Background
Before you can begin to process Update Compliance data from your devices, you must first ensure that they meet the requirements to participate in the Update Compliance process. Update Compliance uses Windows client diagnostic data for all of its reporting. It collects data for update deployment progress, Windows Update for Business configuration data, and Delivery Optimization usage data. Collected data is sent to a customer-owned Azure Log Analytics workspace.
Sometimes we observe discrepancies with actual vs expected Log Analytics Data. This can often be because the client is failing to meet the prerequisites to collect or send its diagnostic data. The aim of this post is to help you identify the reason(s) why your devices may not be sending telemetry in the expected way.
TL;DR The Check-UpdateComplianceSettings.ps1 script in this post will check that the device meets the prerequisites to send diagnostic data to Update Compliance. The script is designed to be run as a Proactive Remediation from Intune and is based on a similar script Microsoft provides for Update Compliance health and remediation
The solution outlined in this post is aimed at Intune managed devices. Microsoft do provide a script and some other binaries to check and remediate Update Compliance issues on devices. The Microsoft solution works well but I don’t like to deviate from Configuration Profiles if I can help it. IMO, there are already many configuration options in Intune and adding a script with binaries to configure Update Compliance draws me too far away from a position I am comfortable with.
Client Prerequisites
Windows 10/11
Update Compliance works only with Windows 10 or Windows 11 – that should be pointed out straight away. If we were to expand on that point, only the Pro, Education and Enterprise SKUs are supported. A compatibility matrix can be found below
| Windows 10 | Windows 11 | Windows Server | Surface Hub | IoT | Other | |
| Home | ❌ | ❌ | – | – | – | – |
| Professional | ✔️ | ✔️ | – | – | – | – |
| Education | ✔️ | ✔️ | – | – | – | – |
| Enterprise | ✔️ | ✔️ | – | – | – | – |
| Enterprise Multi-session | ✔️ | ✔️ | – | – | – | – |
