Intune App Factory was originally developed and instructions for how to set it up were written when Azure DevOps didn’t support Managed Identities or Workload identity federation. However, recently, users of Intune App Factory may have noticed that the pipeline would immediately fail on the first step, with an error similar to the following:

Further investigating this, you should also see that there’s an error when attempting to retrieve the secrets of the Key Vault in the Library variable group named KeyVault:

This error is related to the Service Connection that’s setup in Azure DevOps, to Azure Resource Manager, where it’s not able to use the provided credentials from the App Registration and it’s client secret.
How can we restore access to Azure Resource Manager?
From within the Project in Azure DevOps, where the Intune App Factory is running, click on Project Settings in the left corner at the bottom and browse to Service Connections.
Here, we can see that there’s a security related notification that is asking us to convert an existing Azure Resource Manager service connection, by enabling Workload identity federation instead of making use of a client secret.

Click on the service connection.

Another notification appears right at the top, where we’re given an Convert button.
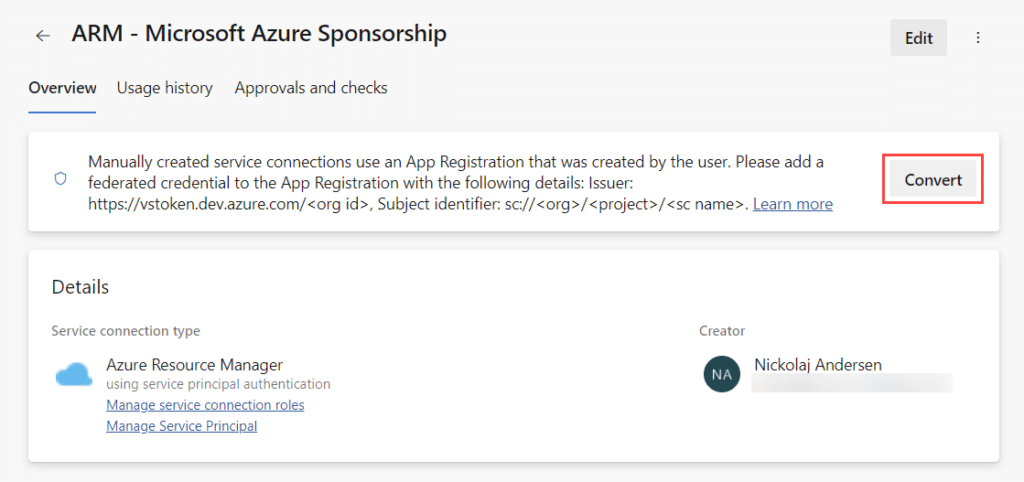
But before we click on the Convert button, we must update the service principal (App Registration) in the Azure portal. Browser to portal.azure.com and open the Microsoft Entra ID blade. Go to App registration and search for the service principal. It’s important that you ensure you make the following changes on the correct service principal, to not cause service interruption.

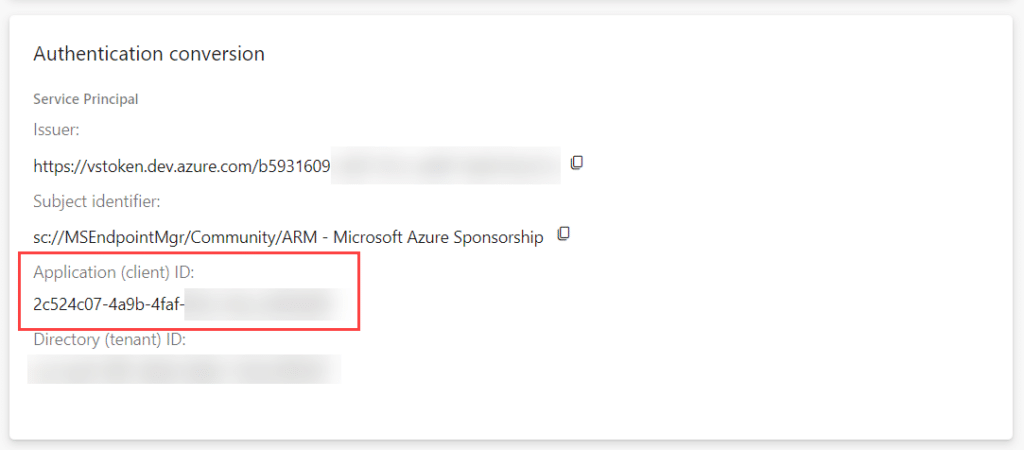
You can verify that the Application (client) ID identifier from the Azure portal, is the same that’s mentioned for the service connection in Azure DevOps, under the Application (Client) ID field for Authentication conversion:
When the correct service principal is found, click on it and then go to the Certificates & secrets blade. Click on the Federated credentials tab and click Add credential.

