FIDO2, Multifactor Authentication, passwordless, Windows Hello for Business, Microsoft Authenticator, Security keys and a whole bunch of other fancy security words are taking the spotlight these days, and with good reason too!


In a time where targeted ransomware attacks are the norm rather than the exception, a password is no longer enough to protect your company’s data.
Actually, the experts say that we should try to get rid of passwords altogether!
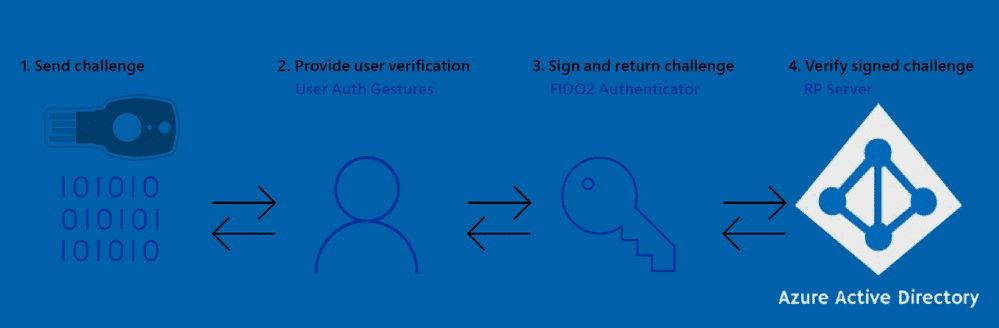
And this is where the FIDO2 capable security keys come into play, the FIDO standard (Fast IDentity Online) is rapidly becoming the go-to standard for passwordless authentication, as the alliance grows stronger.
The concept of passwordless and the FIDO2 standard go hand in hand to enable the following security benefits:
- No more shoulder surfing.
- No more account hijacking.
- No more forgotten password requests in helpdesk (Forgotten tokens though…).
- No more password phishing.
- No more password reuse.
- No more typing “October2019#” several times a day (You should really talk to your boss about his password…)
- No more passwords!
I know it sounds Utopian and like “mission impossible” to some readers. But it’s an important journey to get started on – and the sooner the better!
If you are still on the fence about this whole passwordless business, then I suggest you look at the official video and whitepaper from Microsoft on the subject of going passwordless.
So put on your your boots, and let’s get this journey started…
The journey begins
Being a big fan of Azure AD and all the security features that it empowers me with, I thought that it would be wise to be ahead of the curve and test a token based passwordless existence on my own tortured user accounts.
As I have many user accounts with different customers, and some accounts that span multiple tenants, it’s perfect for getting some real world experiences to share.
A bit of of background; So I started this journey after seeing this blog post by Michael Niehaus on his blog oofhours.com about his tests sign-in on a Windows 10 device with a FIDO2 token, based on guidance by Alex Simons.
“Cool stuff!” I thought to my self…
But with cool new stuff comes new questions…
One question in particular came to mind: Which security token should I buy?
And after buying one, I had a whole bunch more come up…
To save you and others a few headaches, I have tried to sum up some of the data you might need in order to make a qualified decision on how to start your own Passwordless journey.
NB: I will only be dealing with enterprise use with Microsoft Azure AD, and won’t be covering the technical setup details, only linking to relevant information.
The first bunch of requirements
These are my experiences with requirements for enabling FIDO2 support, and even beginning this journey.
Things change fast in this field, so by the time you read this, there might be support for other scenarios. Please comment if you feel the article needs updating.
Let’s do a nice and simple bullet list to start with:
- For now, you MUST have Azure AD in order to sign-in to your Windows 10 device with a qualified FIDO2 token.
Hybrid-Joined is in the works, and my hope is that we will see it in public preview after Microsoft Ignite 2019- Hybrid joined devices will have FIDO2 login support in the beginning of the new year 2020 according to an announcement from Microsoft here: https://techcommunity.microsoft.com/t5/Windows-IT-Pro-Blog/Expanding-Azure-Active-Directory-support-for-FIDO2-preview-to/ba-p/981894
- Your token of choice must support these specific FIDO2 CTAP protocol features.
- FIDO2 Security key authentication enabled in your Tenant
- Enable combined security information registration (preview)
- A browser that supports WebAuthN
- Windows 10 1809 or newer
To sum it up: If you have a Hybrid-Joined environment or Azure AD registered only devices, then you are stuck with only using passwordless on websites, this is enabled by support for WebAuthN in the browser (NB. All browsers aren’t quite there yet).
Official Microsoft guidance on how to enable all these services has been followed in order to do my testing – this blog post series is not about how to configure everything, instead I tried to focus on some real world experiences.
The first few hurdles
Registering keys in Azure AD turned out to be really simple after enabling the new user registration experience, which gives you access to the new mysignins portal, but the user experience is still at bit wonky at times.
If you have issues with initial MFA details for registrations on the site, make sure you don’t have a proxy or firewall blocking some microsoft sites, because I ran into this at some customer sites, and the page would just keep reloading forever.
My guess here is that the official Office 365 endpoints API does not include all the required FQDN’s and IP’s that this service uses.
And sometimes you might also encounter the following glitch, where you will be notified “Sorry, we can’t sign you in”, but after two seconds it will sign you in anyway, which is annoying.
If the message continues for more than a few seconds,then they really can’t sign you in.
Once you are in, you are golden, and you should be able to work with the key registration process.

