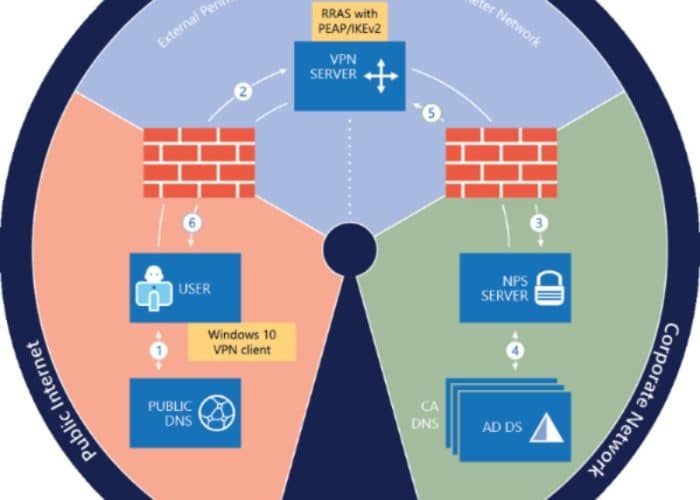
The Microsoft Always On VPN Solution that is pushed by Microsoft as the successor to DirectAccess, is a great tool for remote workers and admins alike because it’s always on – or is it?
Despite the high level of skills required to implement this technology, many try out their luck with the official documentation from Microsoft, only to end up at the troubleshooting section at https://docs.microsoft.com/en-us/windows-server/remote/remote-access/vpn/always-on-vpn/deploy/always-on-vpn-deploy-troubleshooting. Which just scratches the surface of some of the woes you will have with this technology…
But setting all the configuration issues aside for a moment… I think that anyone working with Microsoft Always On VPN infrastructure and client configuration has run into an issue where user tunnel connections don’t always auto-connect – despite having configured “AlwaysOn” in the ProfileXML or Intune configuration policy.
Some hacks to fix this, include scheduling the “rasdial <connection name>” command to re-establish the connection, but wouldn’t you rather know why it has stopped auto-connecting?
Why is it not auto connecting then?
This might have happened because the user manually disconnected the user tunnel at some point in time, or because of something that is yet to be explained.
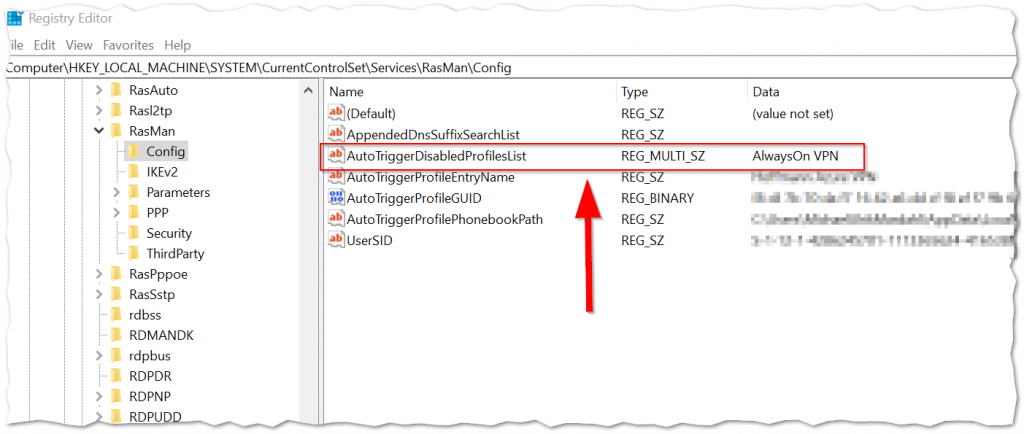
In any case – what happens is, that this lands the VPN connection on a list in the registry called AutoTriggerDisabledProfileList which is a REG_MULTI_SZ property type that you might be interested in clearing out the Always On VPN connection name from.
Can Intune help me fix this?
Sure! You could use PowerShell to achieve this goal in a crude fashion or even better create a .intunewin package that removes unwanted entries with a detection rule that looks for a certain value on this registry property.
I have yet to create this package, so please feel free to share in the comments, as I am sure it could save a lot of people some extra time.
For the detection method you could use:
$connectionName = "Always On VPN Connection Name"
if((Get-ItemProperty -Path HKLM:\SYSTEM\CurrentControlSet\Services\RasMan\Config | select AutoTriggerDisabledProfilesList -ExpandProperty AutoTriggerDisabledProfilesList) -icontains $connectionName){
Write-Host "Found connection: $connectionName in disabled profile list!"
exit 1
}Can I disable the users ability to disconnect?