Select Other issuer as Federated credential scenario. In the Connect your account section, copy and paste the Issuer and Subject Identifier from the Authentication conversion section of the service connection in the Azure DevOps portal. Provide a name for this credential, e.g. some that is distinctive for its usage.
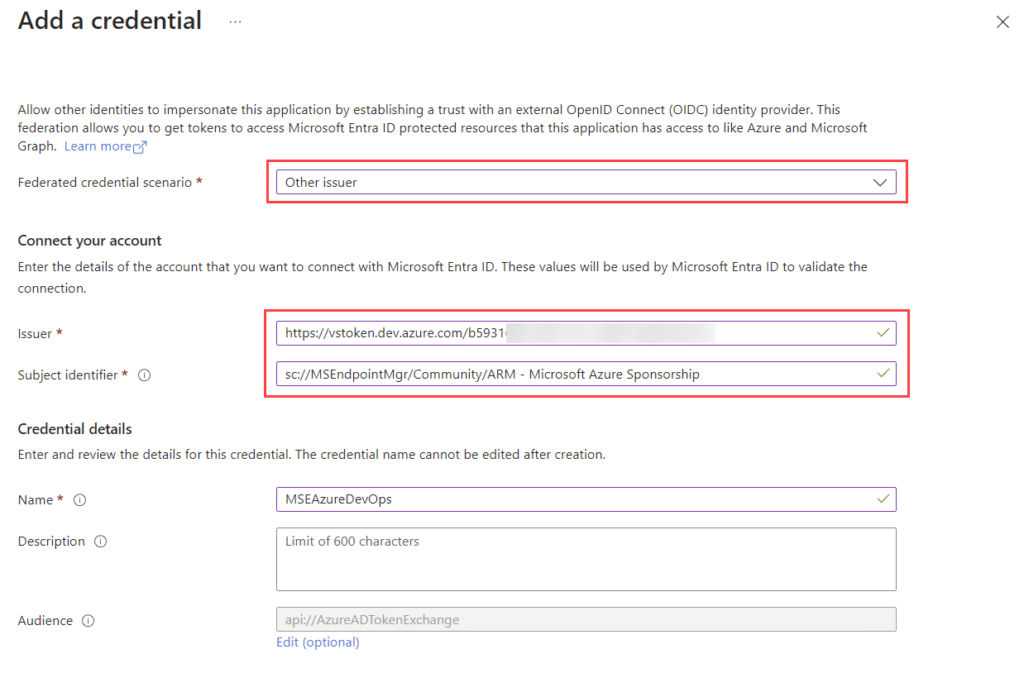
Click Add.
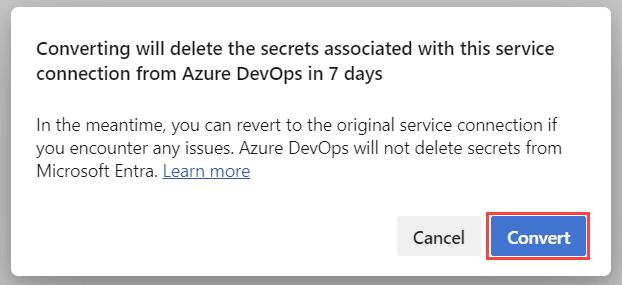
Back in the Azure DevOps portal, click Convert.
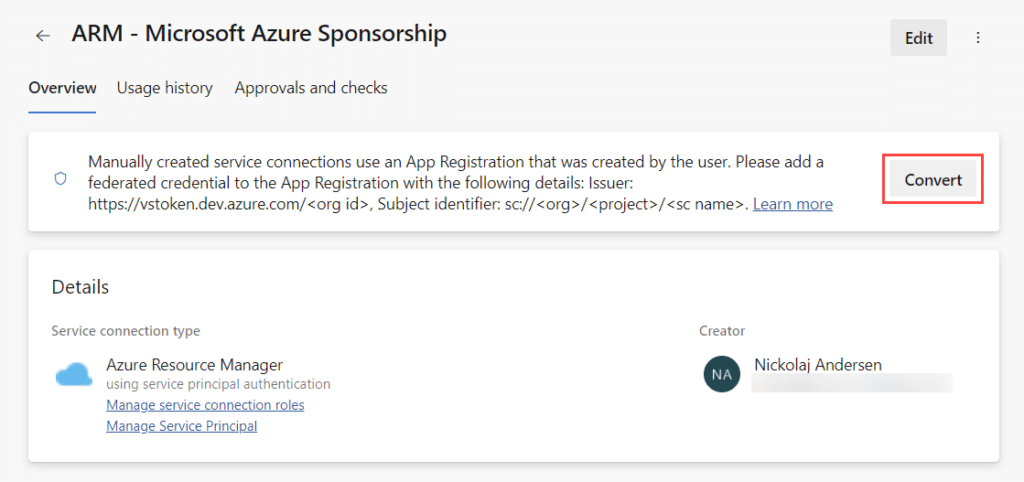
This brings up a warning about client secrets for this service principal (App Registration), will be