If you are in the process of migrating to modern management and are used to the on-premise world, things can be a bit daunting at first when getting familiar with where to set settings in the Intune portal. This post is to help those making this move, with practical examples of what the different methods used within Intune to manage Windows 10.
Series Links:
Managing Windows 10 with Microsoft Intune – Part 1 (MDM Profiles)
Managing Windows 10 with Microsoft Intune – Part 2 (CSP Policies)
Managing Windows 10 with Microsoft Intune – Part 3 (ADMX Templates & Workarounds)
The Path To Modern Management with Intune
Traditionally we have had group policy, something which has been around since the days of Windows 2000 Server and the birth of Active Directory. Over the years, group policy evolved, changing from ADM to ADMX, adding a central store and ultimately some would argue, becoming bloated, with literally thousands of configurable options. Group policy does of course though do one thing well, it gives you the ability to manage every aspect of both Windows and the applications running on top of it.
The thing is of course that Intune is a constantly evolving platform, on which the foundations and the continued expansion are driving directly by customer feedback. Over the part six month’s in particular, there has been huge growth in the ability to deploy and manage applications, along with more control over the underlying operating system. Now, more so than ever, the argument to make the switch to modern management is not so much of a should we, but a question of when.
To be clear though, when I say “modern management”, I am in no means suggesting that it is a big flip of the switch, co-management offers the best of both worlds of course and this will be the preferred path for many years to come. In this post though, we will cover how management of portions of your client PC estate can be undertaken using all of the available options in Intune.
MDM Device Profiles
If we roll back a number of years, and MDM profiles usually referred to the ability to manage settings on devices from Blackberry, Nokia (Symbian), Microsoft Mobile, iOS and Android. Today though the term has evolved, not only due to the fact that some of those before mentioned options are no longer with us, but also to include Windows 10, which by design shares code base with the now legacy Windows Mobile platform.
MDM profiles evolved over the years, to what we have today, a set of hundreds of configurable options. These include;
- Local User Security
- Drive Encryption
- Windows Defender Suite
- Windows Update
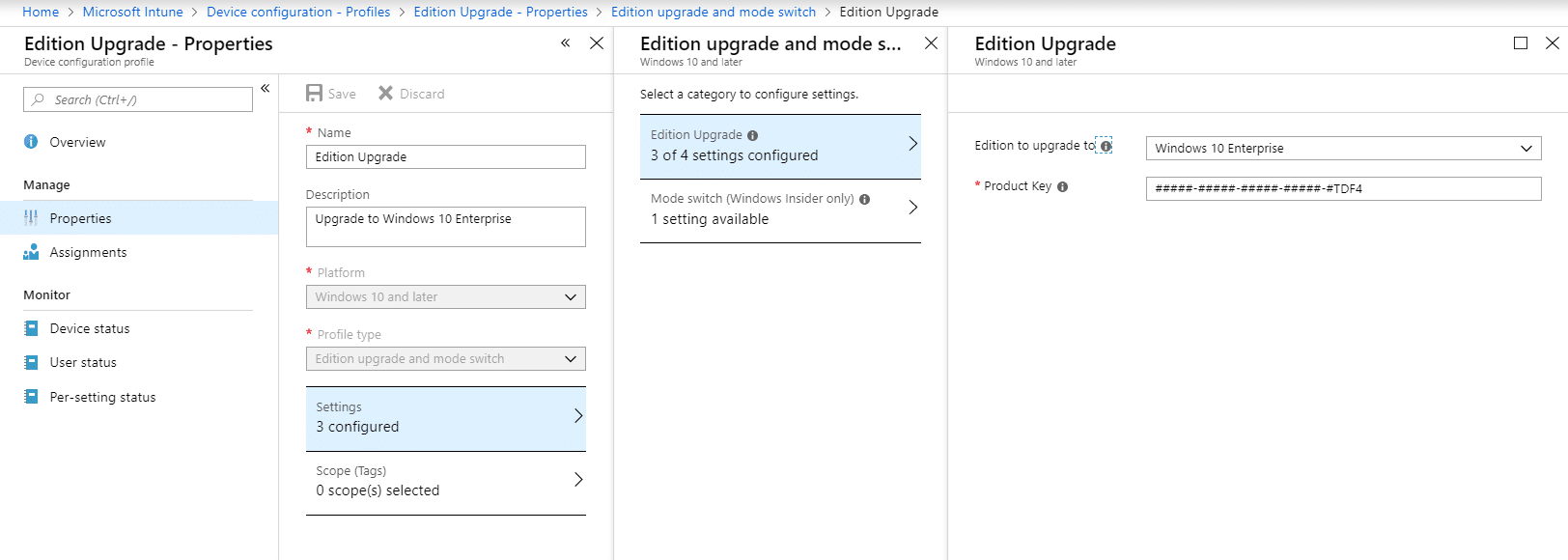
- Windows Edition
- Shared-PC Use
- Plus many many more
So let us step through how to apply settings to your Windows 10 device using an MDM device profile;
Endpoint Protection Profile
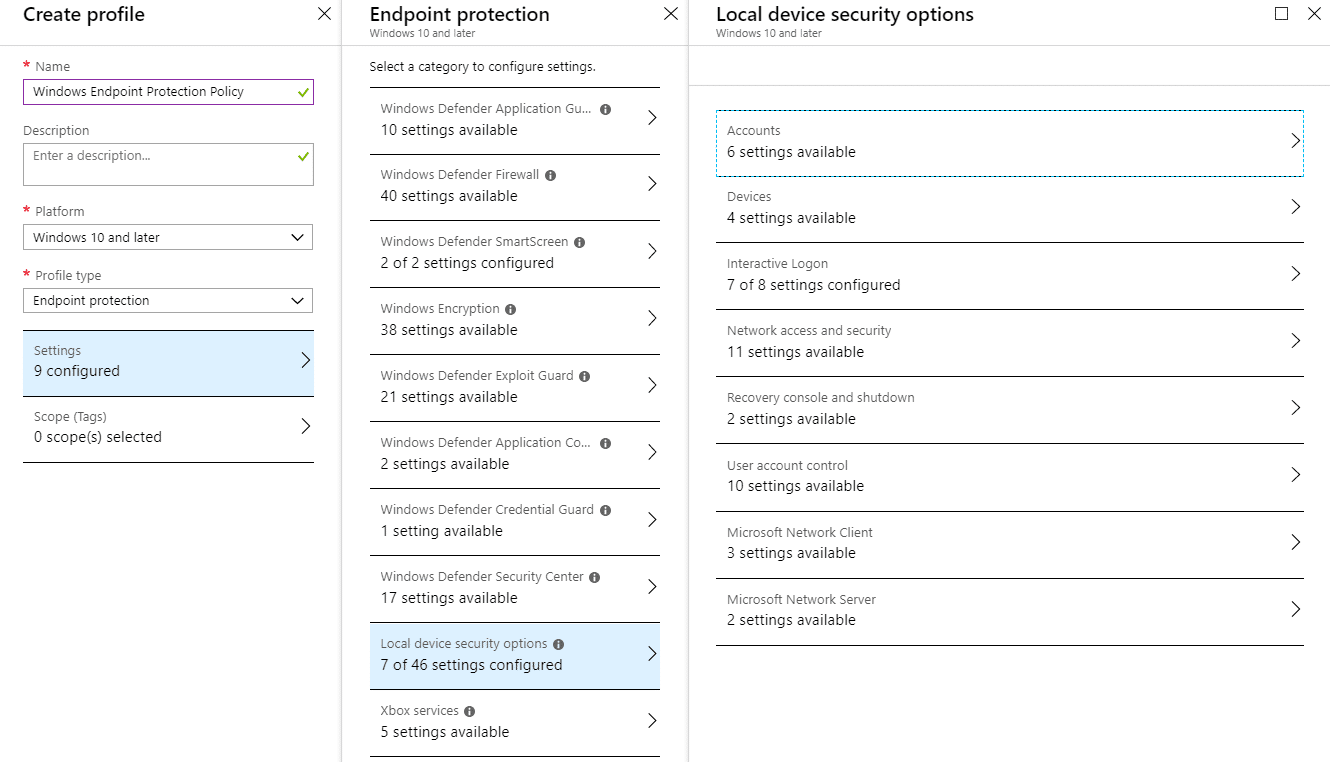
We will start by configuring a simple profile that will do the following;
- Block local administrator and guest account
- Block enumeration of local accounts
- Require secure elevation prompt for local users installing software
- Provide a login message for users
The first thing to do is to log into the Azure portal and select the Intune blade from the list. If you do not see Intune, simply go to all resources and add it as a favorite. With that in place, lets start;
- With the Intune blade selected, click on Device Configuration

