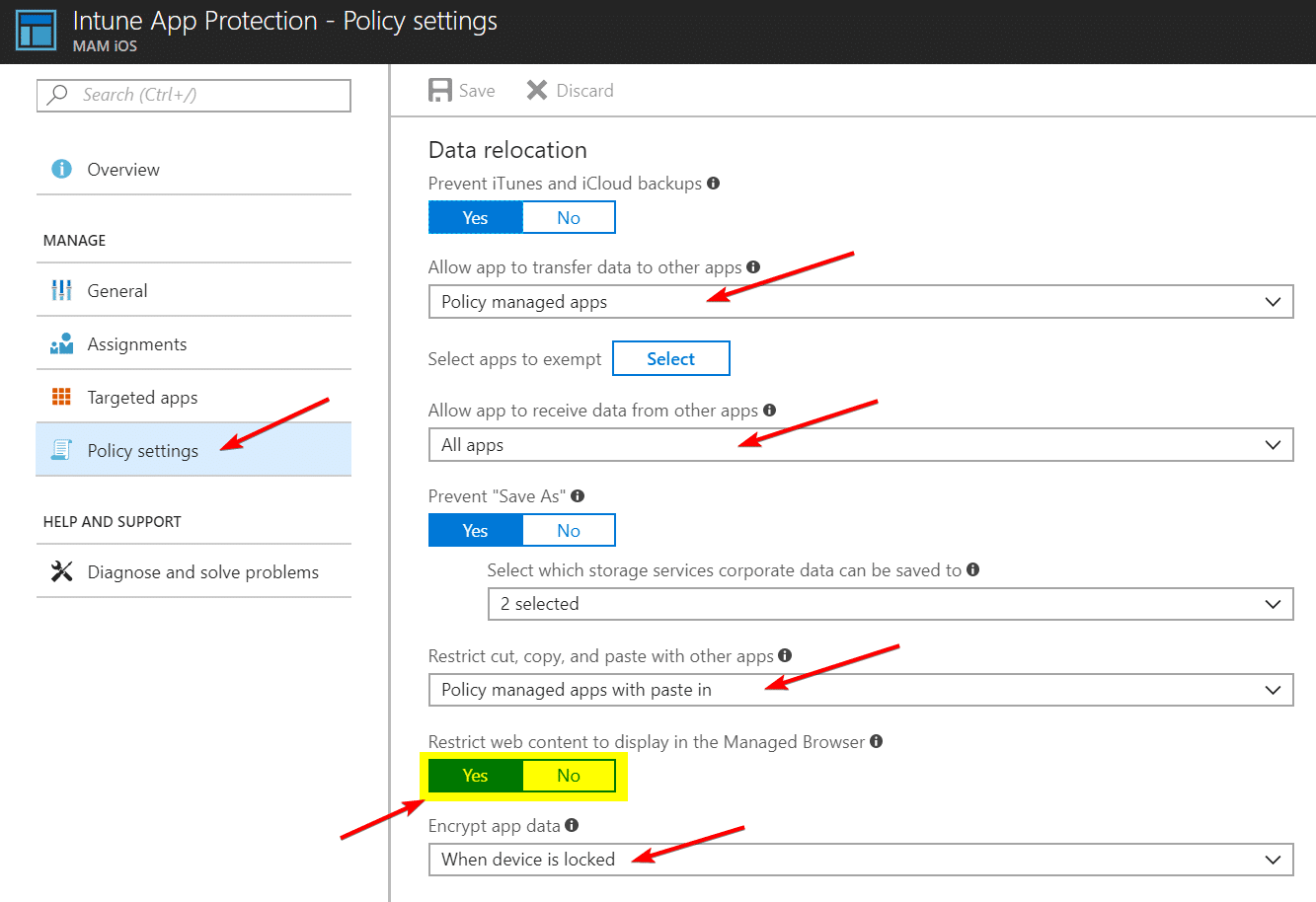
After adding the policy we make sure Outlook and the Managed Browser is in the targeted apps and of course we adjust the individual Policy setting to meet our corporate standard and to realize the containerization (e.g. let apps only transfer data to other managed apps, encrypt data and so on…).
For the policy setting we need to make sure the setting Restrict web content to display in the Managed Browser is set to Yes. This makes sure internal links in emails are opened in the Intune Managed Browser. Even better because of the Azure AD Application Proxy publishing we make sure that internal links get translated and opened successful in Intune Managed Browser. We will do that by assigning an additional app configuration policy in the next step.
As last configuration we assign the app protection policy to our AAD user group we want to target.
