At first, I hope you all enjoying our solutions about Update Compliance, AppLocker, and Enhanced inventory reporting.
When we implement these solutions to our dear customers, we often get this question:
Who has access to these data and reports? And how can we assign permissions?
Well… we can find the answers in Microsoft doc.
Manage Log Analytics workspaces in Azure Monitor – Azure Monitor | Microsoft Docs
Designing your Azure Monitor Logs deployment – Azure Monitor | Microsoft Docs
Workspace-context and Resource-context
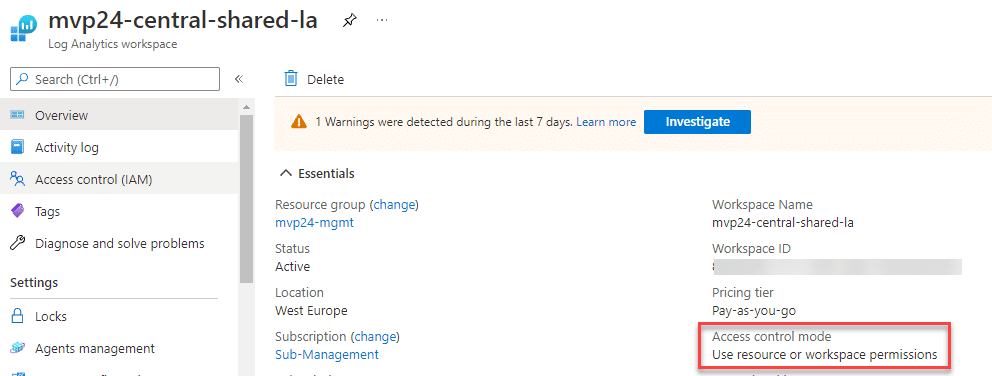
By default, when we create a new Log Analytics workspace, the access control mode is “User resource or workspace permissions”. With workspace-context, you can view all logs in the workspace you have permission to. Resource-context is when you access the workspace for a particular resource, for example, Azure Virtual Machine, Azure Automation account, etc. When we are using Update