- Click on Profiles
- Click on “+ Create Profile“
- Now we will need to select the type of profile
- Select the Platform as “Windows 10 and later“
- Select the Profile Type as “Endpoint Protection“
- Let us configure the lock screen experience for the end user now. Click on “Local device security options“
- Click on “Interactive Logon“
- Define settings similar to the ones outlined below

- Repeat this process for other area’s you wish to configure in the policy;



- Click “OK“
- Click “OK” again
- Now click on the “Create” button
Now you have created your first profile, we need to assign it to a device.
Creating a Device Group
Unless you want this profile to be assigned to all devices, you will need to create a security group and assign your device to that group. This is a straight forward process, so lets run through it here;
- Click on the Azure Active Directory Blade
- Click on “Groups“
- Click on “New Group“
- Enter a device group name, description and select “Assigned” as the membership type. You will see an option for “Dynamic Device”, this can be used with a query to automatically add devices to the group (further information can be found here – https://docs.microsoft.com/en-us/azure/active-directory/users-groups-roles/groups-dynamic-membership)
- Click on “Members“
- For this example I am going to add a device called “Desktop-71IL7C2”

- Click on “Select“
- Click on “Create“
Deploying an MDM Profile
At this point we now have a basic MDM profile and a device group to assign it to. Now we need to go back to the Intune blade and deploy the the profile.
- Click on the profile and go to “Assignments“
- Click on “Select Groups to Include“
- Type in the name of the group. In this example “Demo Devices”
- Click on the name of the group

- Click on the “Select” button
- Now click on “Save” to save the assignment
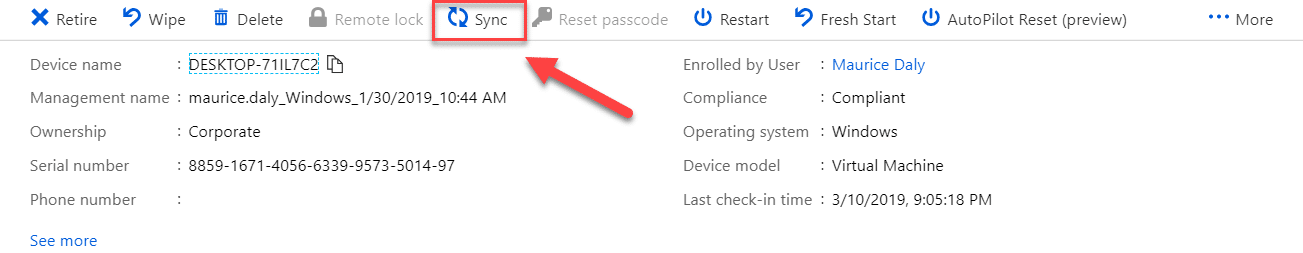
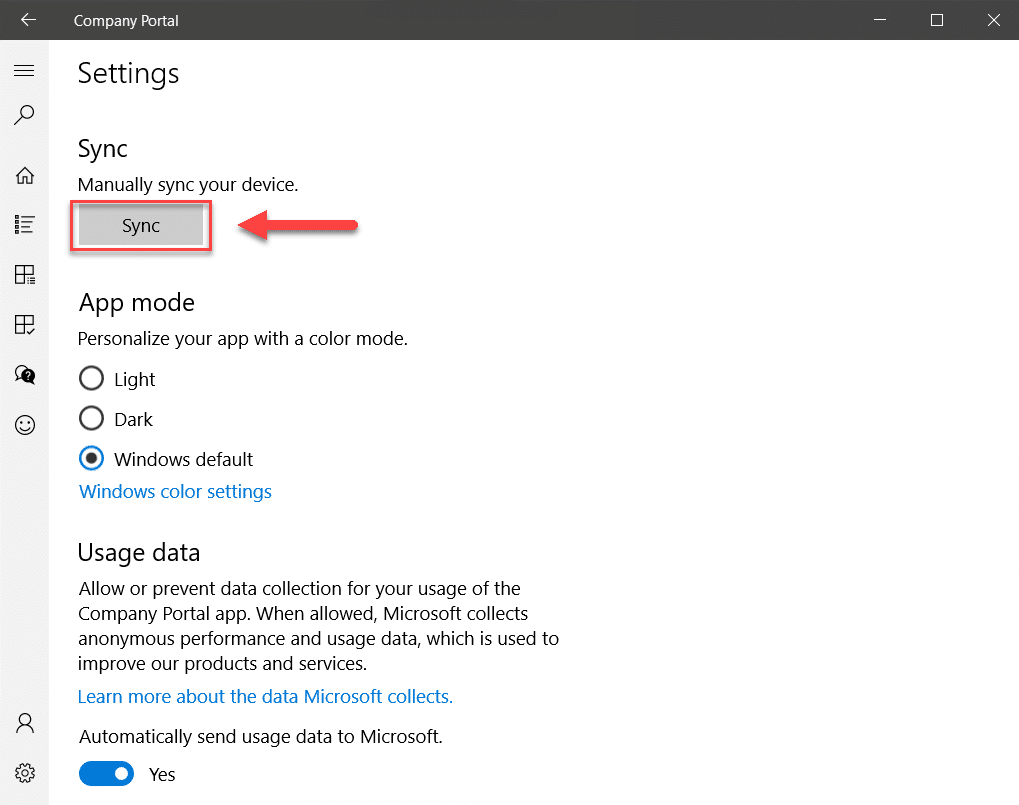
Sync Client Settings
The next step is to refresh the policies being applied to the device, this can be done either through the Intune portal or on the device itself;
Intune Portal
Company Portal App
Client Settings Applied
Once the profile is applied to the device, we can check the settings have applied;
Conclusion
In this part of this multi-part series, you should now have a basic understanding of how to deploy settings to your Intune managed device using MDM profiles. In part 2 we will focus on CSP and Administrative Templates (ADMX).
Thanks for reading.













Add comment