Lately there’s been a lot of talk about the newly introduced Microsoft Endpoint Manager solution, that’s aiming for bringing together the best from both worlds, where devices in both ConfigMgr and Intune can be managed from within the same console, the Microsoft Endpoint Manager admin center (MEMAC). In ConfigMgr Current Branch version 2002, the first set of functionality of this integration has surfaced. With this release, devices managed by ConfigMgr can now be uploaded to the back-end cloud services of Microsoft Endpoint Manager, where administrators have the possibility to perform remote actions on all devices within their organization, without having to think about the management authority of the device itself.
This blog post will focus on the configuration parts of setting up the so called Tenant Attach between ConfigMgr and Intune, making management scenario through MEMAC that was mentioned previously possible.
What is Tenant Attach
You may probably have heard about Co-management at this stage, but what is Tenant Attach and is it the same as Co-management?
Co-management has been around for quite a while now, and it aims at enabling targeted workload management from either ConfigMgr or Intune on a given device. A co-managed device is managed by both ConfigMgr and Intune at the same time. Tenant Attach on the other hand is a bit different. Enabling this doesn’t mean that the device has to be enrolled in Intune, it can be either managed by ConfigMgr or Intune, but to make things more interesting devices can also be co-managed. Tenant Attach is simply a way to attach your ConfigMgr hierarchy to your tenant and leverage the capabilities available from the cloud, such as discovery cloud users and groups, synchronize Azure AD groups from a device collection and more.
At writing this blog, the device management capabilities from within the Microsoft Endpoint Manager admin center aren’t that many, but expect Microsoft to pump resources into enabling more management features in the future.
Prerequisites
Before we jump into the configuration parts of this blog post to set everything up, let’s look at the prerequisites for enabling the upload of devices managed by ConfigMgr so that they can be managed from within the MEMAC:
- ConfigMgr Current Branch version 2002 or later
- An user with Global Admin permissions is required when setting up the tenant on-boarding within the Co-management configuration item
- An Azure public cloud environment
- User accounts that triggers the device actions in MEMAC needs to meet the following prerequisites:
- Discovered with Azure Active Directory user discovery
- Discovered with Active Directory user discovery
- The Notify Resource permission under Collections object class in ConfigMgr
Azure Active Directory user discovery requires you to on-board your Azure AD tenant into your ConfigMgr hierarchy. This configuration is covered very well in the docs from Microsoft and doesn’t need further explanation, but it’s worth mentioning that it’s configured from within the ConfigMgr console under Administration – Cloud Services – Azure Services and the Cloud Management service.
Configure device upload in ConfigMgr
Even though that the enabling of device upload to Intune and manage them from within MEMAC scenario talked about in this blog post isn’t the same as Co-management, it’s configured within the same configuration item (also in the same configuration wizard in the case that Co-management hasn’t been setup in your environment previously). The Co-management configuration wizard has also been updated to let you decide what parts you want it to configure for you when running the wizard. Essentially the Co-management configuration wizard enables you to perform the following two operations, either both at the same time or just one of them:
- Tenant Attach – enable device upload
- Co-management – enroll devices into Intune for management by both ConfigMgr and Intune
In this blog post I’ll cover both scenarios on how to set up the device upload for Tenant Attach, when Co-management and device enrollment to Intune have previously been configured and also when it hasn’t.
Enable device upload when Co-management have not been configured previously
Let’s assume that your environment was never enabled for Co-management and device are only managed by ConfigMgr at present.
- In the ConfigMgr console, go to Administration – Cloud Services and select Co-management. Right-click and select Configure Co-management.
- Ensure that only the Upload to Microsoft Endpoint Manager admin center check box is selected and click the Sign-in button.

- Sign-in with a Global Admin account in the authentication prompt that appears and click Next.
- Click Yes in the prompt to Create AAD Application.

- Select whether to upload all devices within ConfigMgr or rather a set of devices that’s a member of a specific device collection and click Next.

- At the Summary page, click Next. Wait for the configuration to complete
- Click Close once the wizard has completed the configuration

You’ve now configured the device upload functionality. Skip the next section in case you followed the steps mentioned above.