Compliance, AppLocker, Enhanced Inventory, or Intune diagnostics logs, these are using workspace-context access control (you don’t need to change the default setting), because these solutions are only using workspace logs, they aren’t Azure resources
Sure you can assign Log Analytics Reader role for the resource group to the user, that will work, but too much access still in my opinion. Some customers might be using one central shared Log Analytics Workspace to collect all the logs, so giving Log Analytics reader role to users, will give users permission to access all these data.
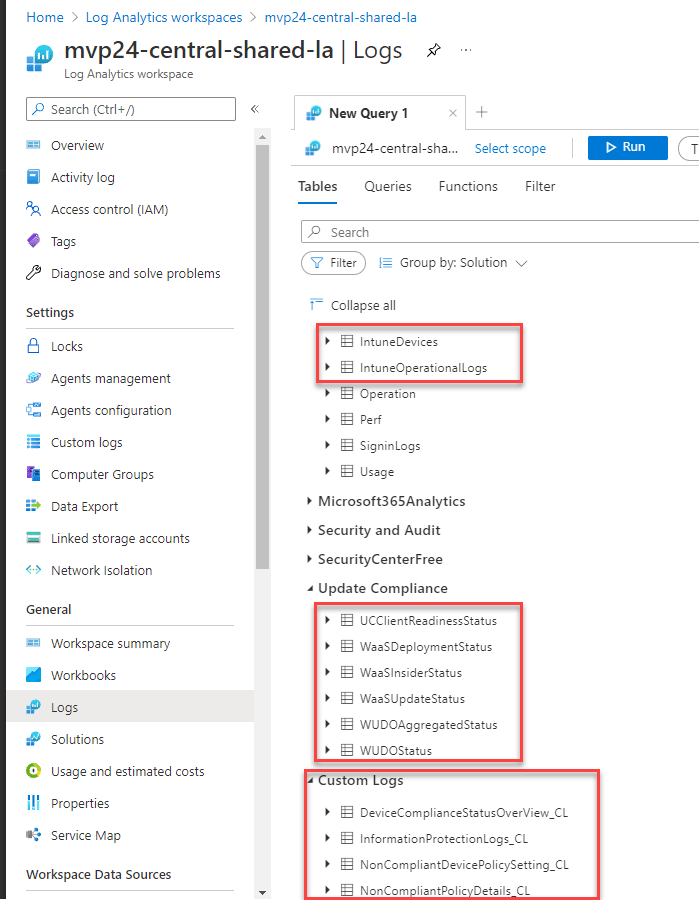
Let’s say you have all these log data sent to the same Log Analytics workspace, and you want to allow specific users to access specific sets of data or workbooks, what should you do? Use custom role! In the example here, I only want to allow users access to Intune logs, Update Compliance log, and custom logs