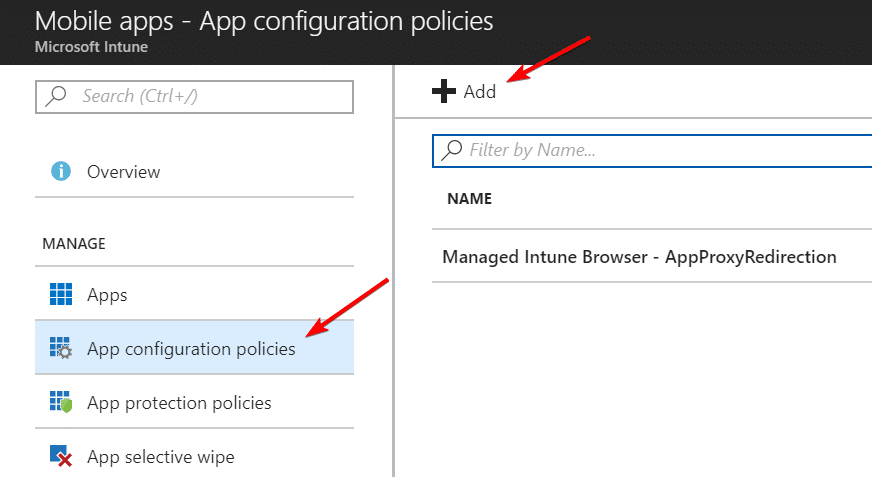
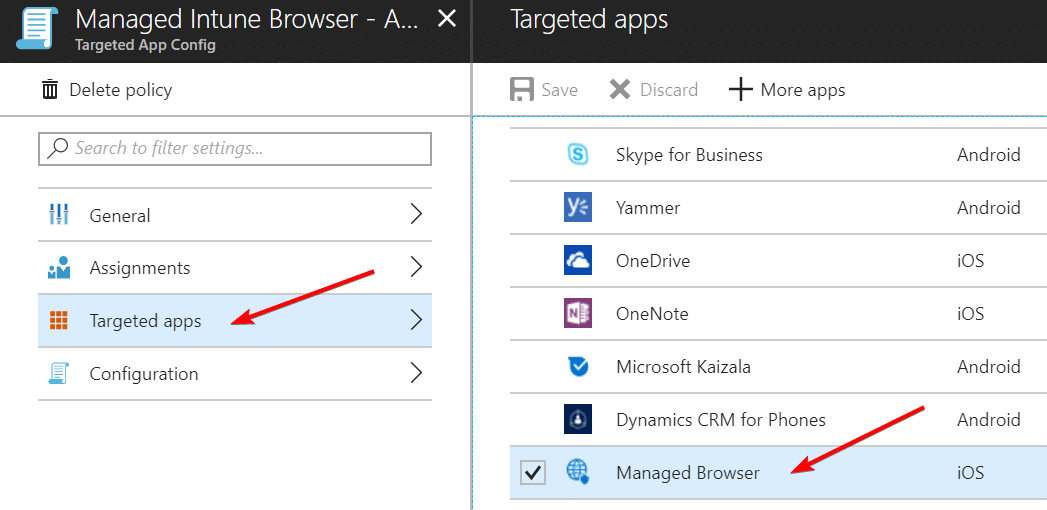
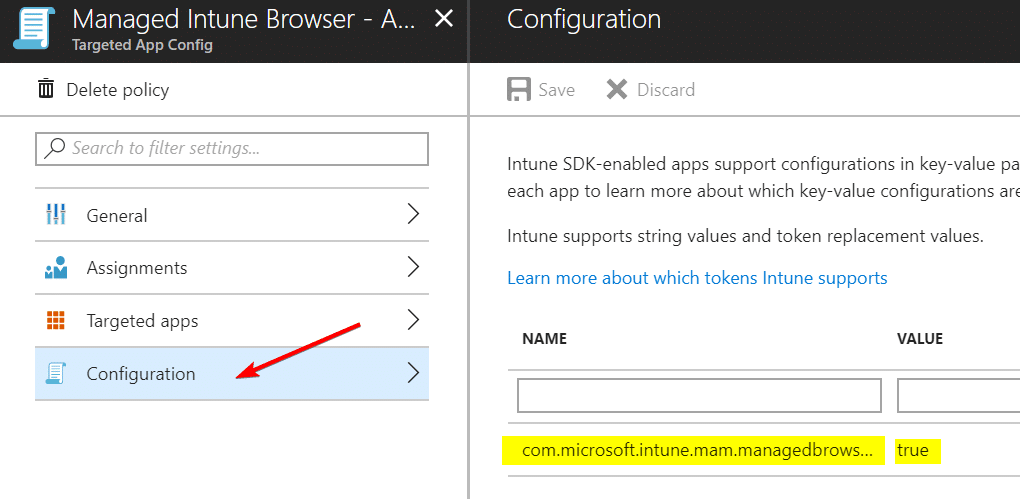
To configure the Intune Managed Browser to work hand in hand with the Azure AD Application Proxy and translate internal URLs to the published URLs we need to configure an app configuration policy for the managed browser.