Enable device upload when Co-management have previously been configured
It’s also important to mention, that if you wish to configure only what’s being discussed in this blog post, you don’t need to start enrolling devices into Intune, meaning enabling Co-management fully. We only utilize the same configuration item for Tenant Attach and the device synchronization and remote actions functionality.
- In the ConfigMgr console, go to Administration – Cloud Services and select Co-management. Open the Properties of the CoMgmtSettingsProd item and go to the Configure upload tab. Click the Upload to Microsoft Endpoint Manager admin center check box.

- Select whether to upload all devices within ConfigMgr or rather a set of devices that’s a member of a specific device collection.

- Click OK or Apply. Provide Global Admin permissions in the authentication prompt that appears.

- Click Yes in the prompt that appears to register an application in your Azure AD tenant that will be used to authorize the synchronization of data to Intune.

- If you clicked Apply, the required configuration is now done, so click OK to close the Properties window.
Device upload App registration
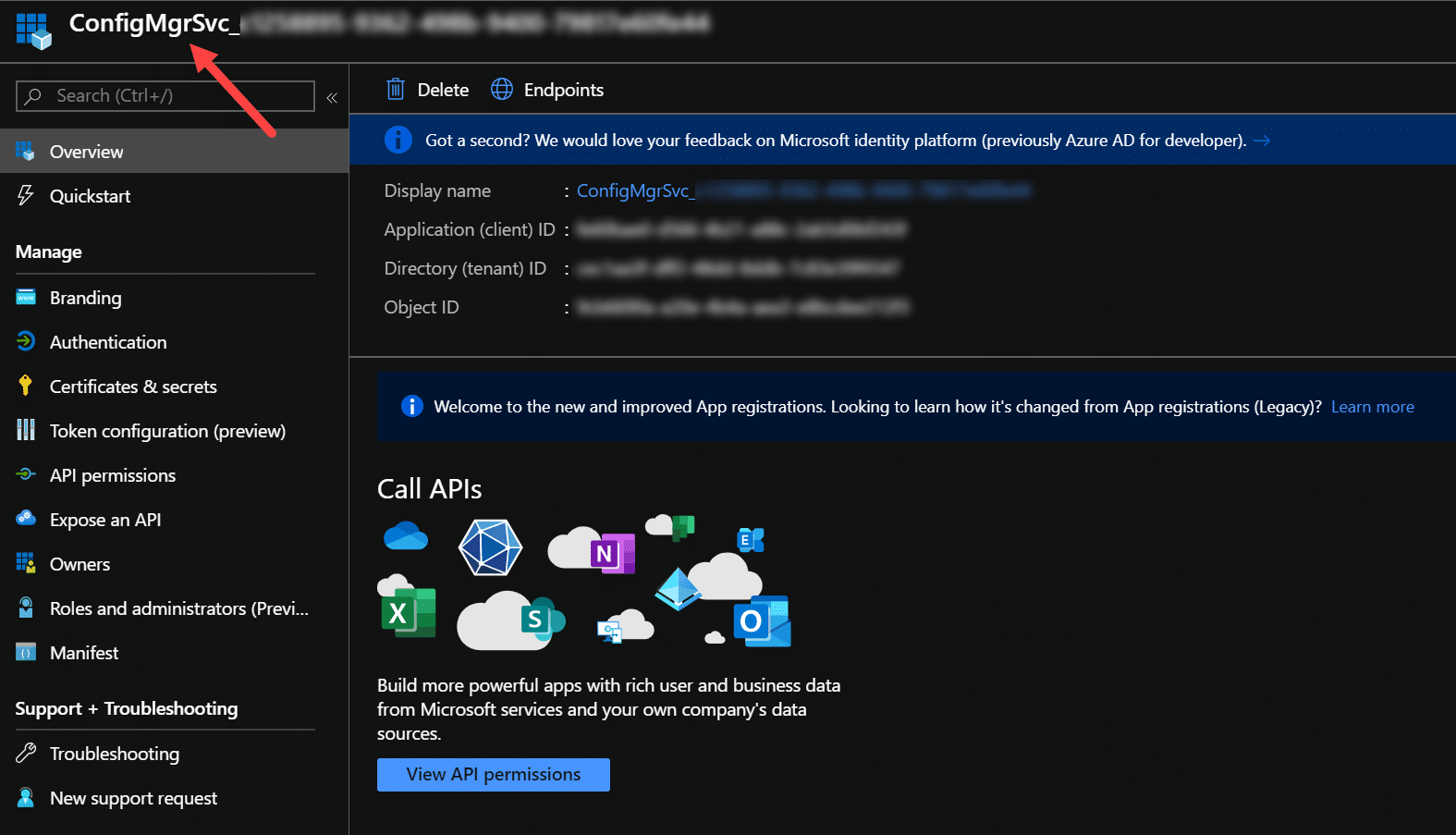
What actually happened in the back-end when asking for registering an application in Azure AD on-behalf of your organization? In the Azure portal under App registration in Azure AD, you should see an application that’s named according to the ConfigMgrSvc_<GUID> naming scheme, looking similar to this:
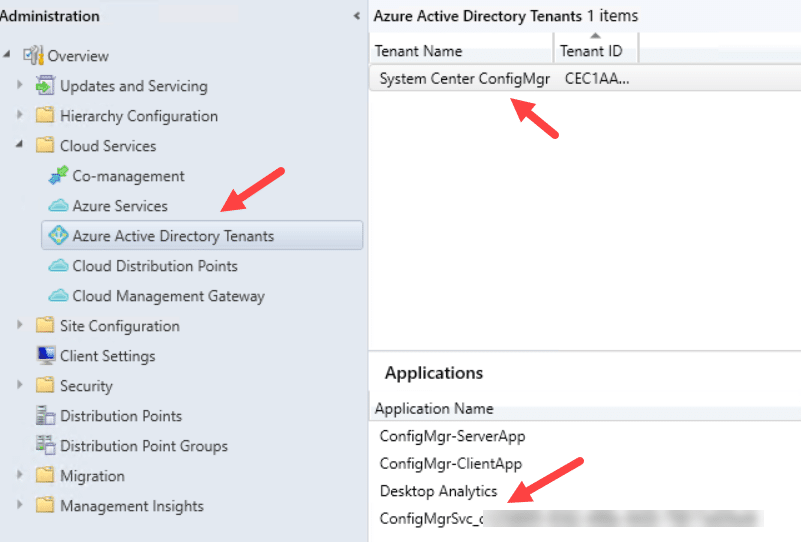
In the event when you’d attach multiple ConfigMgr hierarchies to your tenant, in the ConfigMgr console under Administration – Cloud Services – Azure Active Directory Tenants and the Applications section you’ll see which application name is being associated with the respective ConfigMgr environment:
What’s going on in the background
In the ConfigMgr logs directory on the Site server there’re two log files to make a note of where what we’ve configured up until this point will be logged, these are:
- CMGatewayNotificationWorker.log
- CMGatewaySyncUploadWorker.log
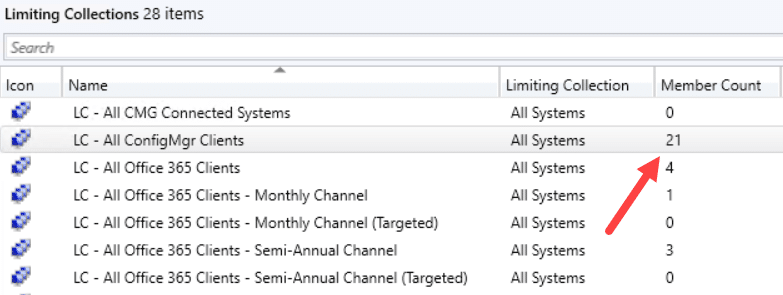
If we look in the CMGatewaySyncUploadWorker.log, we can see that it detected that 21 devices was to be uploaded to Intune:
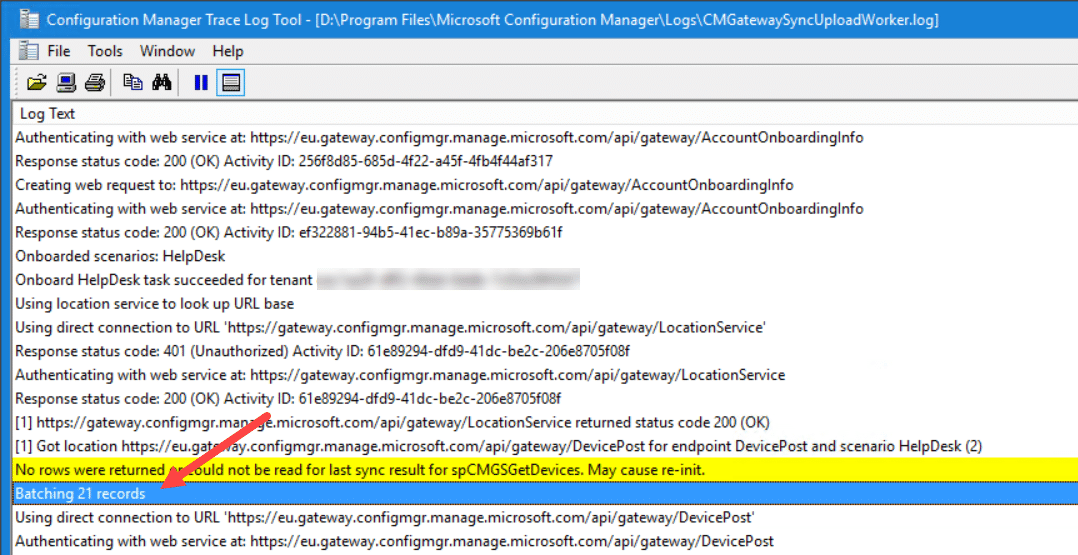
That correlates to the amount of devices currently in this environment that I’m using to set this up:
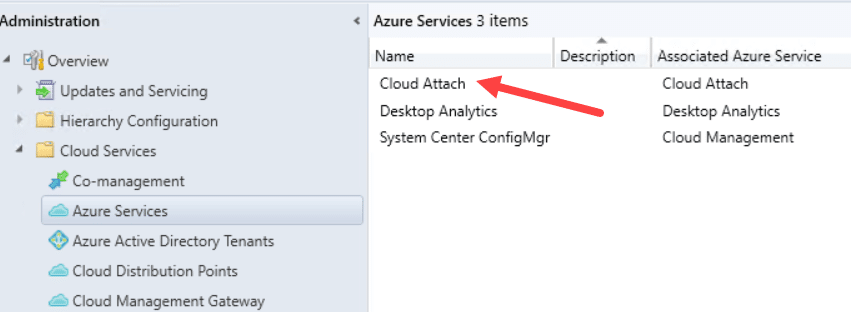