Now I also had some issues with getting the key tested with Windows 10 sign-in…
My test machine was loaded up with Windows 10 1903 with the latest updates, but I had to refresh it (re-install) in order to get the “FIDO security key” option on the lock screen.

The token vendors
At launch, Microsoft announced that they partnered with Feitian Technologies, HID Global, and Yubico for Security Key support in Enterprises, others have since joined…
During the last few months I have acquired a bunch of these tokens for testing.
Let’s take a look at the list of vendors that I have been able to acquire a key or two from. And some important facts about them…

- Yubico
- Swedish / US based vendor.
- Microsoft partner at launch of FIDO2 support in Azure AD.
- FIDO2 Certified (Level 1)
- Wide range of keys available
- Web shop for direct purchase (International shipping).

- eWBM
- Korean / US based vendor.
- Member of the Microsoft Intelligent Security Association as of October 2019
- Has integrated bio-metrics support.
- FIDO2 Certified (Level 2)
- World’s first and only FIDO2 Level 2 security key vendor (As of writing)
- Web shop for direct purchase (International shipping).

- Solokeys
- US based vendor.
- Crowdfunded project.
- “Hackable” (in a good way)
- First open-source FIDO2 key.
- Not really a passwordless key according to their faq.
- Web shop for direct purchase.
The Yubico keys
- Yubikey 5 NFC (USB-A)
- Yubikey 5C (USB-C)
Thanks go out to Peter Selch Dahl for providing me with these puppies after I got turned down for the Microsoft starter kit by Yubico.
Let’s take a look at these two keys the shall we?


With full support for the required FIDO2 CTAP protcols from the get-go, these keys hold a promise of easy setup, and they look pretty.
Besides the different form factor and connectivity, these two keys are identical except that the USB-A model has built-in NFC which I did not manage to test that much on my iPhone, besides verifying that the NFC in the iPhone 11 Pro can read the key.
The USB-C key is very tiny, maybe a bit too tiny for my taste as it might easily get lost under the edge of the keyboard or at the bottom of a purse.
These keys have a ton of features, too many to bother you with in this post, but I encourage you to have a gander at the incredible list of features these keys have, many of wich I will not be covering in this article, as the focus is on using them with Azure AD to protect Cloud Accounts.
Overall these keys seem very durable and waterproof, but I’m sure you’r users will find a way to break them every now and then, so make sure to keep a few spares handy.
The eWBM keys
- Goldengate Security Key G310 (USB-A)
- Goldengate Security Key G320 (USB-C)
Thanks go out to Andrew Jun from eWBM for hooking me up with these nice biometric capable security keys.
Let’s take a look a these very special biometric capable security keys.