Now the important piece of configuration is to configure:
| Key | Value |
| com.microsoft.intune.mam.managedbrowser.AppProxyRedirection | true |
The screenshot below does not display the complete string!
Again as last configuration we assign the app configuration policy to our AAD user group we want to target.
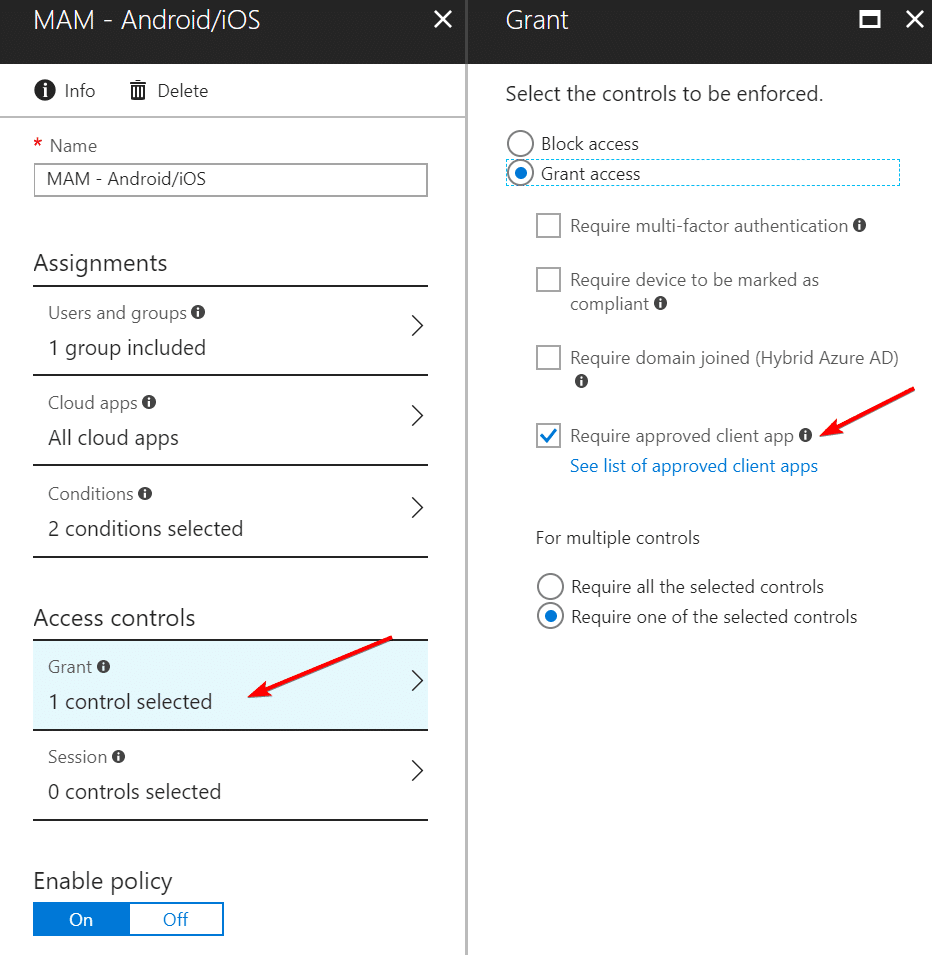
CONTROLLING ACCESS TO THE INTERNAL WEBSITES WITH APP-BASED CONDITIONAL ACCESS
Now we need to make sure our internal published website can only be accessed by Intune approved apps which are protected by app protection policy.
To do that we create the following Conditional Access policy in Intune or in the Azure AD portal. We assign our AAD user group, target All cloud apps, and include iOS and Android devices, and select Browser and Mobile apps desktop clients
As access control we grant access for approved client apps by choosing the option Require approved client app
How about the user experience?