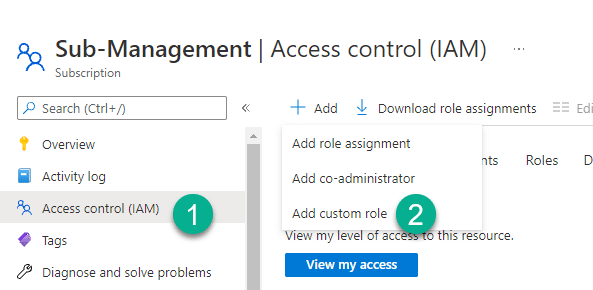
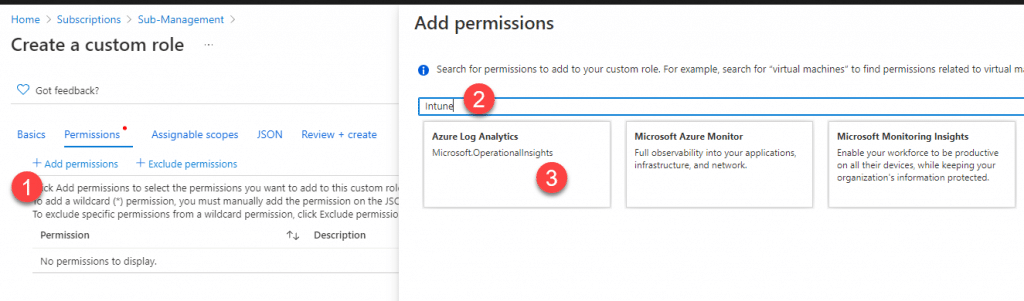
Step 1: Create a custom role
Chose your Azure Subscription, in Access control (IAM), add a custom role
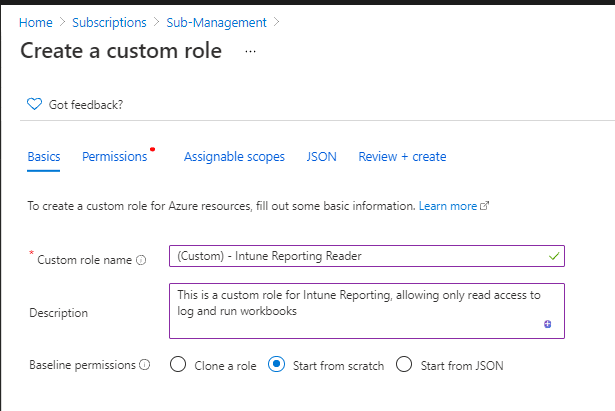
Give it a custom role name, write a good description.
Chose Add permissions, type example Intune in the search field, if you want to give permission to other data tables, type the table name in the search field. Then chose Azure Log Analytics
We should see all the Intune Diagnostics logs in the list, choose those logs that you wish to give permission to users. Then click Add
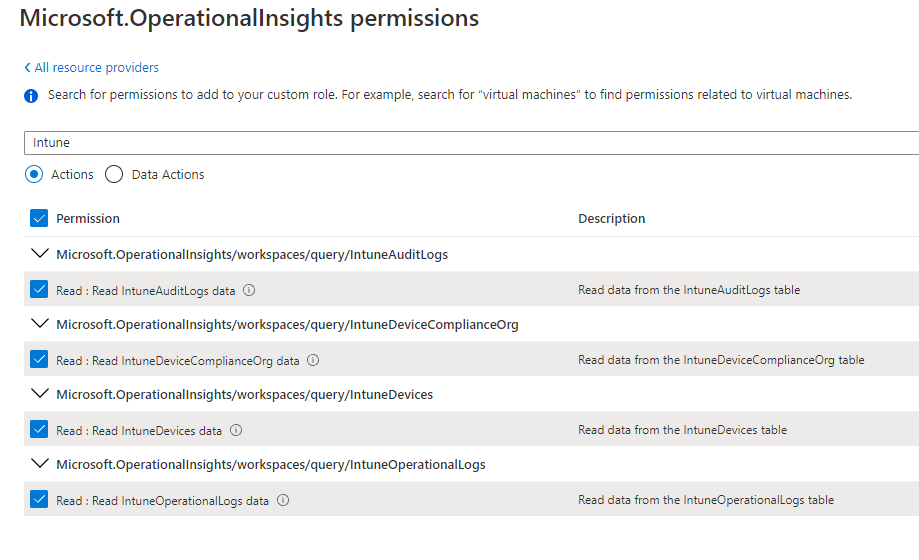
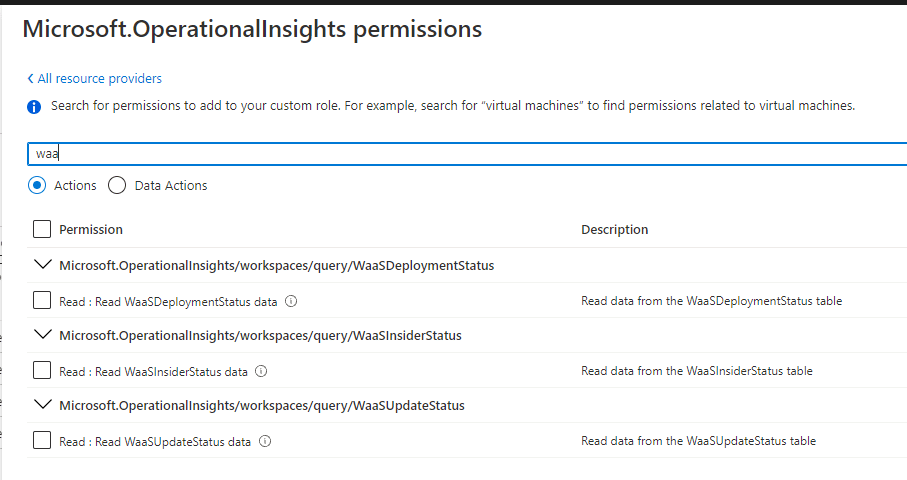
Continue to search other logs from Microsoft.OperationalInsights that you wish to have
IMPORTANT: You need to add these two permissions as well
- Microsoft.OperationalInsights/workspaces/read
You need this permission to enter the workspace blade in the portal - Microsoft.OperationalInsights/workspaces/query/read