Required Endpoints
The device must be able to contact certain endpoints for both authentication and sending of diagnostic data. It is important to make consideration for the following endpoints on your proxy or firewall
- https://v10c.events.data.microsoft.com
- https://v10.vortex-win.data.microsoft.com
- https://settings-win.data.microsoft.com
- http://adl.windows.com
- https://watson.telemetry.microsoft.com
- https://oca.telemetry.microsoft.com
- https://login.live.com
Required Services
It is difficult to single out individual Windows services and dependencies but specific to Update Compliance, the following services are required to be present and healthy
- wlidsvc (Microsoft Account Sign-in Assistant)
- diagtrack (Connected User Experiences and Telemetry)
Required Policies
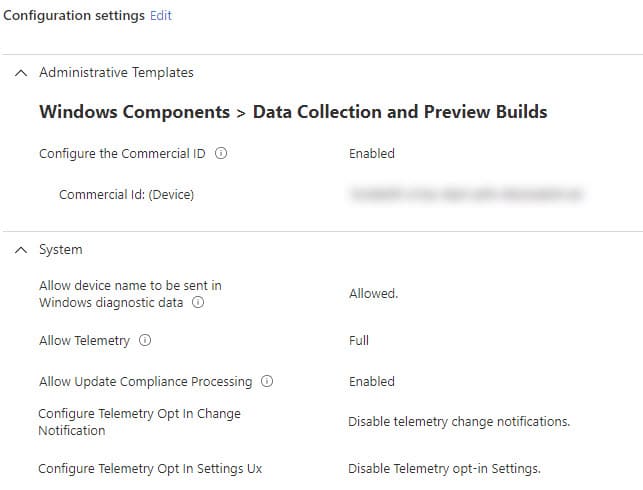
We can now use the Settings Catalog to configure all Update Compliance settings instead of Custom Configuration Profiles
- CommercialID
- AllowTelemetry
- ConfigureTelemetryOptInSettingsUx
- AllowDeviceNameInDiagnosticData
- AllowUpdateComplianceProcessing
Required Windows Configuration
Other information that is required to be present and healthy for the device to process and send diagnostics for Update Compliance
- SQMID The Windows SQM (Software Quality Metrics) device identifier
- UTC CSP The Win32CompatibilityAppraiser configuration service provider
Solution
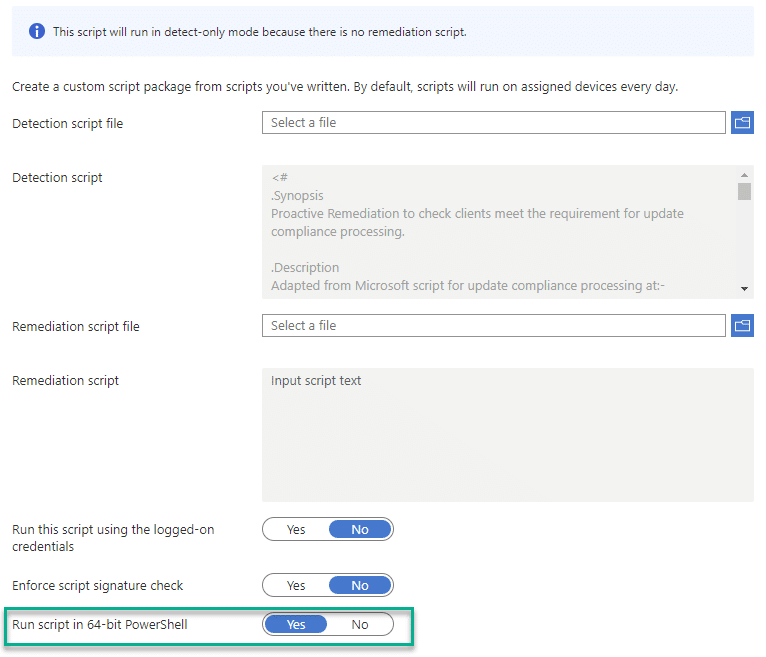
Check-UpdateComplianceSettings.ps1 is a script designed to be deployed as a pre-remediation detection script using a Proactive Remediations in Endpoint Analytics.
The script must be run in the SYSTEM context
When creating the Proactive Remediation, ensure you select to run as 64-bit PowerShell
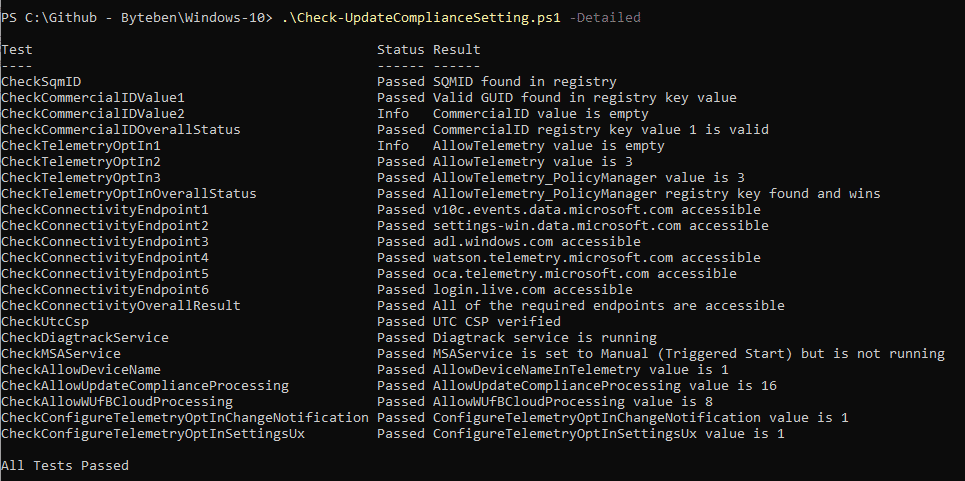
The script will check the following conditions on the device
- CheckSqmID
- CheckCommercialId
- CheckTelemetryOptIn
- CheckConnectivityURL(s)
- CheckUtcCsp
- CheckDiagtrackDLLVersion
- CheckDiagtrackService
- CheckMSAService
- CheckAllowDeviceNameInTelemetry
- CheckAllowUpdateComplianceProcessing
- CheckAllowWUfBCloudProcessing
- CheckConfigureTelemetryOptInChangeNotification