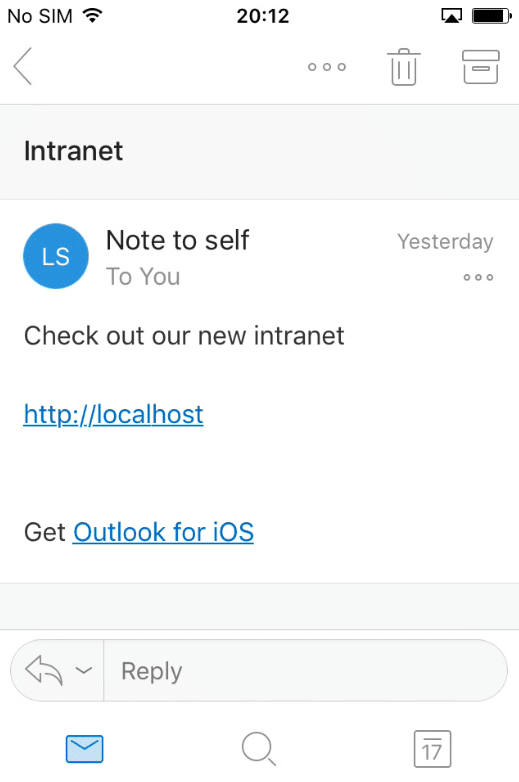
Everything is in place and we assume someone in the company sent us an internal link to the new intranet site https://localhost. We open up mobile Outlook on iOS in this example:
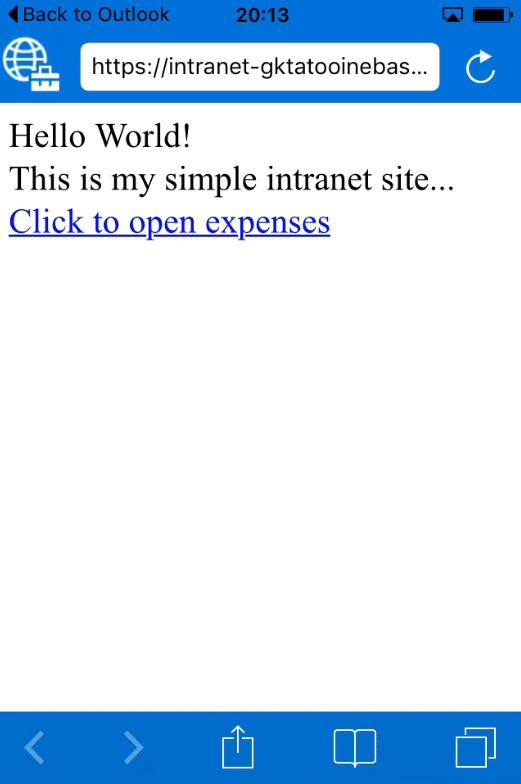
If we now click on the internal link, Outlook is configured to Restrict web content to display in the Managed Browser and will open the link in the Intune Managed Browser for us. The Intune Managed Browser is then instructed for AppProxyRedirection = true. This will redirect us to the external published URL instead of the internal URL as shown below and shows us the demo intranet site:
Even the link within the demo intranet site is translated and will open the published demo expenses website:
To make sure that the published intranet site is only accessible by the Intune Managed Browser we open up Safari and open the published intranet site by typing in the external URL and we will check if access if blocked:
As we see the access is blocked and we get a nice feedback to use the Intune Managed Browser instead and we can directly use the blue link button to open the Intune Managed Browser.
Summary
We have seen how to publish internal websites via Azure AD Application Proxy easily. Then we configured our mobile apps to use an Intune app protection policy and instructed the Intune Managed Browser to use Azure AD proxy redirection to translate internal links and open them successfully. We achieve protection of the published internal website to prevent data leakage.
My advice to all, give it a try and start to play with MAM and app-based Conditional Access as it might be a quick win for your company and finally allow the usage of BYOD as company data can be protected very well in this scenario.
Further information
The Intune Managed Browser now supports Azure AD SSO and Conditional Access!
https://cloudblogs.microsoft.com/enterprisemobility/2018/03/15/the-intune-managed-browser-now-supports-azure-ad-sso-and-conditional-access/
Better together: Intune and Azure Active Directory team up to improve user access
https://cloudblogs.microsoft.com/enterprisemobility/2017/07/06/better-together-intune-and-azure-active-directory-team-up-to-improve-user-access/
Manage Internet access using Managed Browser policies with Microsoft Intune
https://docs.microsoft.com/en-us/intune/app-configuration-managed-browser
How to create and assign app protection policies
https://docs.microsoft.com/en-us/intune/app-protection-policies












Excellent post and how to secure with the Intune protected browser is icing on the cake