Locking Down The Workstation
Security is on everyone’s mind these days, and well it should be as threats pose both a risk for downtime for your employees and lost revenue through business interruption or reputational damage.
As you transition from traditional to modern management with Azure AD and Intune taking control of your infrastructure, it is important to understand the baseline options available to you to secure your devices. So in this post we will look at securing windows devices through the inbuilt policies in Intune, covering areas such as password complexity, browser security, antivirus prevention / detection and other Windows restrictions that should make life easier for the IT department by ensuring their users do not stray into area’s of the OS they shouldn’t.
Note: The settings contained within the examples are there for demonstration purposes only. They should not be considered as a approved security baseline, but as a suggestion of the minimum security levels I would deploy.
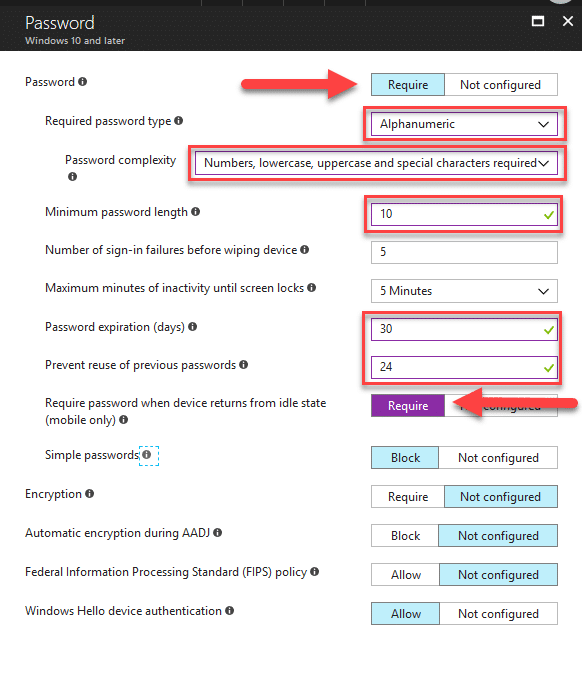
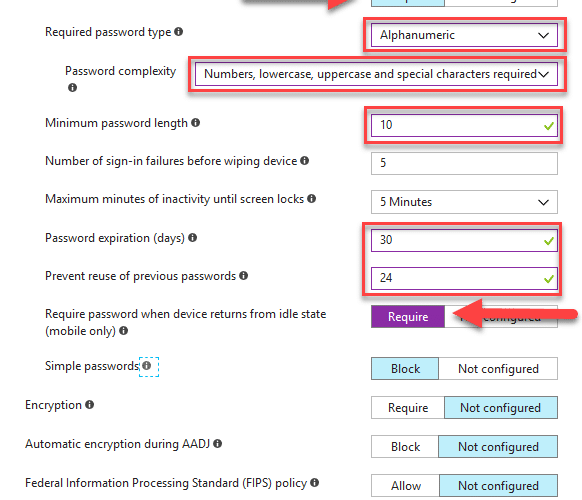
Passwords
Lets start off with the very basics and look at password complexity requirements. Those of you familiar with active directory security policies will know the inbuilt options for complexity, and their shortcomings (which I will touch on later). You will be either glad or dismayed to hear that the same level of control is carried over to Intune, personally I think this is somewhat of a lost opportunity to improve upon the situation where “P@ssword1” can be considered a complex password though.
So lets start with creating a password policy;
- Log onto the Azure Portal
- Select the Intune option from the blades on the left of the screen
- Click on Device Configuration
- Underneath the Manage section click Profiles
- Click on the +Create profile button
- Give your Policy a name, e.g Security Profile
- Select the Platform as “Windows 10 and later“
- Select the Profile Type as “Device Restrictions“
- Click on the Password section under Device restrictions
- Here you can specify your minimum requirements, example;
- Click OK to save the settings
In the above example I have highlighted the key areas I would be concerned about when rolling out password policies. This should help to ensure passwords are frequently changed and a complexity / length requirement is met.
Security Improvements
I would like to see the complexity requirements extended in the future to allow for dictionary based matching to prevent users from using less complex constructs to their passwords. An excellent example of how to do this on-premise is through the likes of SpecOps Password Policy, or another filter based method to control the complexity requirements. Microsoft do provide the option for custom policies in the Azure AD B2C offering, however it would be nice to have it built in for all.