- CheckConfigureTelemetryOptInSettingsUx
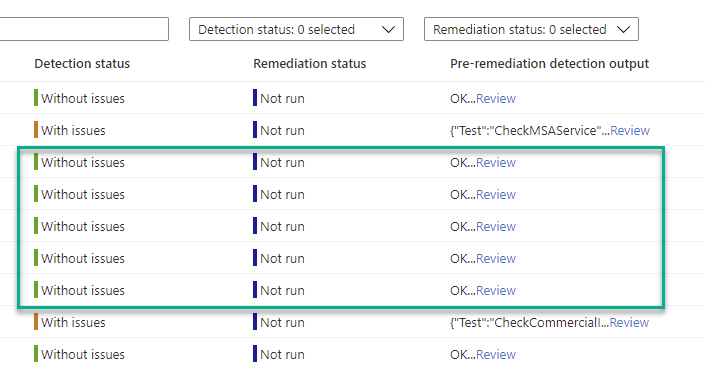
If some conditions do not PASS the tests successfully a hard fail is recorded and the pre-remediation detection script will exit with a code of 1 (Fail) and the failure(s) will be listed in the pre-remediation detection output column
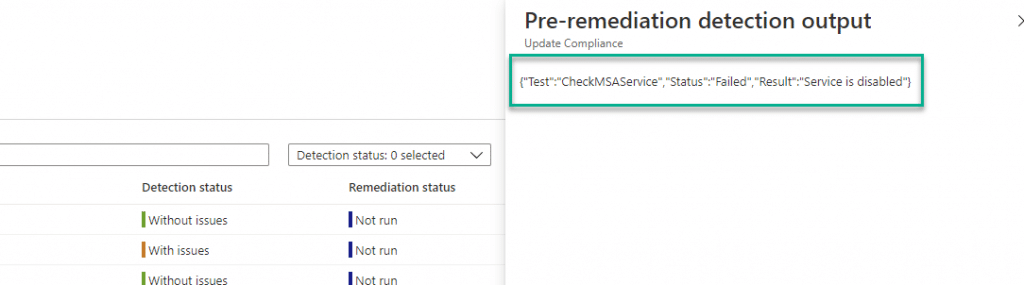
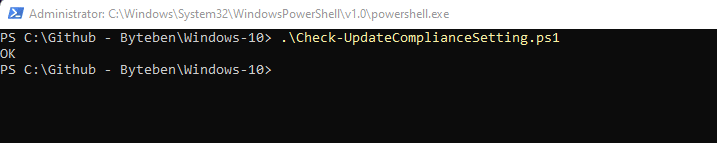
If all tests PASS successfully, OK will be listed in the pre-remediation detection output column
Interactive Option
You can view more detailed information if you run the script interactively on a client. You may wish to do this while troubleshooting an issue.
The script needs to be run in 64 bit PowerShell and in the SYSTEM context. You can achieve this by using PSEXEC (64bit) included in PSTools from Sysinternals
psexec64 -s -i C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe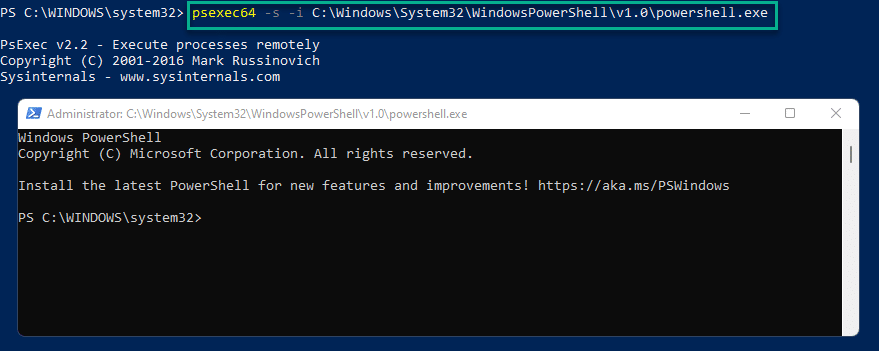
The script accepts 2 parameters
- Detailed – This option outputs the results in a table
- ExportJSON – This option outputs the results as a JSON.

Next Steps
We intend to ingest the device Update Compliance health into Log Analytics so we can compare any Update Compliance reporting anomalies with the last successful OK health status of the device from the proactive remediation.
Proactive Remediations are very versatile. This solution doesn’t contain a remediation script but we can see how powerful it can be just to collect information for inventory and troubleshooting.
Reach out if you need help, Ben.










Hi Ben, awesome idea. Eager to try it out.
Tried to implement, but when I want to add the detection script, I get the following error:
Selected file ‘Check-UpdateComplianceSetting.ps1’ must be between 1 and 200000 bytes.
The file I’ve downloaded is 417kb (417000bytes)
Have you seen this before?
Thks
Hey, thanks for the feedback 🙂
The script is only 30kb, it sounds like you are saving file as from GitHub which is saving it as a html? Wild guess though.
Try viewing the code as raw and copying to a new file or clone the repository using Github desktop and grabbing the file that way?
Good luck 🙂