A little over two years ago, I wrote a blog post regarding the same subject that will be covered in this series. Since then much has changed in two years, like Microsoft Intune is now running on Azure and Azure AD Application Proxy has moved to the Azure portal, I felt that it was about time to bring up this topic again. Microsoft provides somewhat helpful documentation regarding the configuration and preparation steps required, but there’s a few pieces missing from their documentation that I’ll cover in this blog series. Additionally, the original blog post contained manual steps for installing and configuring the NDES server. Within this blog series, I’ll share a PowerShell script that I’ve created to automate that part.
Blog series overview
- Certificate deployment for mobile devices using Microsoft Intune – Part 1 – Overview
- Certificate deployment for mobile devices using Microsoft Intune – Part 2 – Certificate templates
- Certificate deployment for mobile devices using Microsoft Intune – Part 3 – Install NDES
- Certificate deployment for mobile devices using Microsoft Intune – Part 4 – Install Intune Certificate Connector
- Certificate deployment for mobile devices using Microsoft Intune – Part 5 – Deploy SCEP Certificate profile
Certificate deployment on mobile devices
Companies and organizations that are investing in Microsoft Intune for Mobile Device Management most often have the need to enroll certificates to their mobile devices when deploying for instance Wi-Fi or VPN profiles. Mobile Device Management products, such as Microsoft Intune, supports deployment of SCEP Certificate Profiles to distribute certificates using the SCEP protocol on mobile devices such as Android and iOS for instance. SCEP stands for Simple Certificate Enrollment Protocol and is a industry wide technology that was developed to simplify the distribution of certificates. Behind the scenes, a service called NDES (Network Device Enrollment Service) that is running on-premise communicating with a Certificate Authority allows mobile devices running without domain credentials to obtain certificates using the SCEP protocol.
Below is an illustration of an example environment that’s using Microsoft Intune together with the required on-premise infrastructure to distribute certificates to mobile devices.
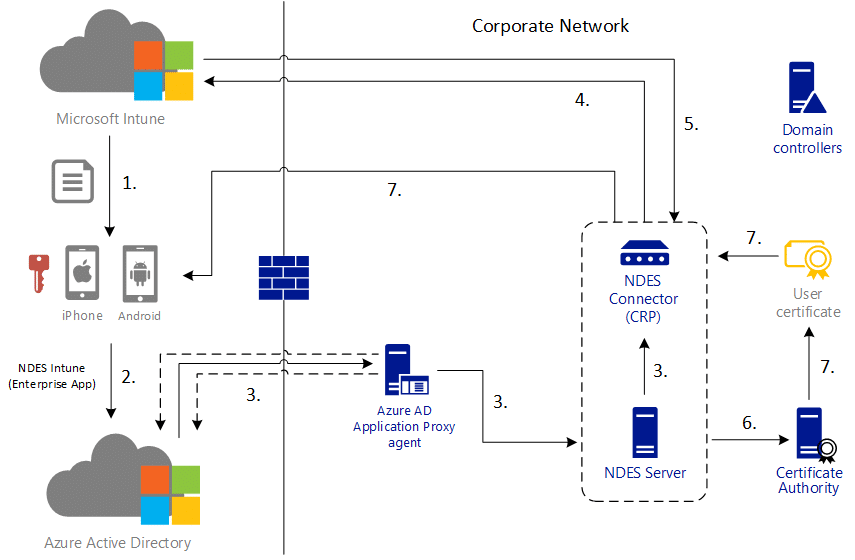
Here the administrator has assigned a SCEP Certificate Profile to mobile devices that contains an external URL for where to contact the NDES server. This URL is published using Azure AD Application Proxy that allows publishing of internal applications without the need of firewall openings. Since the NDES server would need to be made available publicly, you have several options to accomplish that. You could for instance install a Web Application Proxy (WAP) server and make that internet facing, use any kind of 3rd party load-balancing equipment like for instance Citrix NetScaler. Azure AD Application Proxy leaves a much smaller footprint in your environment however. This technology uses an agent that you install on a member server in your on-premise environment and it then operates much like a reverse proxy, allowing you to publish internal services externally.
Ronny de Jong originally published an blog post series quite similar to the one you’re reading right now. I’ve updated his original illustration with Azure AD Application Proxy and a few more details that should hopefully make it easier to understand what’s going on when a certificate is distributed to a mobile device. If you want to read Ronny’s original post, check it out here:
On-premise infrastructure requirements
Distributing certificates to mobile devices require a few on-premise infrastructure components as shown in the above illustration. Below is a list of the components that
- Internal PKI
- An internal PKI (Public Key Infrastructure) is required for issuing the certificates consisting of an Enterprise Certification Authority (CA) that runs on an Enterprise edition of Windows Server 2008 R2 or later
- Network Device Enrollment Service (NDES) server
- A domain joined member server running on Windows Server 2012 R2 or later on the same domain as the internal PKI
- Intune Certificate Connector (installed on the NDES server)
- This connector installs the NDES policy module and acts as the Certificate Registration Point
- Member server for Azure AD Application Proxy
- Any on-premise server in your environment that will have the agent service running being responsible for the outbound connection to Azure
Resource references
This series contains a lot of information which have been gathered from various resources around the web. Here’s the main sources of information if you want to dig deeper into this topic:
- https://docs.microsoft.com/en-us/intune/certificates-scep-configure
- https://ronnydejong.com/2014/12/15/part-1-deploy-certificates-to-mobile-devices-using-microsoft-intune-ndes-overview/
- https://blogs.technet.microsoft.com/tune_in_to_windows_intune/2014/04/25/part-2-scep-certificate-enrolling-using-configmgr-2012-crp-ndes-and-windows-intune/
In the next part we’re going to get into the configuration part for the required certificate templates and some prerequisites for the rest of this series.









Hi Nickolaj, do you have the part 5 and 6 available yet? The guides are very useful.
Just a note that event though you can install NDES role on server core, you cannot complete the configuration because the NDES connector requires IE to be installed.
Looking forward to the rest of the guide, are you planning to finish it?
Great post, as always Nickolaj. Question, if you want to design this as a HA-solution how many of each servers would you use?
2-3 issuing CA
2 x NDES
2 x pfx…then also installed on NDES?
Thanks Nickolaj, Perfect Follow of the Guide line