Under Administration – Cloud Services – Azure Services in the ConfigMgr console, there’s a new Cloud Attach service that has been added. There’s no configuration options for it, it just sits there doing it’s thing:
Invoking remote device actions for uploaded devices
From within the Microsoft Endpoint Manager admin center (devicemanagement.microsoft.com) under Devices – All devices, all devices that was uploaded from ConfigMgr are now visible to be remotely managed:
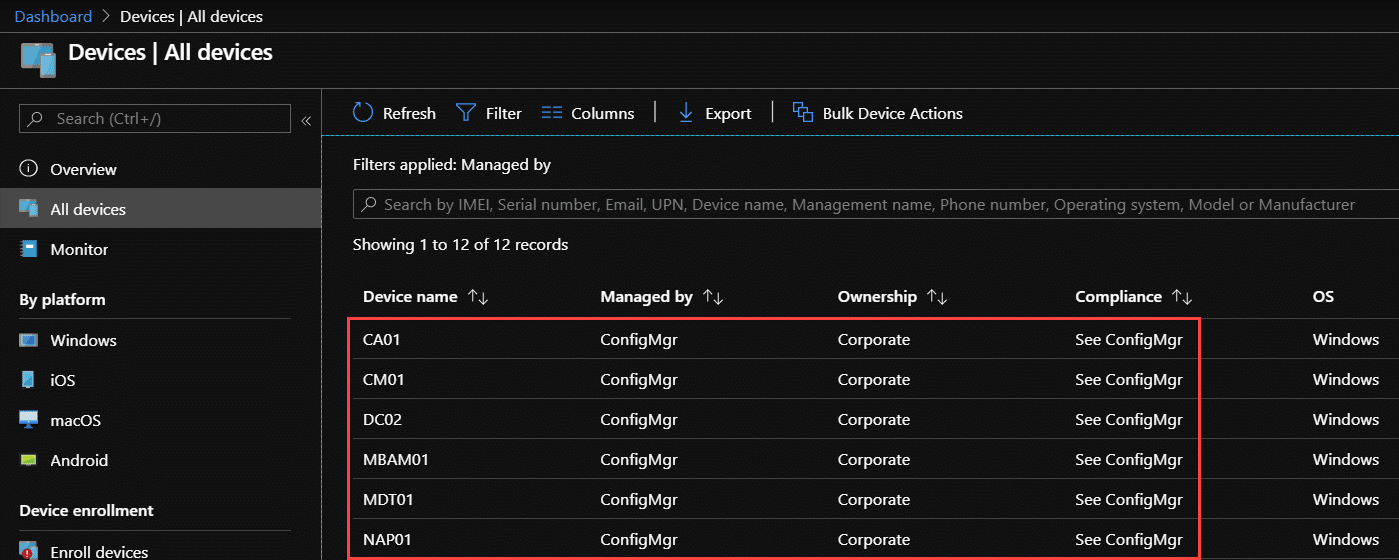
As the screenshot shows, it’s also so now possible to see your Windows Servers in the admin center, pretty cool right? In the view above, devices have been filtered on the Managed By attribute of ConfigMgr, to easily being able to distinguish what devices are managed by which platform. Unfortunately you can’t view the uploaded devices through the Devices – By Platform (Windows) – Windows devices as of yet, but I’m assuming that will be added in the future.