More information on the capabilities of Azure AD password policies can be found here – https://docs.microsoft.com/en-us/azure/active-directory/active-directory-passwords-policy
Browser Security – Edge
Another one of the key requirements or complaints that you might here when we talk about moving away from GPO based restrictions, is that of browser security. Now lets talk about Microsoft’s latest browser Edge, love it or hate it, but Edge is here and the good thing is that it can be managed in much the same way that IE is managed through GPO’s.
So using the same policy we can add in security restrictions for the browser;
- With the Security Profile – Settings still open, click on Edge Browser
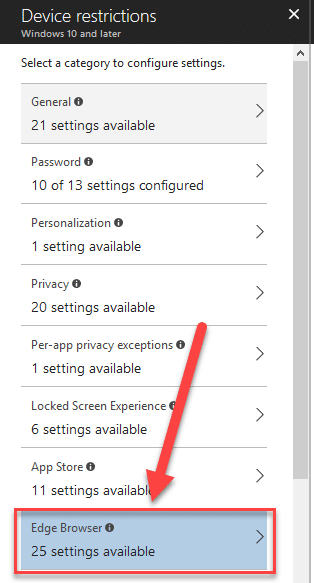
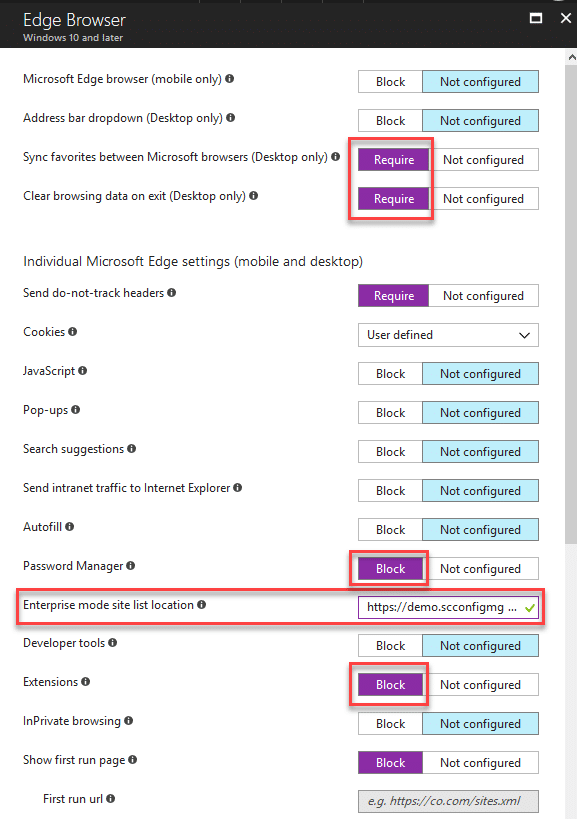
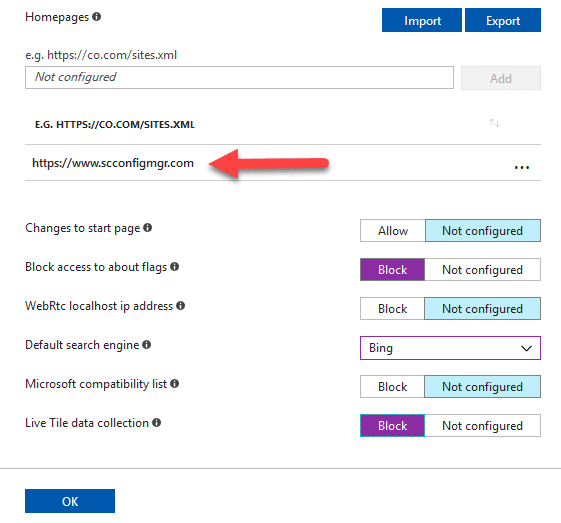
- In the below example I have configured some security hardening features
- prevent sensitive data being stored (passwords)
- prevent website tracking
- ensure that the users’s start page is consistent
- ensure that enterprise model URL’s are adhered to by setting the location of the hosted XML (read over https)
Note: For enterprise mode list generation you will need to create an XML using the Enterprise Mode Site List Manager, available from this download link – https://www.microsoft.com/en-us/download/details.aspx?id=49974
Antivirus / Malware
Here we deal with the traditional antivirus and malware prevention settings, through Windows Defender of course in this instance. Like BitLocker in Windows 10, many organisations are turning to Microsoft’s own in-house products rather than go down the third party route. The best part of all of course is that the product is included in the OS, therefore there is no need for application deployment.
