Managing Apple devices with Microsoft Intune requires you to have an Apple MDM Push certificate. Apple requires administrator to renew these certificates every 365 days. As of today, Microsoft Intune does not have any monitoring service for the expiration of these certificates, other than it’s shown in the console when it will expire. A common request that I’ve got from customers have been to somehow monitor when the Apple MDM Push certificate will expire, and get notifications before it happens.
Since a couple of months back, as of writing this post, we’re not able to retrieve the expiration date for an Apple MDM Push certificate through the Graph API. Previously, we could only rely on the data shown in the console or set a calendar reminder for when the certificate would have to be renewed. In this blog post, I’ll share a solution that I’ve written in PowerShell and designed for being implemented with Azure Automation to monitor the expiration of the Apple MDM Push certificate used in a given tenant.
Getting started with Microsoft Intune and Azure Automation
If you’re new to automating tasks in Microsoft Intune using the Graph API and Azure Automation, I suggest that you read my post about how to get started. It’ll cover everything you need to setup that I’m not covering in this post. Read the blog post about getting started here:
Getting started with Microsoft Intune and Azure Automation
PowerShell script overview
The script that is being used in this solution to monitor the expiration of the Apple MDM Push certificate has been written for Azure Automation. However, it’s not a PowerShell Workflow, in fact just a basic PowerShell script. With some customization of the script, it should be fairly easy to use it with a scheduled task running it on-premise in your environment.
This script is by default set to perform the following tasks:
- Retrieve the Apple MDM Push certificate from your given tenant
- At execution, check if the remaining days of the certificate is less today’s date. If so, it’ll send a notification email about the expired certificate
- If the certificate has not expired, it will check if the remaining days until the certificate expires is within the notification range, set by default to 7 days.
Script prerequisites
Using this script requires a few things to be in order before it can be put into production. First of all, it comes with support for Office 365 but it can easily be amended to support any other mail service. In addition, you’d need to setup the following:
- User account with a mailbox
- This should be a user in your tenant that has a mailbox and is capable of sending emails. When the script sends notifications it’s sending on behalf of this user.
- Azure Automation variables
- You need to create two variables containing the piece of information required for authenticating against Graph API. These variables are described in the getting started post that’s referenced above. These are the required variables:
- AppClientID – should be a string with the ApplicationID of your app registration, or use the default value for the Microsoft Intune PowerShell enterprise application.
- TenantName – should be a string with the tenant name of your organization, e.g. domain.onmicrosoft.com.
- You need to create two variables containing the piece of information required for authenticating against Graph API. These variables are described in the getting started post that’s referenced above. These are the required variables:
- Azure Automation credential
- MSIntuneAutomationUser – should be an Azure Automation credential for the user account that is going to send email on behalf of this script.
- Azure Automation modules
- AzureAD – add this module from the PowerShell Gallery, it’s required for the PSIntuneAuth module.
- PSIntuneAuth – add this module from the PowerShell Gallery.
I’m not going to cover how to setup all of the things mentions above, many of them are already covered in the getting started with Microsoft Intune and Azure Automation blog post.
PowerShell script
You can download the script that’s used to monitor the Apple MDM Push certificate expiration from our GitHub repository:
Create a runbook in Azure Automation
To set all of this up, you need to create an Azure Automation runbook. Assuming you have an Azure Automation account setup, but if not, reference the official documentation for creating one:
https://docs.microsoft.com/en-us/azure/automation/automation-create-standalone-account
Create the runbook
If you’ve not created the requirements for the script, please go back and make sure they’re all in place before you continue. With all the prerequisites in place, we start off with creating the runbook in Azure Automation.
- Login to the Azure portal and go to your Automation Account.
- Select Runbooks and click Add a runbook.
- Name the runbook e.g. Get-AppleMDMPushCertificateExpiration and select PowerShell as the Runbook type.

- Click Create.
- You’ll be taken directly into the editor of the newly created runbook. Paste in the script from the GitHub URL above.
- Edit the script after the Define email information details comment section to something more suitable for your environment.

- Click Save.

- Click Publish and Yes in the prompt that appears.

- You’ve now setup the runbook using the script to monitor the Apple MDM Push certificate. Before you continue to setup a schedule for it, it’s recommended that you validate that everything is working by simply starting the runbook.
- Click Start.

- Click on Output and wait for the runbook to complete. If successful, it should look something like this:

Create a schedule
Your runbook is now setup and it’s working well, to utilize this script fully and completely automate the process of monitoring the Apple MDM Push certificate, we need to add a schedule to the runbook.
- In your Automation Account, select the Get-AppleMDMPushCertificateExpiration runbook and click on Schedule.