Sure you can! And what a wonderful way of avoiding to have to fix this issue all together. Unless of course there is an actual need for the user to be able to disconnect from time to time? 🙂
Microsoft has a device CSP that you can deploy with a custom OMA-URI to disable the disconnect button. and it looks a little like this:
./Device/Vendor/MSFT/VPNv2/{ProfileName}/DisableDisconnectButton
Just remember to include a %20 for any spaces in your VPN profile name!
Read info about this CSP and other at: https://learn.microsoft.com/en-us/windows/client-management/mdm/vpnv2-csp#deviceprofilenamedisabledisconnectbutton
Final thoughts
Adding a fix via Intune nicely complements the fact that Intune is the preferred distribution mechanism for the Always On VPN profiles. And even though this seems like a bug, it’s a feature, and as such it might never end up on the troubleshooting page.
But I would have liked an option within Intune’s VPN CSP that disables this feature for those organizations with explicit requirements for users to be connected via VPN at all times.
Thats it for me this time – as always I hope you will do me the honor of following me on Twitter (@michael_mardahl).







OK that comment got mangled, I can email you the scripts so you can format them properly if you want.
I’ve turned this into two PRs. First detect if it’s been autotriggerdisabled (just realised this might need a -ErrorAction SilentlyContinue):
DetectAOVPNAutoDisabled.ps1
if ( (Get-ItemProperty -path “HKLM:\SYSTEM\CurrentControlSet\Services\RasMan\Config”).AutoTriggerDisabledProfilesList.Contains(“AOVPN”) ) { exit 1 }
exit 0
If so, remove it from there:
RemediateAOVPNAutoDisabled.ps1
try {
$a = ((Get-ItemProperty -path “HKLM:\SYSTEM\CurrentControlSet\Services\RasMan\Config”).AutoTriggerDisabledProfilesList -ne “AOVPN” )
Set-ItemProperty -path “HKLM:\SYSTEM\CurrentControlSet\Services\RasMan\Config” -name AutoTriggerDisabledProfilesList -Value $a
exit 0
} catch {
$errMsg = $_.Exception.Message
Write-host $errMsg
exit 1
}
Then the next PR detects it’s been disabled and we’ve removed it from the AutoTriggerDisabledProfilesList:
DetectAOVPNNoAuto.ps1
# The first script will remove the VPN from AutoTriggerDisabledProfilesList, but the auto-connect won’t be re-enabled. Since it requires GUIDs and per-user paths, just remove it and let Intune reinstall it.
if ( -not (Get-ItemProperty -path “HKLM:\SYSTEM\CurrentControlSet\Services\RasMan\Config”).AutoTriggerDisabledProfilesList.Contains(“AOVPN”) -and -not (Get-ItemProperty -path “HKLM:\SYSTEM\CurrentControlSet\Services\RasMan\Config” -name AutoTriggerProfileGUID -ErrorAction SilentlyContinue) ) { exit 1 }
exit 0
Then just straight up remove it, on the next sync Intune will see it’s gone and put it back, with the automatic trigger enabled:
RemediateAOVPNNoAuto.ps1
# Remove the VPN connection, Intune will send it out again
try {
Rasphone -r “AOVPN”
exit 0
} catch {
$errMsg = $_.Exception.Message
Write-host $errMsg
exit 1
}
I tried using delete-vpnconnection but it just hung execution, even with -force, and even just running it manually, so switched to rasphone -r.
I set the scripts to run hourly otherwise it can take a while for them to run in the right order and then Intune sync to occur and send back the VPN.
That is cool James!
Thanks for giving back. I am sure many readers can use this.
Hello Michael, 2020-07July-28
I followed the path you specified “Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\RasMan” However the last folder “\Config” does not exist on my machine. As such I’m unable to find the AutoTrigger Disables Profile List.
Odd that this is the case … How to proceed?
If you don’t have the key, then you most likely do not have the issue.
The key does not exist until the system creates it. it’s not a default.
Hi Michael,
There is also a line in configuration called AutoTiggerCapable (seems like a typo, it should be “Trigger”) located inside of rasphone.pbk file (open with notepad) located for example in C:\Users\user\AppData\Roaming\Microsoft\Network\Connections\Pbk which is handling whether the connection will have the option to “Connect automatically” in VPN settings. This value can be set to 0 (AutoTiggerCapable=0) and users won’t have the option to keep the connection alive all the time (this was required in our environment). In case the “Connect automatically” is required to be available / enabled, set the value of this line to 1 (AutoTiggerCapable=1).
Hi @Peha1906,
Tried your way to autoconnect but it doesnt. Do you have anyother suggestion