If you have Apple Mac’s in your environment and want to use Conditional Access to control access to your Azure AD integrated applications and data, like Office 365. Then you should take a look at what Jamf Pro can give you. Intune standalone or Configuration Manager does not give you a way to have deep management of Mac’s today. This post is not meant to learn you how to manage you Mac’s, but rather how you can integrate your Jamf Pro with Azure AD and Intune so that your Jamf managed Mac’s shows up as compliant devices in Azure AD. This again will allow you to have conditional access policies to control that only compliant Mac’s are allowed to access your corporate Office 365 environment.
I am assuming you already have Jamf Pro running, that is a requirement before we go any further. So to get this up an running we need 3 things
- We must create a new application in Azure AD
- Turn on Intune integration with Jamf Pro
- Configure Conditional Access in Jamf Pro
Create the Azure AD Application
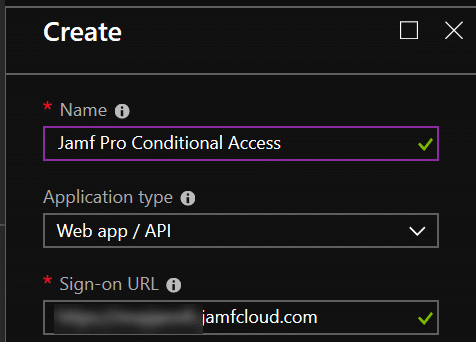
Log on to https://aad.portal.azure.com with admin credentials and go to Azure AD – App registration and click on New application registration
- Name: Jamf Pro Conditional Access
- Type: Web app /API
- Sign-on URL: Use the URL to your Jamf Pro instance
- Click Create
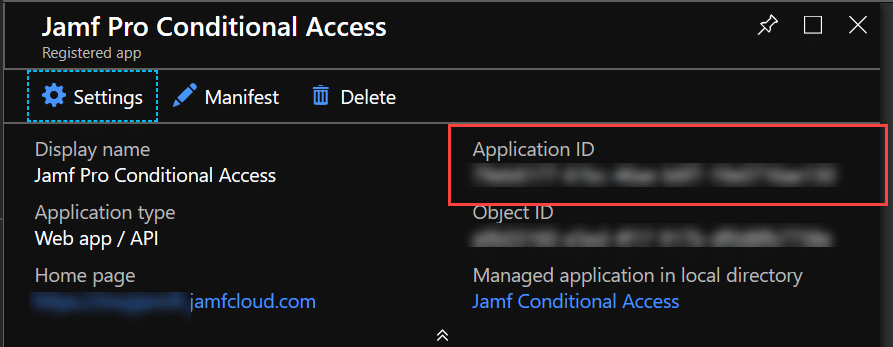
In this page, take a not of your Application ID, you will need it later. Now go to Settings – API Access > Keys
Type in a description – choose when the key shall expire and click on Save
NOTE: When you click on save your key value will show. You MUST copy this key value to a safe place for later use NOW. After you close this windows it will be hidden.
Now you must go to API Access – Required Permissions
Here it is important that we delete the existing permissions as this application will only work if it has the single required permission. After deleting the Azure AD Permission click on Add and select Microsoft Intune API.
Select ONLY the permission Send device attributes to Microsoft Intune and click on Select – Done – Then click on Grant Permissions and answer Yes.
Enable integration between Intune and Jamf Pro
Go to Intune Blade in the Azure Portal. (Microsoft Intune – Device Compliance – Partner Device Management)
In this page we need the Application ID from previous step where we created the Azure AD Application. Put the ID in on 2. and click on Save
Now we are done on this side and need to navigate over to the Jamf Pro Console.
Configure Jamf Pro Conditional Access
In Jamf Pro – go to Global Management -> Conditional Access
In this page we need to enter information about our Azure Active Directory:
- Azure AD tenant name (onmicrosoft.com)
- Application ID
- Application Key
After you have entered the information you should click on the Open administrator consent URL which should give you the following prompt for you to accept:
When you click on Accept you should get the following response:
If you want to verify that the connection is working, on your page in Jamf Pro after you save the configuration you should have a button who says Test masOS Intune Integration. Click on that and see that you get the green status back:
This concludes the first step of the integration. Your Jamf Pro is now integrated with our Azure AD and can send information about your devices into Intune and Azure AD for Compliance. The next post will focus on how to get your devices registered for conditional access via the Company Portal App on your Mac.





















When someone writes an article he/she maintains the thought of
a user in his/her mind that how a user can understand it. Thus that’s why this post is amazing.
Thanks!