- Select Link a schedule to your runbook and click Create a new schedule.
- Configure the schedule accordingly to your requirements, a recommendation would be to run this daily or perhaps weekly but keep in mind to set the notification range in the script to cater for the scheduling.
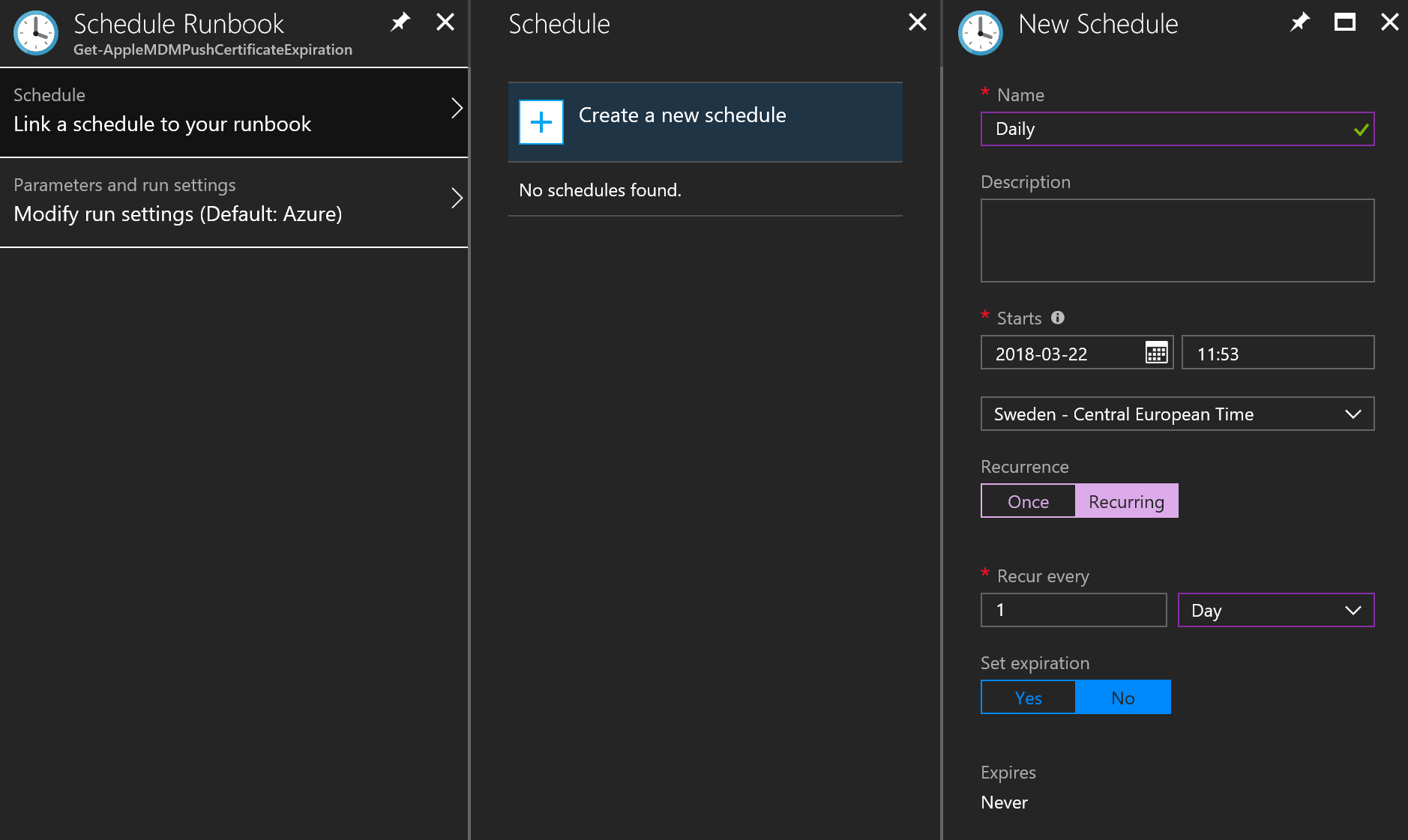
- Click Create once you’ve configured your schedule.
- This runbook does not have any parameter inputs, so skip Parameters and run settings and click OK.
Summary
Utilizing Azure Automation with PowerShell and Graph API is very powerful and I’ve just shown you another example for how we can setup a monitoring solution for the Apple MDM Push certificate. The same method used in this blog post could also be used for e.g. Apple DEP or VPP tokens.










Add comment