removed, which is fine. We want to remove and stop using the client secret and convert the service connection into a Workload identity federation service connection instead, using the same service principal.
Click on Convert again.
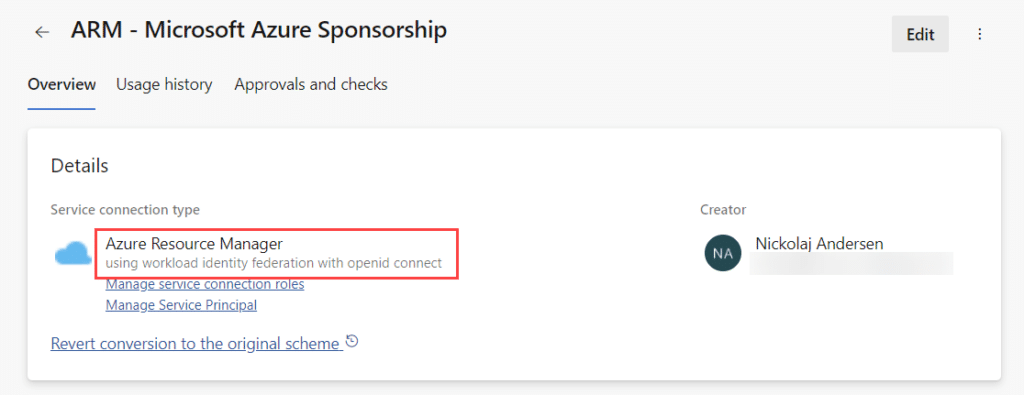
After a while, once the conversion completes, verify that the service connection is now setup as using workload identity federation:
And with that, the issue is fixed! Verify it by executing the pipeline manually, and you should see that the “Download secrets: <KeyVaultName>” steps are now working again.










Add comment