These keys are also endorsed by Microsoft for use with Azure AD, and as with the Yubikeys it looks promising for a smooth setup.
The keys are identical except they have different connectivity options, USB-C and USB-A.
They boast that this key can be used in place of the Yubikey, and give you added security with biometrics.
No support for NFC yet though.
The list of features on these keys are fewer than the Yubikey 5 series, but they seem more durable, and the biometrics are fast!
Though you might want to code in a few fingers from each hand, or you might get annoyed when using computer that have USB on the opposide sides of the computer you initially configured the key on.
Speaking of fingers, there is no “index” of them, which is maybe a Microsoft thing, (idk?) There are no drivers to install, so I am guessing that eWBM is not responsible for keeping track of the fingers that have been coded into the key.
Take a look at the features listed on eWBM’s official site for the Goldengate keys, which just also happen to bee the worlds first FIDO2 Level 2 certified keys (check out what the levels mean on the official FIDO alliance page, it could be very relevant for your decision making process).
Like the Yubikey these are also waterproff and a good size like the Yubikey 5 USB-A key.
The Solkeys key
- Solo Tap USB-A (NFC)
This one was on my own dime, so I chose not to go with more than one key.
Let’s take a look at the only Open Source FIDO2 key that I know of.

This key has gotten a lot of good reviews after breaking through with their kickstarter campaign – but Microsoft does not officially support them, and they don’t rank high on the membership listings on the FIDO Alliance site.
I thought I would by one to test it out against Azure AD, because it was Open Source and “hackable”.
It does have some caveats thought, which are listed in the Solokeys FAQ.
Be aware, that this key is not very robust and your user will break them once a week!
So it might only be financially feasible as a BYOK (Bring Your Own Key) to work.
But I bet some of you will appreciate the real “push” button on this key, and the fact that it has NFC support like the Yubikey (but only really usable on Android phones).
The list of features for this key can be found here on their kickstarter page:
https://www.kickstarter.com/projects/conorpatrick/solo-the-first-open-source-fido2-security-key-usb
The end of part 1
That’s it for part one of “Passwordless journey with FIDO2”.
If you feel like sending some keys to me for testing, please DM me on Twitter @michael_mardahl and I will extend the series with more parts.
Next part : Passwordless journey with FIDO2 – Part 2 – Usage experiences









Hello Michael,
Like you, the security key option is missing on the lock screen, but reinstalling the Windows didn’t help. Using the key to access Microsoft web apps works as expected.
Any idea?
Hi Leo,
You should try with the newest feature release of Windows 10, and make sure that it is not hybrid joined, only joined to Azure AD, using an account that is not synced from on-prem.
Then try and go through the pre-requisites again. There are alot of good articles out there about how to actually enable this.
https://oofhours.com/2019/08/30/sign-in-to-azure-active-directory-with-a-fido2-key/
Hello Michael,
Thank you for your response.
My test PC is not a hybrid joined one, it’s a test PC joined only to Azure AD. I’ve also enabled the security key on Intune.
I read the article you told me but I still don’t know what I did wrong. I’ve also read Microsoft official docs so many times already… *shrug*
Hi Leo
This is the way sometimes with preview features 🙁
Is your account also a pure AAD account, and not synced from on-prem AD ?
The feature is currently only for pure cloud environmnets I think, so mixing hybrid user with aad joined machine might not be supported, and there are certainly no good docs covering that topic.
Hello Michael,
Thank you for the response.
The Azure account is also purely a test account made specifically for this passwordless test 😀
If you want I can create an Azure admin account for you just to see if I did something wrong.
It’s about to drive me crazy 😀
I think the best thing would be to add a support case with microsoft.
Or you can contact apento.com and we can get you setup as a customer.
Good article