You need this permission to query logs using any interface, example workbooks - Microsoft.OperationalInsights/workspaces/query/Tables.Custom/read
If you want to allow user have permission to custom logs as well, this will give read permission to all custom logs
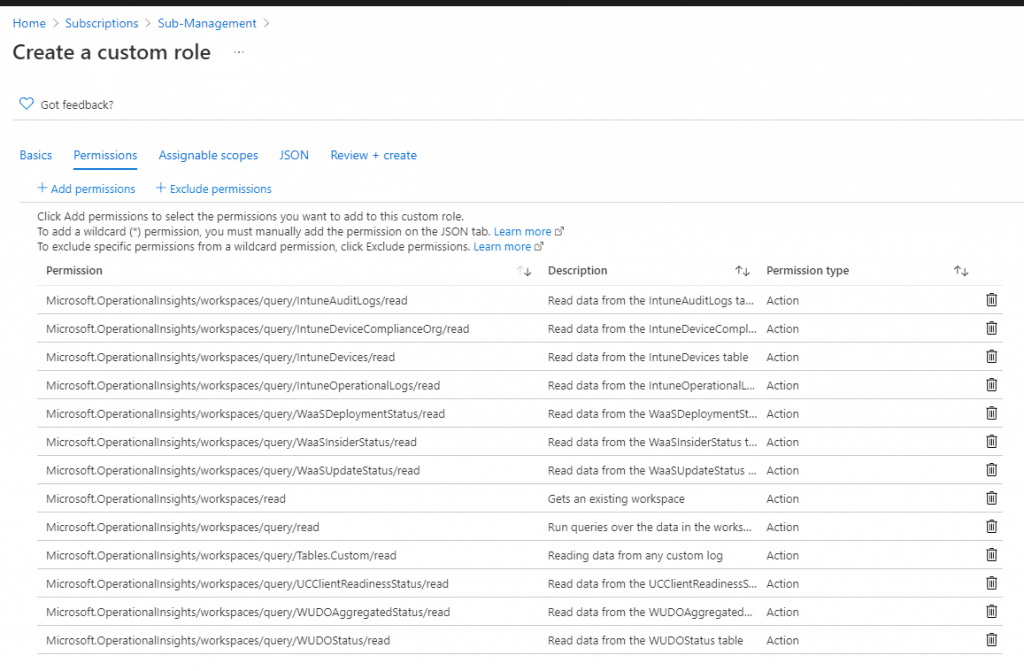
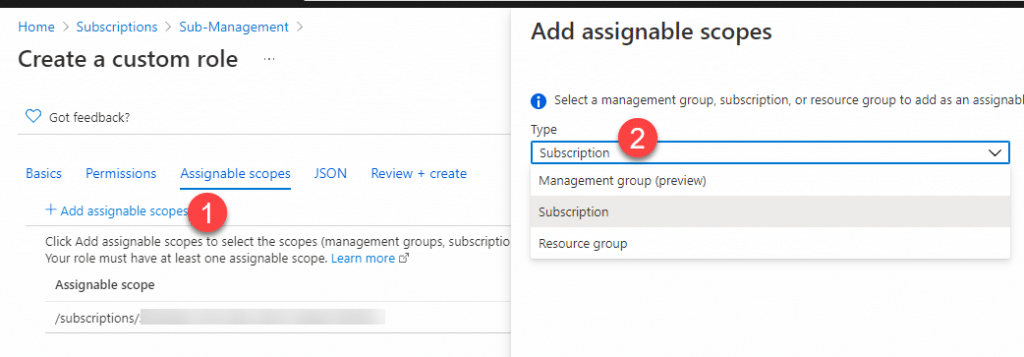
Next, chose assignable scopes. Then create the role
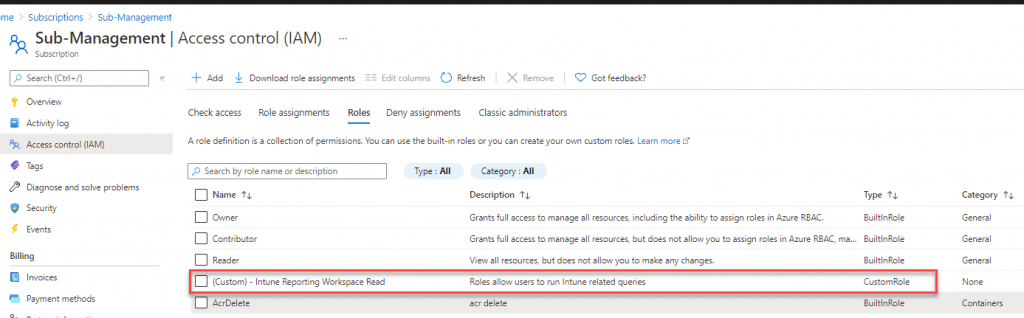
You should see the (Custom) – Intune Reporting Workspace Read role is created
Step 2: Assign roles for access Log Analytics
If you decide to assign this custom role to a resource group for a user, then the user will have access to all Log Analytics workspaces that are in the resource group, within those data tables. But if you would like to have better control, then assigns the role to a specific Log Analytics workspace.
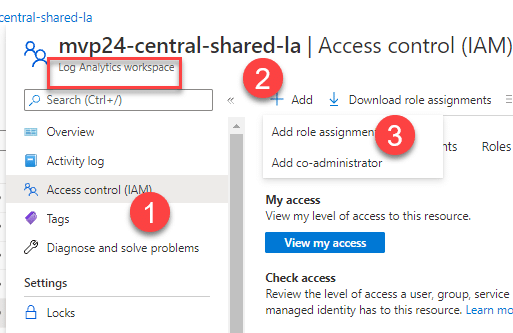
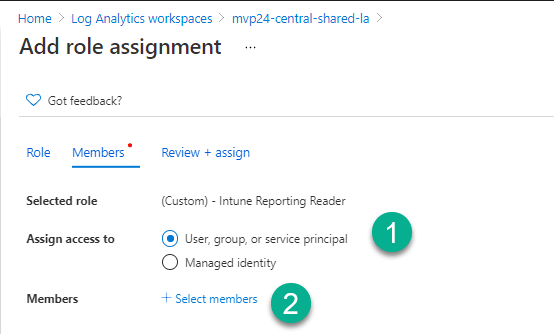