There are two schools of thought about this and I am not going to argue over the virtues of one product over the other in this post, so lets deal with applying the settings to secure the device using what we have out of the box:
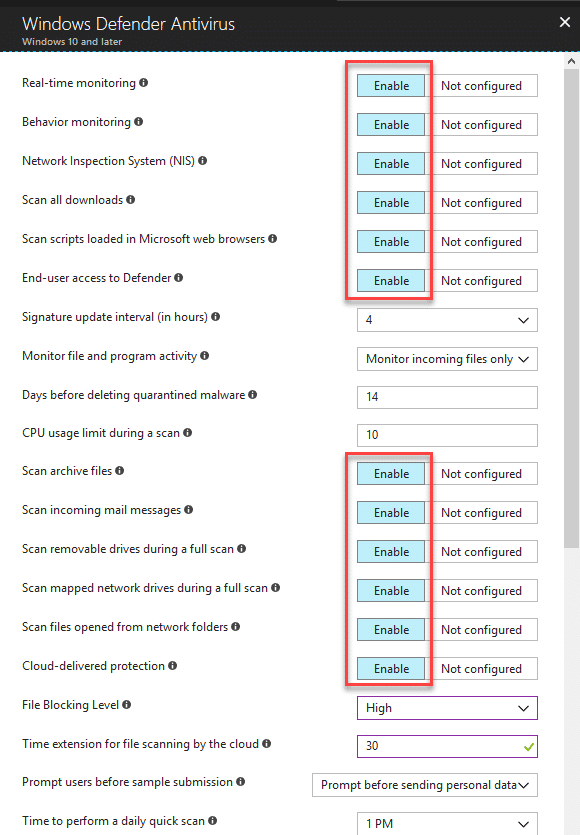
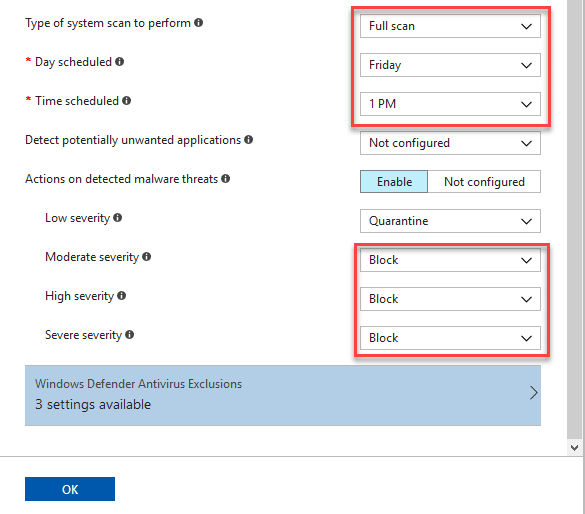
- Under Device Restrictions click on Windows Defender Antivirus
- In the below example I have configured a profile that should provide sufficient production without impacting on CPU performance during full scans:
- Exclusions for AV processes can be included by clicking on the Windows Defender Antivirus Exclusions button, but this should be on a specific requirement basis

- Click on OK to save the settings
Control Panel & Settings
The settings we are about to block / restrict here are all about ensuring that your employees do not stray into area’s of the OS which they do not need to. As with most things in IT, prevention is the best form of cure, so with that in mind lets look at the below example;
- Under Device Restrictions click on Control Panel and Settings
