Conditional Access and multi tenancy can be tough on anyone used to “the old ways”…
As a consultant, I spend a lot of my admin time in other tenants that my own. And as such, I find it extremely useful to take my identity with me.
Azure AD makes this easy, by allowing my customers to on-board me as an external user through a simple invite.
Afterwards they can grant me the permissions I require and I am good to go.
An invited identity is still a separate identity
But… (yes there is a big ol’ “but” here)
If your customers are like mine and like having a secure Azure AD Tenant, then they will surely require even external users to authenticate with MFA.
Again Azure AD makes this pretty painless, and I am prompted to give out some extra details for Multi-Factor Authentication on-boarding of my external user.
The experience is that this is seemingly happening in my own tenant because I will see my own tenant’s branding during the initial logon. This can be confusing to some users that might think, “Hey, didn’t I already set this stuff up?”.
On Smartphones, it’s hard to see that you are feeding this data into another tenant, while on a PC, you might see another organisations name after the initial login.
Remember that Conditional Access can be evaluated in both tenants simultaneously, and you must pass both if that happens.
But that is not the real issue… Now the real pain here is that if you are like me and love the Authenticator App, you might end up with a headache the next time you change your smartphone or lose it completely.
It turns out that if you have gone through the setup of the Authenticator app in another Organisation, you might very well need them to activate the “Require re-register MFA” function if you change your smartphone. Not cool…
What to do…
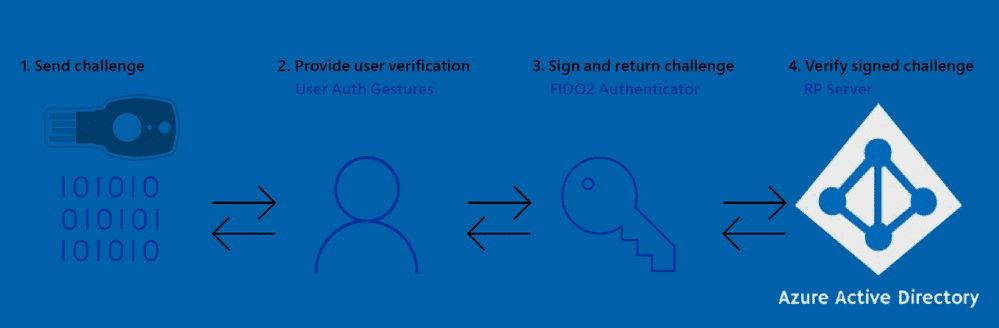
The solution here is simple… Use a FIDO2 key, or use the text message/phone call verification methods when registering for MFA as an external user in an Azure AD tenant. The latter has some security drawbacks, and you will need to evaluate the risk.
There is also the option of excluding Guests and External users from CA, but I don’t recommend it for obvious reasons…
https://docs.microsoft.com/en-us/microsoft-365/enterprise/identity-access-policies-guest-access
If you are using Microsoft Teams on your mobile, you might already have had to scratch your head on this one if your customer has enabled the enhanced registration process (preview), and you tried linking your Authenticator app during the registration process. Sometimes it just works, sometimes it does not – troublesome to say the least.
Final Words
As always, these are just my thought, and I share them freely for your own evaluation. Please don’t hesitate to “follow” and reach out to me on Twitter @michael_mardahl if you face similar issues, or have feedback/corrections.










Add comment