Chose the Log Analytics workspace, go to Access control (IAM) and add role assignment
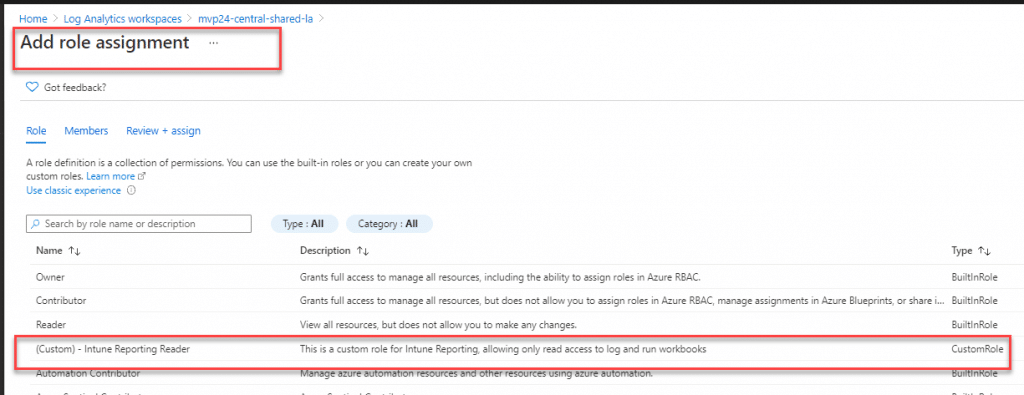
Chose the (Custom) – Intune Reporting Reader, click Next
Select members to who you wish to give access, then Review and Assign
Step 3: Assign roles for access Workbooks
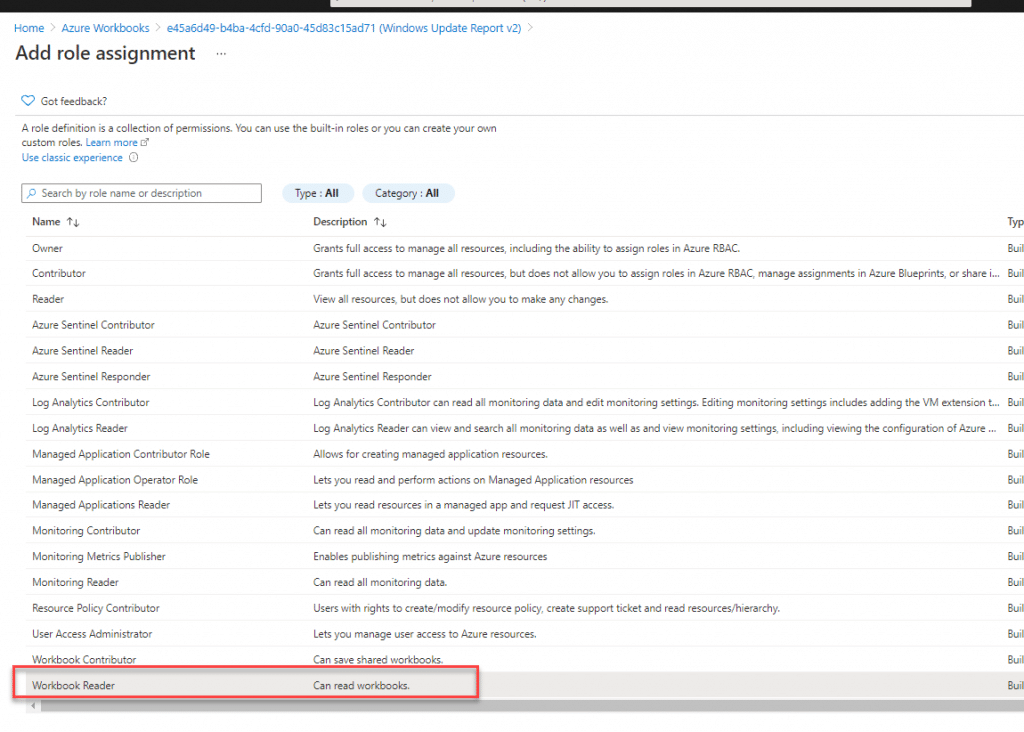
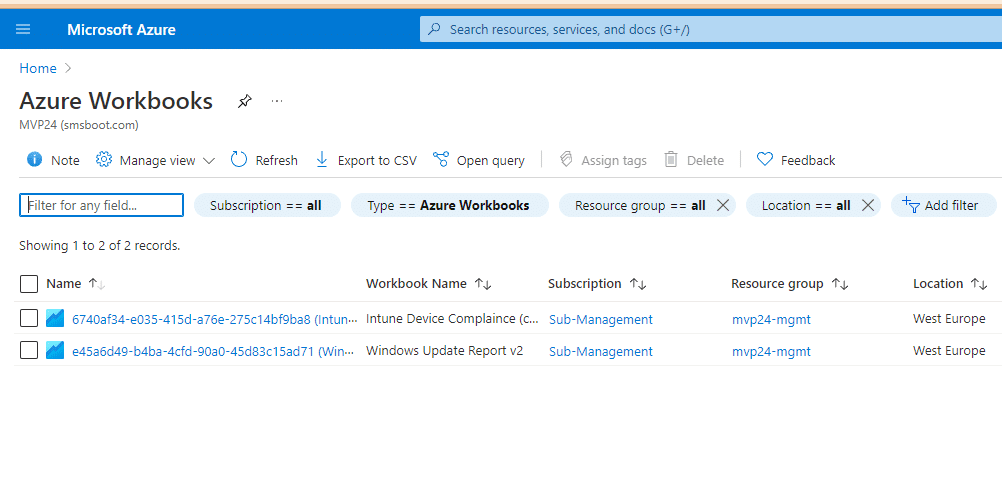
There is a build-in role Workbook Reader that allows users to read workbooks. If you want to allow users to read all the workbook in a resource group, assign this role to the resource group level. But if you only want to give access to particular workbooks, assign this role to the workbook level. Open Azure Workbooks, choose the workbook you wish to give access to, then add role assignment.
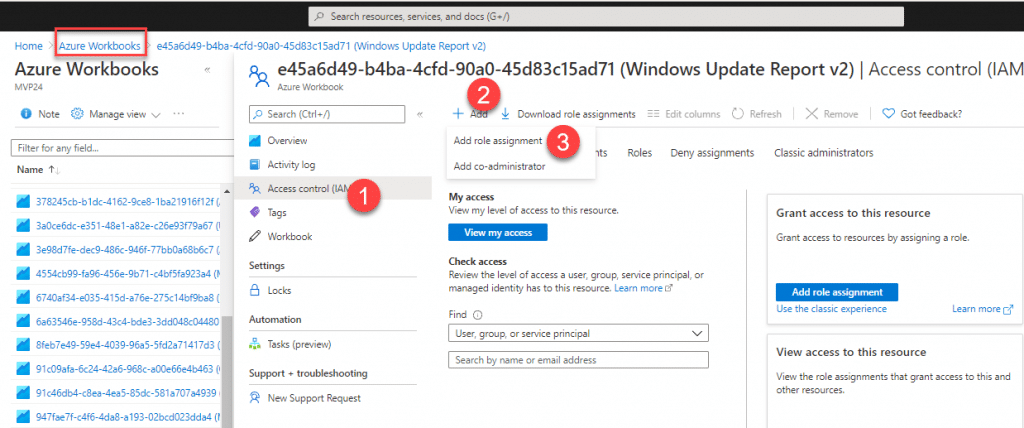
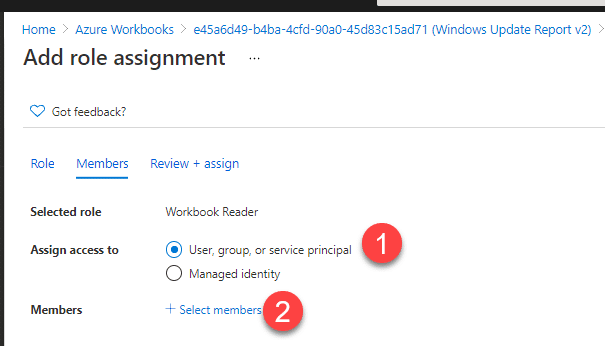
Chose Workbook Reader, then Next.
Again, select members that you wish to give access to, then Review and assign
Congratulation! You have now successfully configured these permissions! When the assigned user login to Azure Portal, or if you share a workbook link with the user, this user should be able to open the workbook. The user will be able to open the Log Analytics workspace, see all the data table list, but only those data tables that the user has access to will return query results. Other tables queries will return empty results.
By the way. You can also use json to create a custom role as well. Example json file
Save the json to example C:\Temp\IntuneCustomRole.json, remember to change your own Azure Subscription ID in the json file. To add the role to a subscription, run the following PowerShell command:
New-AzRoleDefinition -InputFile "C:\Temp\IntuneCustomRole.json"More information about custom roles. Azure custom roles – Azure RBAC | Microsoft Docs










It was very helpful and helped me to solve my issue.