- Lets start off with blocking access to the System and Device Manager
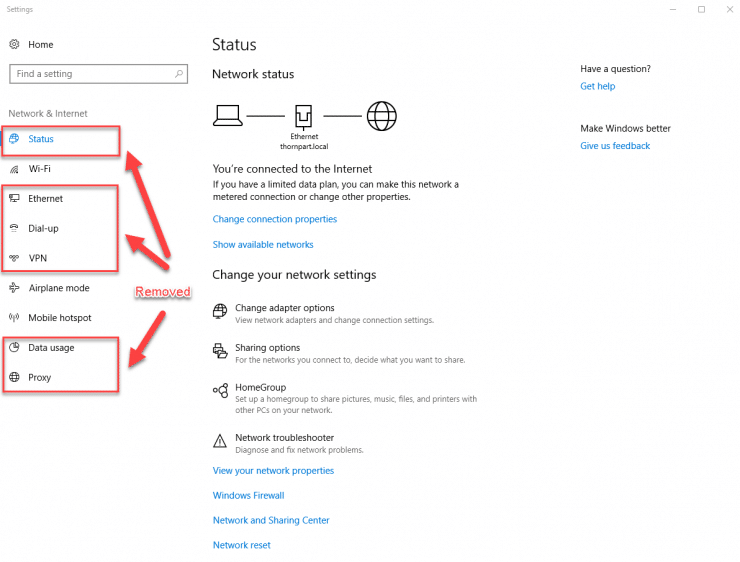
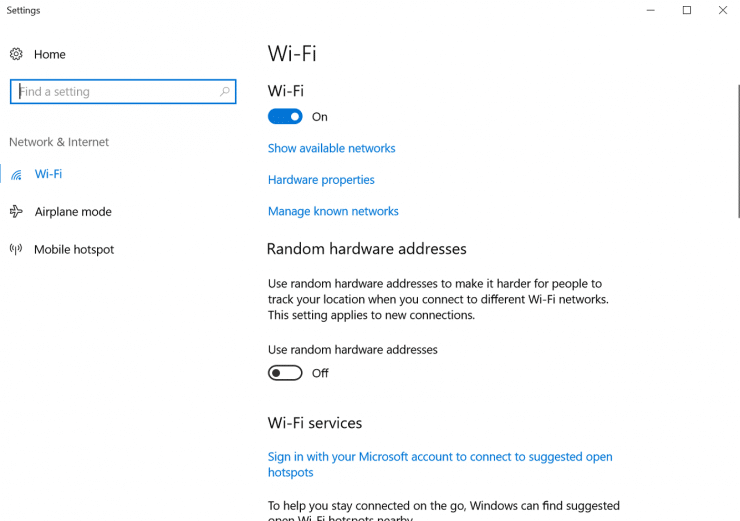
- Now lets block the Network and Internet settings to aid to prevent users from changing network settings
- Finally lets block access to the Apps, Accounts and Gaming settings
- At this stage if you are following this you will have a screen similar to the below:
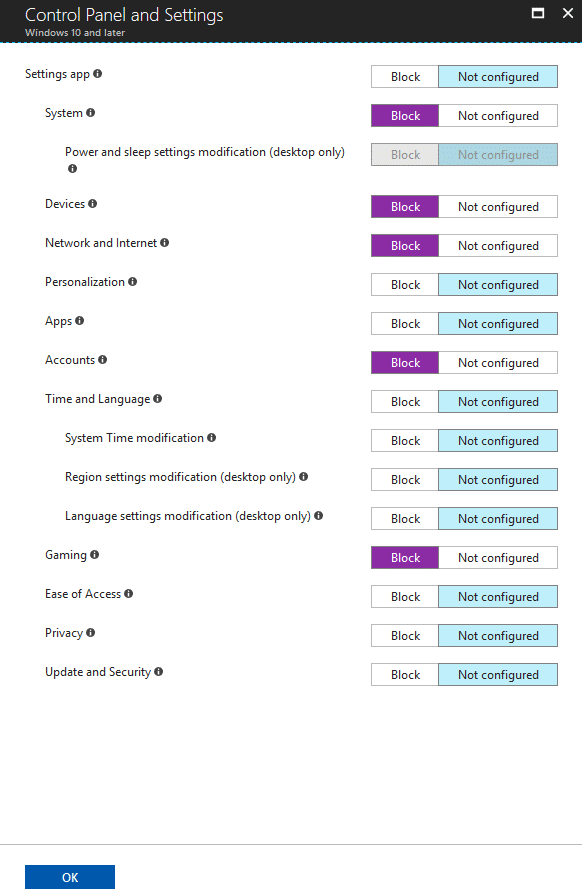
- Click OK to save the settings
User Experience
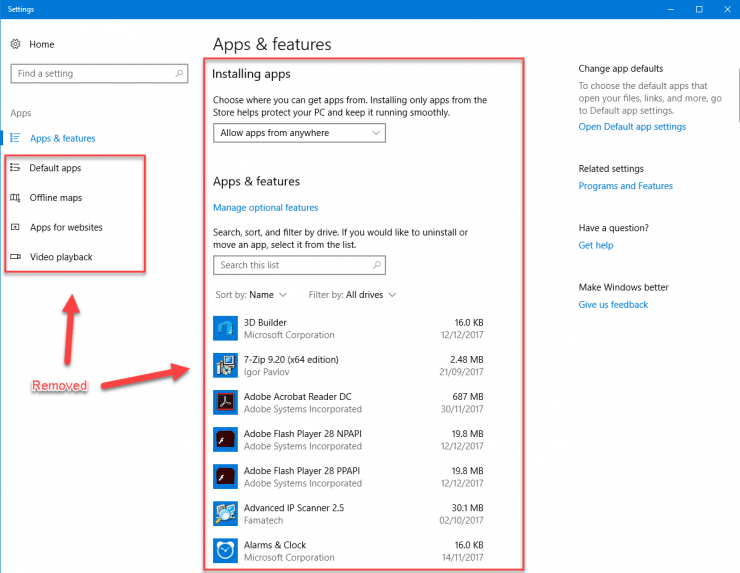
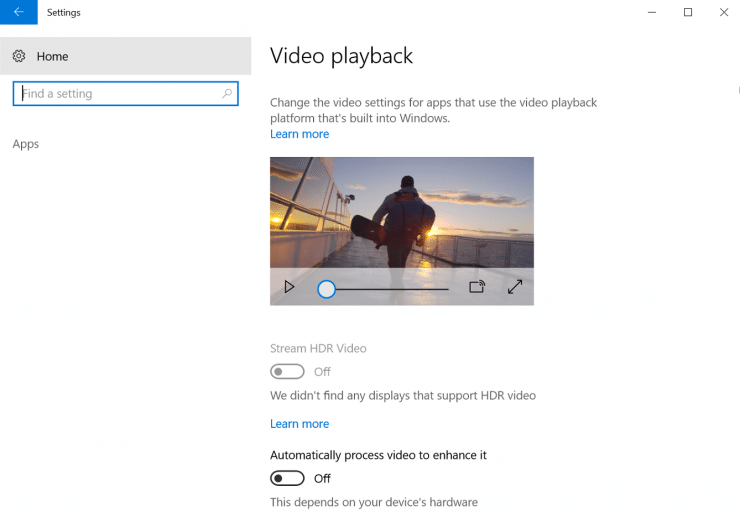
So what does this look like for the end user?. Lets review what the “Apps” and “Network and Internet” sections of settings looks like both in pre and post lock down scenarios:
Apps
Network and Internet
Conclusion
At this point I have now demonstrated some of capabilities of basic security settings in a modern management scenario with Microsoft Intune. This should open your eyes as to the capabilities of the product and help you to compare these to how you currently manage your traditional AD GPO locked down environment.
Series Links
- Traditional Management vs Modern Management – Part 1 – Encryption
- Traditional Management vs Modern Management – Part 2 – Office 365
- Traditional Management vs Modern Management – Part 3 – AAD/Auto MDM Enrollment
- Traditional Management vs Modern Management – Part 4 – Windows AutoPilot
- Traditional Management vs Modern Management – Part 5 – Security









Hey, thanks for your great post.
But I have a little understanding problem. For which accounts is the password policy for. From my point of view: Synced Accounts / Federated Acconts get the on-premises password policy; cloud only accounts get the password policy from Azure AD. What is the (in fact) device-based password policy used for?
Hi Simon,
The scenario here is for organisations who are moving away from their traditional on-premise infrastructure and are consuming all services from Azure / Intune. In this instance the Intune password policy is used for improving the security of the local workstation/device, which is separate of course to Synced/Azure AD account passwords which have their own governed password policy.
Maurice