Clicking on any of these devices takes you into slightly different device blade that gives an overview of the device but also shows what remote device actions that can be triggered:
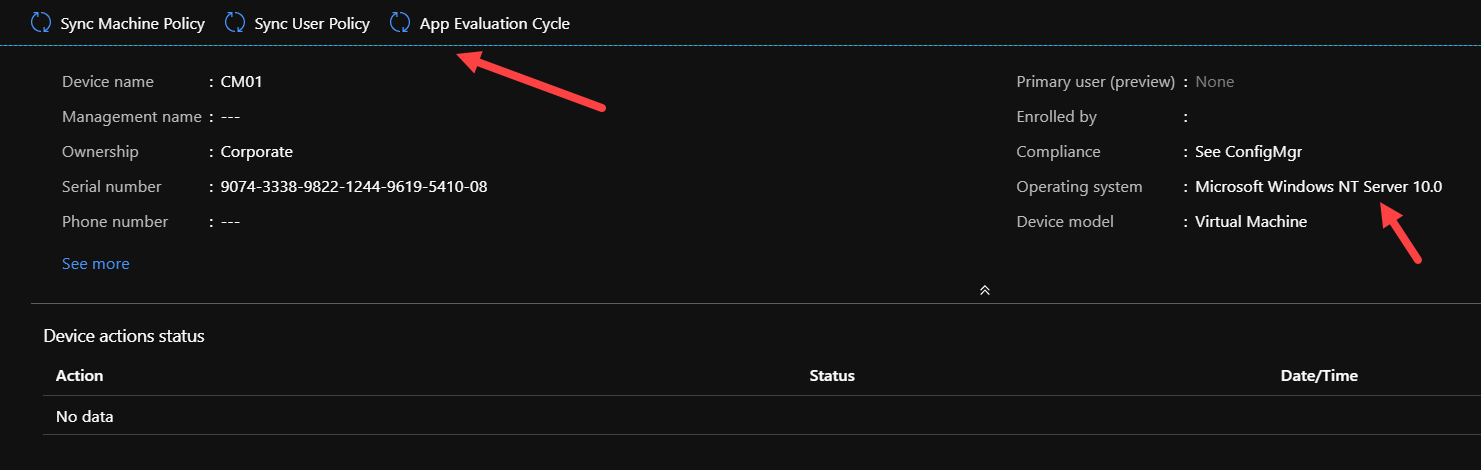
As you can see, the options are not that many as of yet, but to demonstrate the functionality, let’s trigger a Sync Machine Policy and follow the logs to see what goes on behind the scenes:
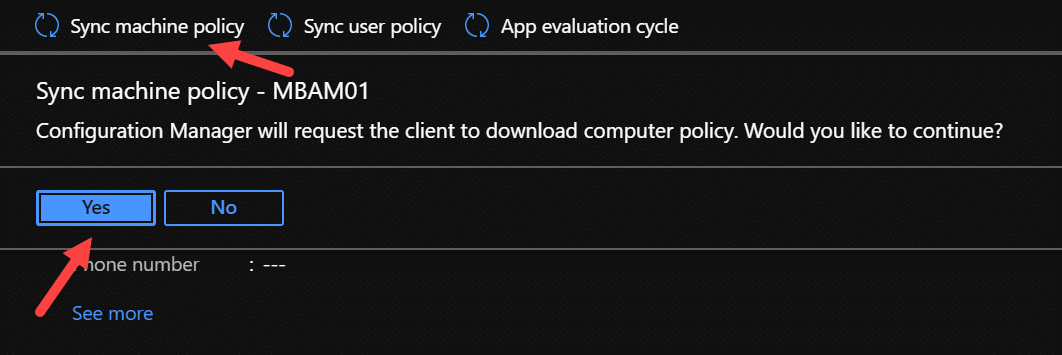
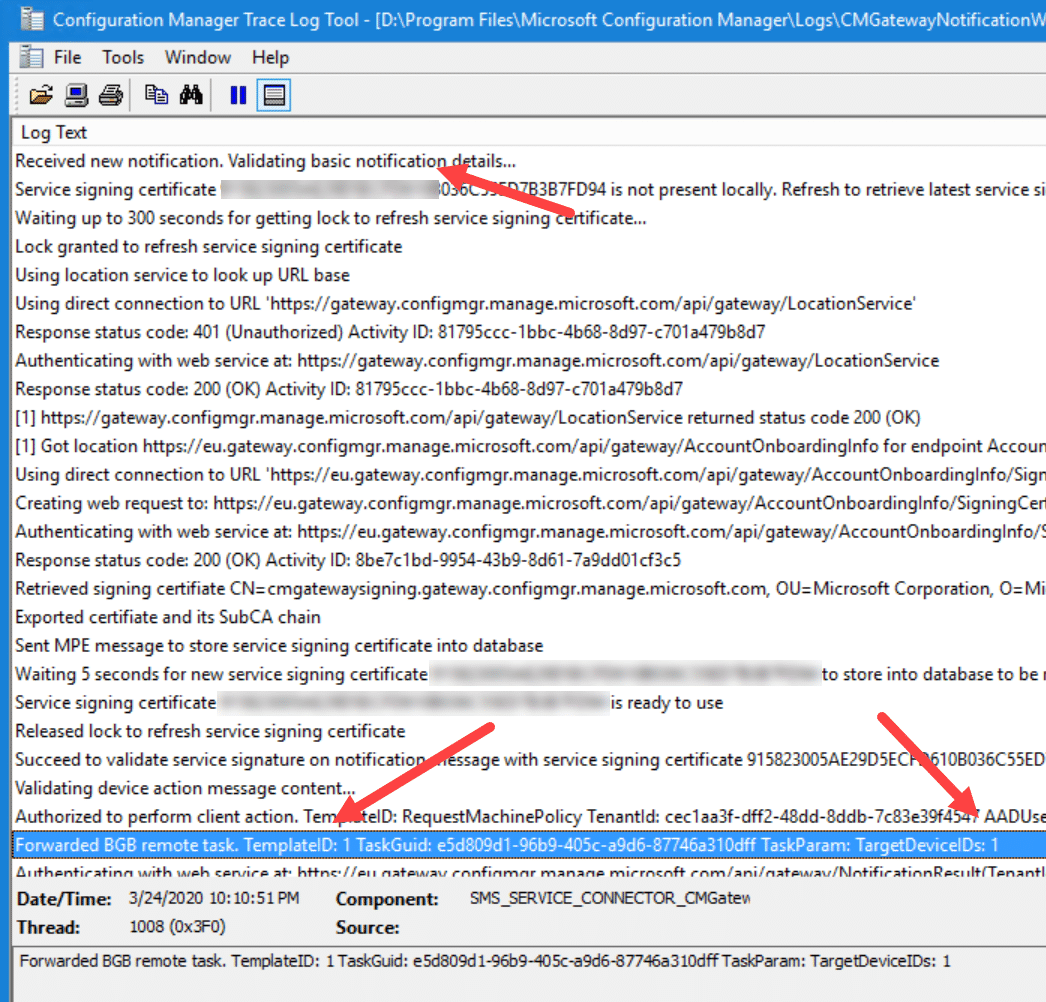
In the CMGatewayNotificationWorker.log on the Site server you’ll notice that a new notification was received and that it then triggered the machine policy sync using the BGB channel (also known as the Fast channel):
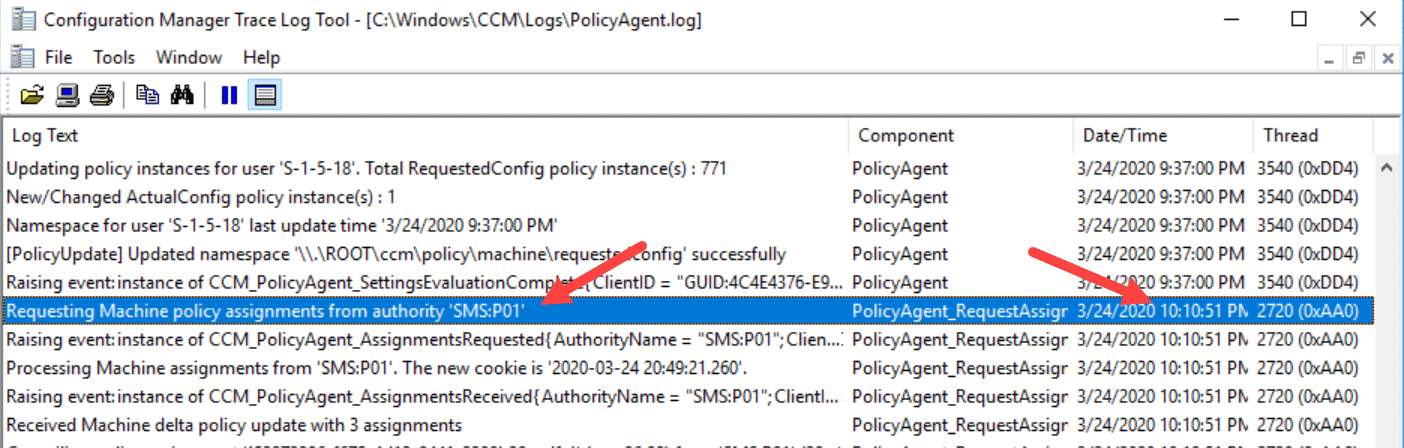
Looking further in the PolicyAgent.log locally on the MBAM01 server (that’s the server that I chose to trigger the machine policy sync on) the log shows that a sync was indeed triggered:
Summary
If we just sit down for a minute and think of what we’ve talked about in this blog post, cause it’s pretty darn impressive. Essentially, we’ve taken devices (even servers) managed only by ConfigMgr, uploaded or rather synchronized with Microsoft Endpoint Manager (or actually Intune), seen the device from within the MEMAC portal and initiated a machine policy refresh that within a seconds trigger the action locally on the server. Now if you don’t think that’s cool, think again. I can’t wait to see what’s in store for the future with and what’s going to come out from Redmond around this integration between ConfigMgr and Intune from within the Microsoft Endpoint Manager admin center.










Add comment